Java Session Handling and Authentication Security Guide
Learn about Java session handling, user tracking, and authentication for secure web applications. Explore different session management methods and authentication techniques to enhance user security.

Java Session Handling and Authentication Security Guide
E N D
Presentation Transcript
Session Handling Authentication and Security Joshua Scotton
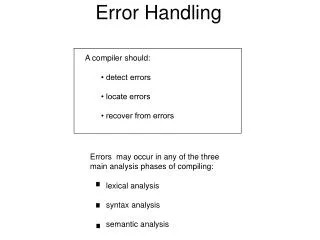
Overview • Sessions • Login and Authentication
Sessions Tracking the User
Tracking the User • Cookies • Store a unique identifier in a cookie for the website • URL Rewriting • Append a unique identifier to the end of each URL • Hidden Form Fields • <INPUT TYPE="HIDDEN" NAME="session" VALUE="...">
Benefits • Customization • Adaptive Content • Adaptable Content • Security • Restrict areas of the site based on user • User login tracked using session • User Behaviour • Track page accesses • User Information • Store user settings and information
javax.servlet.http.HttpSession • getAttribute(), getAttributeNames(), setAttribute(), removeAttribute() • These methods are used to set, get and remove objects from a user session • getId() • Every session created by the server has a unique 'id' associated with it in order to identify this session from other sessions. • getCreationTime() • Simple returns a long value indicating the date and time this session was created. • getLastAccessedTime() • Returns a long value indicating the last time user accessed any resource on this server. • getMaxInactiveInterval(), setMaxInactiveInterval() • Return and set the maximum inactive interval in seconds for this session respectively. • isNew() • Returns a boolean value indicating if the session is new. • invalidate() • Simply invalidates a session. Can be used for logout
Sessions in Java • Most Java servers will use cookies if the browser supports them, but automatically revert to URL-rewriting when cookies are unsupported or explicitly disabled.
Counter Example • Sessions can be accessed and managed by both Servlets and JSPs. • This can happen in combination as in the following demo.
CounterBean public class CounterBean implements Serializable { private Integer count; public CounterBean() { super(); this.count = 0; } public Integer getCount() { return this.count; } public void setCount(Integer count) { this.count = count; } public void incrementCount() { this.count++; } }
UpdateCounter.jsp <jsp:useBean id="counter" class="webdev.examples.sessions.CounterBean" scope="session"/> <p> The counter was: <%= counter.getCount() %> </p> <% counter.incrementCount(); %> <p> The counter is now: <%= counter.getCount() %> </p>
UpdateCounterServlet PrintWriter out = response.getWriter(); HttpSession session = request.getSession(true); CounterBean counter; if(session.isNew()) { counter = new CounterBean(); session.setAttribute("counter", counter); } counter = ((CounterBean)session.getAttribute("counter")); counter.incrementCount(); out.println("Counter now: " + counter.getCount()); out.close();
Login and Authentication Allowing Persistent Storage
JSP and Servlet Authentication • A user accesses a protected page • If the user is authenticated and has permission to access the page then the resource is made available. Otherwise a login page is shown • If the name and password cannot be authenticated then an error is shown
Security Setup • User/Group Database • Access Control List (ACL) • Login Page
Principals and Roles • A Principal is a named entity, commonly representing an individual or corporation. • Principal’s can fill one or more Roles. • Resources can be protected by associating them with Roles. • Principals and Roles are similar to Users and Groups in Linux.
/WEB_INF/web.xmlThe ACL of Java <web-app> ... <security-constraint> <web-resource-collection> <web-resource-name>Protected Page</web-resource-name> <url-pattern> /secretPage.jsp </url-pattern> </web-resource-collection> <auth-constraint> <role-name>employee</role-name> </auth-constraint> </security-constraint> <security-role> <role-name>employee</role-name> </security-role> <web-app>
/WEB_INF/web.xml • <url-pattern>/members/*</url-pattern> • More than one url-pattern in the web-resource-collection
HttpServletRequest Security Methods • Principal getUserPrincipal() • Returns a reference to a java.security.Principal • booleanisUserInRole(String) • Determines whether a user is in a role, specified by the string argument • String getRemoteUser() • Returns the username that was used for login
ServletRequest Security Methods • String getAuthType() • Returns the authentication type: BASIC, SSL, or null • booleanisSecure() • Returns true if the connection is HTTPS • String getScheme() • Scheme represents transport mechanism: http, https...
Authentication Types • Basic authentication • Form-based authentication • Digest authentication • SSL and client certificate authentication
Authentication Type in /WEB_INF/web.xml <web-app> ... <login-config> <auth-method>BASIC</auth-method> <realm-name>Basic Authentication Example</realm-name> </login-config> ... </web-app>
Realms • A realm is a database of usernames and passwords • It also contains a list of roles associated with each user • Realms are specific to the server being used
Tomcat Realms • JDBCRealm - Accesses authentication information stored in a relational database, accessed via a JDBC driver. • DataSourceRealm - Accesses authentication information stored in a relational database, accessed via a named JNDI JDBC DataSource. • JNDIRealm - Accesses authentication information stored in an LDAP based directory server, accessed via a JNDI provider. • UserDatabaseRealm - Accesses authentication information stored in an UserDatabase JNDI resource, which is typically backed by an XML document (conf/tomcat-users.xml). • MemoryRealm - Accesses authentication information stored in an in-memory object collection, which is initialized from an XML document (conf/tomcat-users.xml). • JAASRealm - Accesses authentication information through the Java Authentication & Authorization Service (JAAS) framework.
Configuring a Realm • <Realm className="... class name for this implementation" ... other attributes for this implementation .../> • Serverwide - conf/server.xml • Per Webapp – META-INF/context.xml
In Memory Realm Context.xml <?xml version="1.0" encoding="UTF-8"> <Context> <Realm className="org.apache.catalina.realm.MemoryRealm" /> </Context>
Default Tomcat User List • $TOMCAT_HOME/conf/tomcat-users.xml <tomcat-users> <role rolename="tomcat"/> <role rolename="role1"/> <user username="tomcat" password="tomcat“ roles="tomcat"/> <user username="both" password="tomcat“ roles="tomcat,role1"/> <user username="role1" password="tomcat“ roles="role1"/> </tomcat-users>
Example – members.jsp • members.jsp • web.xml • context.xml
Example – logout.jsp <p>User '<%= request.getRemoteUser() %>' has been logged out.</p> <% session.invalidate(); %>
Form-based Authentication • The login form associated with the security constraint is sent to the client and the URL path triggering the authentication is stored by the container. • The user is asked to fill out the form, including the username and password fields. • The client posts the form back to the server. • The container attempts to authenticate the user using the information from the form. • If authentication fails, the error page is returned using either a forward or a redirect, and the status code of the response is set to 200. • If authentication succeeds, the authenticated user's principal is checked to see if it is in an authorized role for accessing the resource. • If the user is authorized, the client is redirected to the resource using the stored URL path.
Form-based Authentication • Create custom login page with the following form fields: • j_username • The name of the username field • j_password • The name of the password field • j_security_check • The login form's action <form method='post' action='j_security_check'> <input type='text' name='j_username'> <input type='password' name='j_password'> </form>
Form-based Auth in web.xml <login-config> <auth-method>FORM</auth-method> <form-login-config> <form-login-page> /login.jsp </form-login-page> <form-error-page> /error.jsp </form-error-page> </form-login-config> </login-config>
Storing Authentication Details in a Database • Use a JDBC Database Realm • Create table of usernames and passwords • Create table of usernames and roles • Column name for the username must be the same in both tables
org.apache.catalina.realm.JDBCRealm • connectionName • connectionPassword • connectionURL • driverName • roleNameCol • userCredCol • userNameCol • userRoleTable • userTable • http://tomcat.apache.org/tomcat-3.3-doc/JDBCRealm-howto.html