Evolving Ontologies via P2P: Introducing a Rating Methodology
250 likes | 339 Views
Explore solutions to P2P and Ontology problems, review unique rating approach, discuss enhancements for future cooperation.

Evolving Ontologies via P2P: Introducing a Rating Methodology
E N D
Presentation Transcript
Evolving Ontologies via P2P technology Introduction of a rating method
Purpuse of the visit • Share work • See if Trento and VU can cooperate in the future
Outline of this talk • Show some problems in the P2P and Ontology community • Show some solutions from literature for each problem • Show my solution • Open discussion about the solutions
Problem 1: Queries flooding the network The Gnutella approach from broadcasting queries to all their neighbors is very inefficient. A negative side effect is the inability to find rare items “find the 10th episode of Startrek voyager” Solution: Efficient Peer selection service
Solution 1: Hash ID’s (PASTRY, PAST, CHORD, CAN…) • Make a hash identifier of the content and move the this with the content to the peer(s) which identifier is the closest to the hash identifier • Every peer contains a table of their neighbours Problem: Very efficient routing mechanism, but it can’t handle partial matches and complex queries “find music from britney speers” (what probably must be “find music from britney spears”).
Solution 2: Content replication (Cohen et al., Freenet) • Copy content to places where the queries come from Problem: Result solving instead of cause solving the problem remains
Solution 3: Keyword reputation (NeuroGrid, Poblano …) • Peers learn and remember content of other peers e.g. Each peer contains a table with peer/keyword pairs accompanied with a rating (Poblano) Problem: A good solution on the mentioned problem. It also could be an algorithm on top of Pastry methods (just for searching and if the hash-id is found, locate the file). However it doesn’t find “All flatscreen monitors with a diameter > 15 inch ”
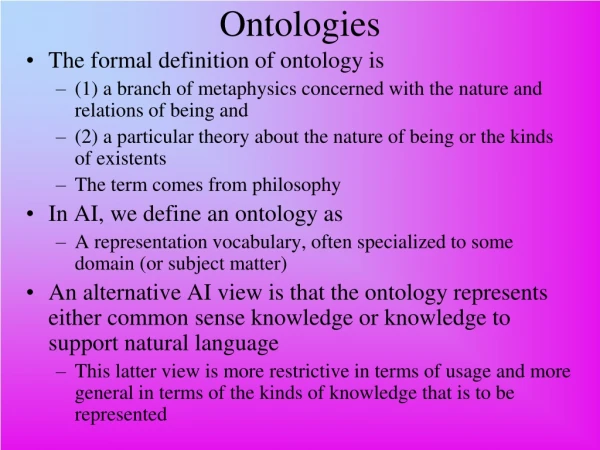
Problem 2:Variation of ontologies and lack of precision Different peers will use different, though overlapping ontologies. They have to deal with inconsistencies, homonyms, synonyms and sloppy definitions
Solution: Mappings between local ontologies & meaning negotiation • Automatic algorithm of meaning negotiation (Magnini et al.) • Mapping languages (CTXML [Bouquet et al.]) • Metadata infrastructure to annotate data with machine processable knowledge (Edutella [Nejdl, Decker et al.] Problems left: who is right? (even with mapping languages, the mapping is an opinion)
The LARiSSA rating methodology • Backbone of peer is a full-connected, directed graph structured in a class taxonomy • For each statement in the ontology: • Remember source • Remember date • Calculate rating
Problem 3: ontological drift Solution: Add timestamps to (incoming) information, and let them act like a ‘best before’ value (NeuroGrid [Joseph,2002]…in progress…) Problem: How to determine the devaluation function?
Other things:Licencing and dependancy • Open source • Platform dependance (Windows) • Producer dependence (.NET)
Other things:Listen to the users • Don’t think… If we build it, they will come Therefore another characteristic in the compare matrix is the success rate of the described systems
Protocols: Gnutella • File sharing protocol • Identifier are IP numbers • Broadcasting queries • When attaching, every peer responds with some information about itself • Own communication language • No security • Implementations: Limewire, Morpheus, Bearshare…
Protocols: JXTA Project • Protocols • Peer Discorvery Protocol (find advertisements of peers) • Peer Resolver Protocol (send and retrieve queries) • Peer Information Protocol (learn about peers’ status) • Peer Membership Protocol (obtain membership reqs) • Pipe Binding Protocol (bind pipe advertisements to pipe endpoint) • Endpoint Routing Protocol (find route between peers) • Unix alike security model, however users are free to implement their own • XML based messages, however YML is easy to implement • Peer monitoring • Platform independent • UUID (128-bit id to refer to an entity like a peer, an advertisement or a service)
Protocols: JXTA Project: examples on JXTA impl. • Aislandagent framework • AllhandsEvent Notification application • AngelopeerrendezvousA p2p based interactive software for intra enterprise communication • GnougatFully decentralised file caching • GnovellaSome experiments with JXTA and document storage in an enterprise • GoA Go Tournament based on the JXTA Protocols • HaluJXTA media distribution application • Instantp2pJXTA Demonstration GUI • JnushareInformation sharing application based on GISP • Juxtaprosea web / discussion content sharing application • jxta-httpdProvides a Set of service & tools provinding web publishing • MyjxtamyJXTA - JXTA Demonstration Application (aka InstantP2P)…
Protocols: FIPA Project • Combination of speech acts, predicate logic and public ontologies • Searching agents in the DF • AP: physical infrastructure in which agents can be deployed • Agent: The fundamental actor on the AP • DF: The yellow pager agent (combinations possible) • AMS: Supervisor of the platform • MTS: Message Transport Service is the default communication method
Protocols: Pastry • 128 bit ID (e.g. hash from IP address) • Hashlist of content moved close to ID • Implementations: • SCRIBEgroup communication/event notification system. • PASTarchival storage systems. • SQUIRRELa co-operative web cache.
Systems: to be continued… • Neurogrid • Poblano • JXTA • Groove • Magi • Hailstorm • Freenet • Edamok • Edutella • InfoQuilt • InfoSleuth • Jade
Systems: Poblano • On top of JXTA • Based on three components • Codat Confidence (keyword, codatID, flag for local or remote and confidence value) • Peer Confidence (keyword, peerID, confidence value) • Risk (peerID, integrity of codat, accesibility, performance)