Supernetting: Advanced Networking Concepts
250 likes | 278 Views
Explore the benefits of supernetting for efficient IP address management. Learn about assigning class C blocks and implementing superblock approaches. Discover practical examples and solutions in network configuration.

Supernetting: Advanced Networking Concepts
E N D
Presentation Transcript
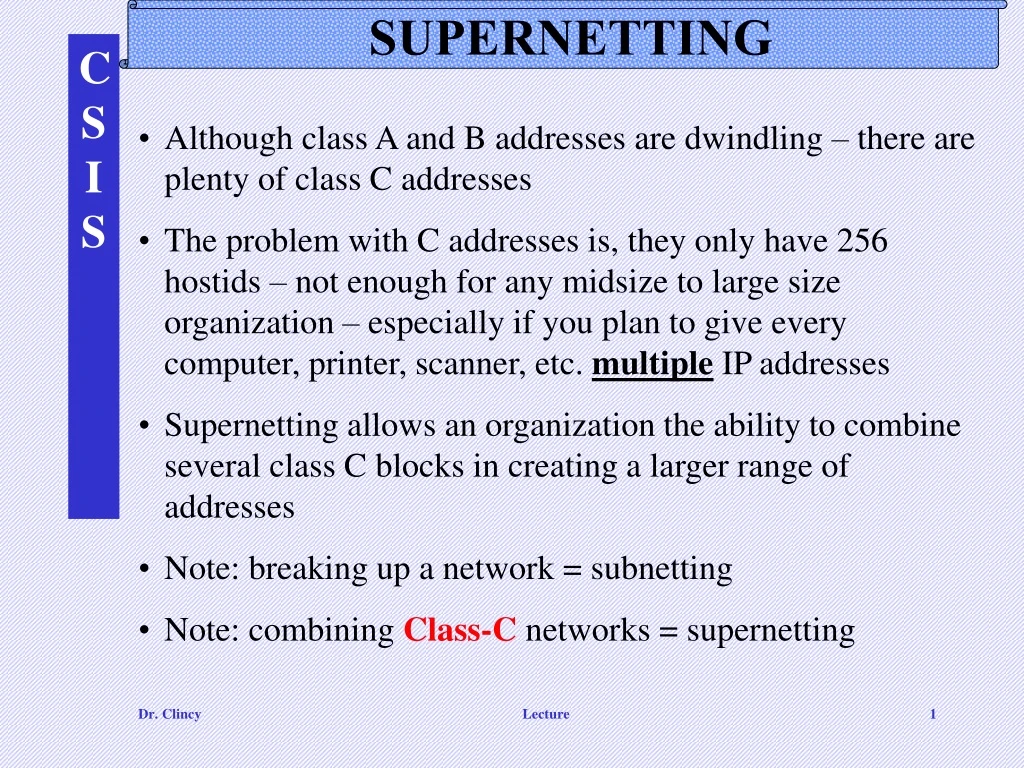
SUPERNETTING • Although class A and B addresses are dwindling – there are plenty of class C addresses • The problem with C addresses is, they only have 256 hostids – not enough for any midsize to large size organization – especially if you plan to give every computer, printer, scanner, etc. multiple IP addresses • Supernetting allows an organization the ability to combine several class C blocks in creating a larger range of addresses • Note: breaking up a network = subnetting • Note: combining Class-C networks = supernetting Lecture
Assigning or Choosing Class C Blocks • When assigning class C blocks, there are two approaches: (1) random and (2) superblock • Random Approach: the routers will see each block as a separate network and therefore, for each block there would be an entry in the routing table – a router contains an entry for each destination network • Superblock Approach: instead of multiple routing table entries, there would be a single entry. However, the choices of blocks need to follow a set of rules: • #1 – the # of blocks must be a power of 2 (ie. 1, 2, 4, 8 …) • #2 – blocks must be contiguous (no gaps between blocks) • #3 – the 3rd byte of the first address in the superblock must be evenly divisible by the number of blocks – ie. if the # of blocks is N, the 3rd byte must be divisible by N Lecture
Example 5 A company needs 600 addresses. Which of the following set of class C blocks can be used to form a supernet for this company? 198.47.32.0 198.47.33.0 198.47.34.0 198.47.32.0 198.47.42.0 198.47.52.0 198.47.62.0 198.47.31.0 198.47.32.0 198.47.33.0 198.47.34.0 198.47.32.0 198.47.33.0 198.47.34.0 198.47.35.0 Solution 1: No, there are only three blocks. Must be a power of 2 2: No, the blocks are not contiguous. 3: No, 31 in the first block is not divisible by 4. 4: Yes, all three requirements are fulfilled. (1. Power of 2, 2. Contiguous and 3. 3rd byte of 1st address is divisible by 4: 32/4=8) Lecture
Example 8 A supernet has a first address of 205.16.32.0 and a supernet mask of 255.255.248.0. How many blocks are in this supernet and what is the range of addresses? Solution • The default mask has 24 1s because 205.16.32.0 is a class C. • Because the supernet mask is 255.255.248.0, the supernet has 21 1s. • Since the difference between the default and supernet masks is 3, there are 23 or 8 blocks in this supernet. • Because the blocks start with 205.16.32.0 and must be contiguous, the blocks are 205.16.32.0, 205.16.33.0, 205.16.34.0………. 205.16.39.0. • The first address is 205.16.32.0. The last address is 205.16.39.255. • The total number of addresses is 8 x 256 = 2048 Lecture
Explain Supernetting Conceptually Back out this bit from netid into host id Causes these 2 blocks to combine as a single block Lecture
Variable-length subnetting • Suppose you were granted a Class C address – this mean you would have 8 bits to play with • Also, suppose you needed 5 subnets consisting of the following # of hosts: 60, 60, 60, 30 and 30 • If you used a 2 bit subnet mask – can get 4 subnets with 64 stations each (too big) • If you used a 3 bit subnet mask – can get 8 subnets with 32 stations each (too small) • What’s the solution ? Lecture
Variable-length Subnetting • Solution: used 2 subnet masks – one applied after the other • Could use a 2 bit subnet mask and get 4 subnets with 64 stations each - this would satisfy the three 60-host subnet requirement – therefore the subnet mask would be 255.255.255.11000000 (192) • We could then further divide one of the 64-host subnets into two 32-host subnets by applying this mask 255.255.255.11100000 (224) after this mask of 255.255.255.11000000 (192) is used Lecture
Ch 5 Classless Addressing Lecture
Guess What ? Classful Addressing is Obsolete However, understanding the classful approach will help you easily understand the classless approach Quickly explain classless vs classful (leave address aggregation for the routing topics) Lecture
CLASSLESS ADDRESSING • Recall the problems with Classful addressing – you have to get a predefined block of addresses – in most cases, the block is either too large or too small • In the 1990’s, ISP came into prominence – they provide Internet access for individuals to midsize organizations that don’t want sponsor their own Internet service (ie. email, etc). • The ISP’s are granted several B and C blocks of addresses and they subdivide their address space into groups of 2, 4, 8, 16, etc.. – blocks can be variable length • Because of the up rise of ISP’s, in 1996, the Internet Authorities announced a new architecture called Classless Addressing (making classful addressing obsolete) Lecture
Number of Addresses in a Classless Block There are two conditions Condition 1: the number of addresses in a block; it must be a power of 2 (2, 4, 8, . . .). A household may be given a block of 2 addresses. A small business may be given 16 addresses. A large organization may be given 1024 addresses. • Another Condition: • The beginning address must be evenly divisible by the number of addresses. • For example, if a block contains 4 addresses, the beginning address must be divisible by 4. If the block has less than 256 addresses, we need to check only the rightmost byte. If it has less than 65,536 addresses, we need to check only the two rightmost bytes, and so on. Lecture
Classless Subnet Illustration Netid subnetid Lecture
Example 9 Which of the following can be the beginning address of a block that contains 16 addresses? 123.45.24.52 205.16.37.32190.16.42.4417.17.33.80 Solution The address 205.16.37.32 is eligible because 32 is divisible by 16. The address 17.17.33.80 is eligible because 80 is divisible by 16. Lecture
Example 10 Which of the following can be the beginning address of a block that contains 1024 addresses? 205.16.37.32190.16.42.017.17.32.0123.45.24.52 Solution • To be divisible by 1024, the rightmost byte of an address should be 0 because any value in that first byte will be a fraction of 1024 (ie. 0 to 255). • To be divisible by 1024, the rightmost byte should be 0 and the second rightmost byte must be divisible by 4 because for every unique number in the second byte position, there exist 256 addresses in the first byte position that maps to it. To get 1024 addresses overall, you will need an increment of 4 in the 2nd byte position. • Therefore, the 2nd byte needs to be divisible by 4. • Only the address 17.17.32.0 meets this condition. Lecture
Mask • Recall the Classful approach, only given an IP – the user defined their mask • For the Classless approach, when an org is given a block, it’s given both the starting address and the mask – these two pieces of info defines the entire block • For classless case, instead of writing out the full mask, we just specify the number of 1’s in the mask and append it to the address – this is called slash notation or CIDR (classless interdomain routing) notation • For classless addressing, the prefix refers to the common part of the address (ie. network portion) • For classless addressing, the suffix refers to the varying part of the address (ie. host portion) Lecture
A block in classes A, B, and C can easily be represented in slash notation as A.B.C.D/ nwhere n is either 8 (class A), 16 (class B), or 24 (class C). Lecture
Example 11 A small organization is given a block with the beginning address and the prefix length 205.16.37.24/29 (in slash notation). What is the range of the block? Solution The beginning address is 205.16.37.24. To find the last address we keep the first 29 bits and change the last 3 bits to 1s. Beginning:11001111 00010000 00100101 00011000 Ending : 11001111 00010000 00100101 00011111 There are only 8 addresses in this block. Lecture
Example 13 What is the network address if one of the addresses is 167.199.170.82/27? Solution The prefix length is 27, which means that we must keep the first 27 bits as is and change the remaining bits (5) to 0s. The 5 bits affect only the last byte. The last byte is 01010010. Changing the last 5 bits to 0s, we get 01000000 or 64. The network address is 167.199.170.64/27. Lecture
Example 14 An organization is granted the block 130.34.12.64/26. The organization needs to have four subnets. What are the subnet addresses and the range of addresses for each subnet? Solution The suffix length is 6. This means the total number of addresses in the block is 64 (26). If we create four subnets, each subnet will have 16 addresses. Lecture
NETWORK ADDRESS TRANSLATION (NAT) Network Address Translation (NAT) allows a site to use a set of private addresses for internal communication and a set of global Internet addresses for communication with another site. The site must have only one single connection to the global Internet through a router that runs NAT software. The routers only 2 address: (1) the global IP address and (2) one private address Lecture
Address translation All packets leaving the network get assigned the global address as the source address (straightforward process) All packets coming into the network get their global destination address replaced with the appropriate private address (process is more involved) (explain this in the next ppt slide) Lecture
Translation Packet: From Private Network to Internet Keep in mind that, with in the private network, the original source address is a private address representing the original source in the private network. Just before the packet leaves the router, the router makes note of the GLOBAL DESTINATION ADDRESS and cross-references it with the PRIVATE source address before changing the private source address to the GLOBAL SOURCE ADDRESS Packet: From Internet Back to Private Network When the packet returns, the SOURCE ADDRESS of the packet is the original DESTINATION ADDRESS. The router uses the new source address of the packet in determining the private destination address – recall the address being cross-referenced Lecture
NAT Using Multiple Global Addresses NAT Router with One GLOBAL address can only allow One private host to access the same EXTERNAL host – with more global addresses, more private hosts can access the SAME external host A NAT Router with 8 global addresses can allow up to 8 private addresses (hosts) to access the SAME external host (simultaneously) – can create up to 8 separate connections To create a many-to-many relationship, a 5-column table (versus 2-column table) is needed in reducing uncertainty – by specifying port address and transport layer protocol Five-column translation table Lecture
An ISP and NAT An ISP serving DIAL-UP customers can conserve addresses by using NAT. NOTE: think of dial-up customers as being apart of the ISP’s private network before gaining access to the Global Internet. The ISP could assign a private address to each customer and when the customer leaves the private network, a translation would occur (like in ppt slide 11). Let an ISP with 100,000 dial-up customers be granted only 1000 global addresses - the ISP could assign private addresses to each 100,000 customers and the ISP translate the 100,000 source addresses for the outgoing packets with the 1000 global addresses Lecture