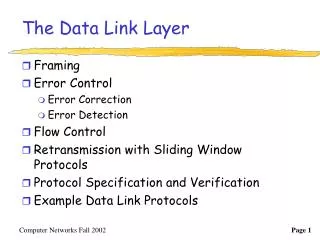
The Data Link Layer
The Data Link Layer. Framing Error Control Error Correction Error Detection Flow Control Retransmission with Sliding Window Protocols Protocol Specification and Verification Example Data Link Protocols. DATA LINK LAYER Services. Unacknowledged connectionless service Voice

The Data Link Layer
E N D
Presentation Transcript
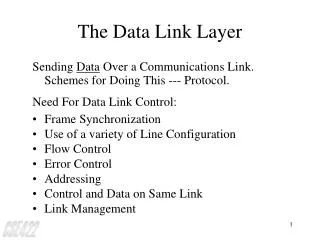
The Data Link Layer • Framing • Error Control • Error Correction • Error Detection • Flow Control • Retransmission with Sliding Window Protocols • Protocol Specification and Verification • Example Data Link Protocols
DATA LINK LAYER Services • Unacknowledged connectionless service • Voice • Acknowledged connectionless service • wireless • Acknowledged connection-oriented service • no out-of-order
Framing • To break the bit stream up into discrete frames and compute the checksum for each frame. When a frame arrives at the destination, the checksum is recomputed and validated. • One way to achieve this framing is to insert time gaps between frames. However, networks rarely make any guarantees about timing.
Data Framing • Character count • Starting and ending characters with character stuffing • Starting and ending flags with bit stuffing • Physical layer coding violations
character count 5 1 2 3 4 5 6 7 8 9 8 0 1 2 3 4 5 6 8 7 8 9 0 1 2 3 frame 1 5 characters frame 2 5 characters frame 3 8 characters frame 4 8 characters one-bit error 5 1 2 3 4 7 6 7 8 9 8 0 1 2 3 4 5 6 8 7 8 9 0 1 2 3 frame 1 5 characters frame 2 (wrong) Now a character count Even if the checksum is incorrect so the destination knows that the frame is bad, it still has no way of telling where the next frame starts. Character Count
DLE(0x10): Data Link Escape STX(0x02): Start of TeXt ETX(0x03): End of TeXt DLE STX user data DLE ETX beginning of frame end of frame user data 0x10 DLE STX A DLE B DLE ETX DLE stuffed at the sender DLE STX A DLE DLE B DLE ETX DLE destuffed at the receiver DLE STX A DLE B DLE ETX Starting and Ending Characters with Character Stuffing
flag 01111110 user data 01111110 beginning of frame end of frame original data 011011111111111111110010 bits stuffed at the sender 011011111011111011111010010 bits destuffed at the receiver 011011111111111111110010 Starting and Ending Flags with Bit Stuffing
1 0 0 0 1 1 0 Starting Delimiter Ending Delimiter user data V V 1 V V 0 0 0 V V 0 V V 0 0 0 beginning of frame end of frame Physical Layer Coding Violations V: Violation bit
Error Control • Three types of frames at a receiver’s end • Damaged frame : Negative acknowledgment / retransmission • Lost frame : Time-out mechanism • Valid frame : Sequence numbering / discarding for valid but duplicate frames
Flow Control • A technique for assuring that a transmitting station does not overwhelm a receiving station with data
Error Detection and Correction • Error-correcting codes • Error-detecting codes
Codeword • n-bit codewords with n =m+r and • m data bits • r redundant or check bits • Not all the 2n codewords are legal. In general, only 2m codewords are legal. • ASCII codes of 7 bits with 1 even parity bit • ASCII code for “A”: 1000001 • codeword for “A”: 10000010 or 01000001 • Codeword 10000011 or 11000001 is illegal.
Hamming Distance • The number of bit positions in which two codewords differ is called the Hamming distance between these two codewords. • The Hamming distance of the complete code is the minimum Hamming distance between all pairs of legal codewords.
Codeword Space • To detect d-bit errors, a distance d +1 code is needed. • To correct d-bit errors, a distance 2d +1 code is needed. 1-bit error detection 1-bit error correction
Determine the Number of Check bits • To correct single bit errors with m bits message and r check bits (n=m+r) • Code space : 2m n-bit legal messages(codewords) • For an n-bit legal codeword, all its n neighbors at a distance 1 from it are illegal • n+1 bit patterns are dedicated to each legal message • (n+1)2m <= 2n and consequently (m+r+1)2m <= 2m+r. we have : (m+r+1) <= 2r
Hamming Code • The bits that are powers of 2 (1, 2, 4, 8, 16, etc.) are check or parity bits of some data bits. • For example, m=7 (ASCII) and r=4 (7+4+1 <= 24) • B1 : B3 B5 B7 B9 B11 • B2 : B3 B6 B7 B10 B11 • B4 : B5 B6 B7 • B8 : B9 B10 B11 1 001 000 “H” xx1x001x000 0 1 0 1 0 0 01 01 00 1001 0000 00110010000 codeword
To Correct Burst Errors • A sequence of k consecutive codewords are arranged as a matrix, one codeword per row. To correct burst errors, the data should be transmitted one column at a time, i.e., column by column. • If a burst error of length k bits occurs, at most 1 bit in each of the k consecutive codewords will have been affected, but the Hamming code can correct one error per codeword, so the entire block can be restored.
1 2 3 4 5 6 7 8 9 10 11 column To Correct Burst Errors: An Example B1 : B3 B5 B7 B9 B11 B2 : B3 B6 B7 B10 B11 B4 : B5 B6 B7 B8 : B9 B10 B11 ASCII Codeword 1001000 00110010000 1100001 10111001001 1101101 11101010101 011 001 111 110 011 000 101 010 001 000 011 burst error 011 001 111 111101 000 101 010 001 000 011 Codeword 00111010000 10110001001 11111010101 Codeword 00110010000 10111001001 11101010101 B1(011100)+B4(1101) => B5 B1(110001)+B4(1000) => B5 B4(1101) => B4
Error Detection • Parity bit • low error rate • Longitudinal redundancy check (LRC) and Vertical redundancy check (VRC) • Cyclic redundancy code (CRC code) / Polynomial code • Easy hardware implementation • Can detect burst errors
Parity Bit • block size: 1000 bits • Hamming code: 1000+10 bits (m+r+1 <= 2n) • parity bit: 1000+1 bits • a message: 106 bits • without no error • Hamming code: 106+10000 bits • parity bit: 106+1000 bits • with a low error rate 10-6 • Hamming code: 106+10000 bits • parity bit: 106+1000+(1000+1) bits ( one error occurs) retransmitted block
VRC 1 0 1 1 0 1 1 1 1 1 0 1 0 1 1 1 0 0 1 1 1 0 1 0 1 1 1 1 0 0 0 0 1 0 0 0 1 0 1 1 0 1 0 1 1 1 1 1 0 1 1 1 1 1 1 0 LRC Longitudinal Redundancy Check and Vertical Redundancy Check
Cyclic Redundancy Code (CRC) / Polynomial Code • A m-bit frame is regarded as the coefficient list for a polynomial, M(x), with m terms, ranging from xm-1 to x0. For example, 110001 represents a polynomial x5+x4+x0. • Addition and subtraction are identical to EXCLUSIVE OR. For example, 10011011 11110000 + 11001010 -10100110 = 01010001 =01010110
Computing Cyclic Redundancy Code • Both the sender and the receiver must agree upon a generator polynomial, G(x), with the degree r in advance. • Append r zero bits into M(x) => xrM(x) • Divide xrM(x) by G(x) • Subtract the remainder from xrM(x) and let the result be T(x)
CRC at Receiver End • T(x) is received with no error. • T(x) is divisible by G(x) • When errors represented by error bit pattern E, ( ie. E(x)), occur, • (T(x) +E(x)) /G(x) has zero reminder only if E(x) is divisible by G(x) • Carefully selects G(x) such that E(x) is not divisible by G(x)
CRC with Single and Double Errors • Single-bit error • E(x)= xj • If G(x) contains tow or more terms, it will neverdivided E(x) • Two isolate single-bits errors • E(x)= xi +xj = xj ( xi-j+ 1) ….. i>j • Assume G(x) is not divisible by x • SelectG(x) that does not divide xk+1, where 1< k i-j
Well-Known Generator Polynomials • CRC-12: x12+x11+x3+x2+x+1 • CRC-16: x16+x15+x2+1 • CRC-CCITT: x16+x12+x5+1 • CRC-32: x32+x26+x23+x22+x16+x12+x11+x10+ x8+ x7+x5+x4+x2+x+1 • CRC-16 and CRC-CCITT • Catch all single and double errors, all errors with an odd number of bits, all burst errors of length 16 or less, 99.997% of 17-bit error burst, 99.998% of 18-bit error and longer bursts
Flow Control Techniques • Stop-and-wait • The receiver provide feedback to the sender • The sender sends one frame and then waits for an acknowledgement before proceeding
Dealing with the Damaged Frames • Adding a timer ( on sender ) • The receiver would only send an ack if the data were correctly received • After time out, the sender send the frame again
Dealing with the Lost Frames • A lost data frame can be resent by using a timer • When an acknowledgement is lost • The sender’s timer eventually time-out • The sender resends the same data frame • After the data frame is received, the receiver sends acknowledgement again
Acknowledgement • Techniques • Control Frame • Data Frame: Piggybacking • The technique of temporarily delaying outgoing acknowledgements so that they can be hooked onto the next outgoing data frame is known as piggybacking. • Types • Positive Acknowledgement: The received frame has no error. • Negative Acknowledgement: The received frame has errors.
Flow Control • Flow control is a technique for assuring that a transmitting station does not overwhelm a receiving station with data. • Sliding Window Protocols: At any instant of time, the sender maintains a set of sequence numbers corresponding to frames it is permitted to send. These frames are said to fall within the sending window. Similarly, the receiver also maintain a receiving window corresponding to the set of frames it is permitted to accept.
Sliding Windows • Each outbound frame contain a sequence number ranging from 0 to 2n-1 • Sending window • Maintained by the sender • A set of sequence numbers corresponding to frames the sender is permitted to send • Receiving window • Maintained by the receiver • Corresponds the set of frames the receiver is permitted to accept
Maintain Sliding Windows • Sending window • When a frame is sent, the upper edge of the window is advanced by one • When an acknowledgement is received, the lower edge of the window is advanced by one • Receiving window • Any received frame the sequence number outside the window is discarded • When a frame whose sequence number is equal to lower edge of the window is received, the window is rotated by one
Sliding Window Protocols • One bit sliding window protocol ( Stop-and-Wait) • Go-back-N Protocol • Selective Repeat Protocol