Malware
Malware. Ge Zhang Karlstad Univeristy. Focus. What malware are Types of malware How do they propagate How do they hide How to detect them. What is a malware ?. A Malware is a set of instructions that run on your computer and make your system do something that an attacker wants it to do.

Malware
E N D
Presentation Transcript
Malware Ge Zhang Karlstad Univeristy
Focus • What malware are • Types of malware • How do they propagate • How do they hide • How to detect them
What is a malware ? • A Malware is a set of instructions that run on your computer and make your system do something that an attacker wants it to do.
Malware zoo (1) • Virus: attaches it self to a program and propagates copies of itself to other programs • Worm: program that propagates copies of itself to other computers • Logic bomb: Triggers action when condition occurs • Trojan horse: Program that contains unexpected additional functions • Backdoor: Program modification that allows unauthorized access to functionality • Exploits: code specific to a single vulnerability or a set of vulnerabilities
Malware zoo (2) • Downloaders: Program that installs other items on a machine that is under attack • Auto-rooter: Hacker tools used to break into new machines automatically • Kit (virus generator): tools to generate new viruses automatically • Spammer program: tools to produce large volume of unwanted emails. • Flooders: tools to generate large volume of unwanted traffics • Keyloggers: capture keystrokes on a compromised computer. • Zombie: Program activated on an infected machine that is actived to launch attacks on other machines
Number of malware signatures Symantec report 2009
Viruses • 4 phases: • Dormant phase: It is idle, waiting for some event • Propagation phase: Copy itself into other programs • Triggering phase: activated to perform some intended actions • Execution phase: execute the payload, maybe harmless
DOS boot Sequence • ROM BIOS: locates the master boot sector • Master boot sector: partition table • DOS boot sector: executable codes and FAT
DOS bootstrap virus • A bootstrap virus resides in one of the boot sectors • Becomes active before DOS is operational • Example: stoned virus
Parasitic virus • Overwriting virus • Appending virus
Companion virus • Do not need to modify the original files • Create a new file with a specific name
Lifecycle of virus • A virus gets created and released • The virus infects several machines • Samples are sent to anti-virus companies • Records a signature from the virus • The companies include the new signature in their database • Their scanner now can detect the virus
Virus hidden mechanisms • Encrypt virus code with random generated keys • What happens if the boot area is encrypted?
Virus hidden mechanisms (2) • Polymorphism: randomly changes the encryption/decryption portion of a virus • Change key each time the virus starts • Change the range of plaintext • Change the location of encryption subroutine • Countermeasure: scan in RAM (after self-decrypting)
Virus hidden mechanisms (3) • Entry point changes • Random execution (JMP)
Macro viruses • Macro: an executable program embedded in a document to automate repetitive tasks. (save keystrokes) • Application-dependent, e.g., MS office • Cross the O.S. and hardware platform • Why virus writers like macro viruses? • Easy to learn • Easy to write • Popularity of MS office
How macro virus works • Every word document is based on a template • When an existing or new document is opened, the template setting are applied first • A global template: NORMAL.DOT
Worm • Worm: self-replicating over networks, but not infecting program and files • Example: Morris worm, blaster worm
The structure of worms • Target locator (find the target) • Email address collector • IP/port scanner • Warhead • Break into remote machines • Propagation • Automatically sending emails • Automatically attack remote hosts • Remote control and update • Download updates from a web server • Join a IRC channel • Lifecycle management • Commit suicide • Avoid repeatedly infecting the same host • Payload
State of Worm Technology • Multiplatform: Windows, unix, mac, … • Multiexploit: web server, browser, email,… • Ultrafast spreading: host/port scanning • Polymorphic: Each copy has new code generated by equivalent instructions and encryption techniques. • Metamorphic: different behavior patterns (prepared) • Transport vehicles: for the payloads (spread attacking tools and zombies) • Zero-day exploit: self-updated
discussion • Is it a good idea to spread worms with system patches?
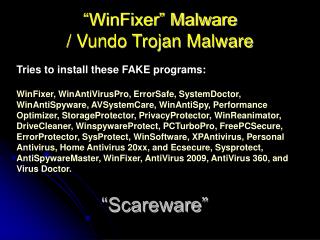
Trojan • A program with hidden side-effects that are not specified in the program documentation and are not intended by the user executing the program
What a trojan can do • Remote administration trojans: attackers get the complete control of a PC • Backdoor: steal data and files • Distributed attacks: zombie network • Password stealers: capture stored passwords • Audio, video capturing: control devices • Keyloggers: capture inputting passwords • Adware: popup advertisements
Familiar with your PC • Startup programs/services • Frequently used IP ports • 20/21 FTP • 23 Telnet • 25 SMTP • 80 WWW • Netstat
Malware Payloads • No payload • Payload without damage • Only display some information • Payload with little impact • Modify documents (wazzu virus) • Payload with heavy impact • Remove files, format storage • Encrypting data (blackmail) • Destroy hardware (W95.CIH): rewrite flash bios • DDoS attacks • Steal data for profit
Malware naming • CARO (computer antivirus researchers organization) • CARO naming convention (1991) • <family_name>.<group_name>.<Infective_length>.<variant>.<modifier> • e.g., cascade.1701.A. • Platform prefix • win32.nimda.A@mm
Malware defenses (1) • Detection: once the infection has occurred, determine that it has occurred and locate the virus • Identification: once detection has been achieved, identify the specific virus that has infected a program • Removal: once the specific virus has been identified, remove the virus from the infected program and restore it to its original state
Malware defenses (2) • The first generation scanner • Virus signature (bit pattern) • Maintains a record of the length of programs • The second generation scanner • Looks for fragments of code (neglect unnecessary code) • Checksum of files (integrity checking) • Virus-specific detection algorithm • Deciphering (W95.Mad, xor encrypting) • Filtering
Malware defenses (3) • The third generation scanner • Identify a virus by its actions • The fourth generation scanner • Include a variety of anti-virus techniques • Collection method • Using honeypots
In the future… • New spreading methods: e.g., RFID Infected! Infected! Infected!
Key points • Taxonomy of malwares • The difference between virus and worm • How does bootstrap/companion/parasitic/macro virus propagate • Virus hidden method • The structure of worm • What a trojan/malware payload can do • Malware naming standard (CARO) • Malware defenses methods