Steganography
By Robert Summitt and Jiten Patel. Steganography. What is Steganography. It is the art and science of writing a message in a way to where the only the recipient knows of its existence. The word Steganography is of Greek origin and means “covered, or hidden writing.”

Steganography
E N D
Presentation Transcript
By Robert Summitt and Jiten Patel Steganography
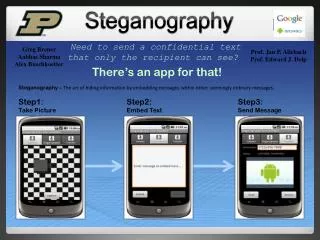
What is Steganography It is the art and science of writing a message in a way to where the only the recipient knows of its existence. The word Steganography is of Greek origin and means “covered, or hidden writing.” Steganographic messages will generally appear as something else such as a picture or a text file. Provide security over insecure channel
History of Steganography Dates back to 440 BC Heredotus and wax tablets Histiaeus and his tattooed slave Later in the 1500’s Johannes Trithemius Steganographia World War II Micro Dots Doll Woman Pueblo Incident in 1968 Sign Language Photos
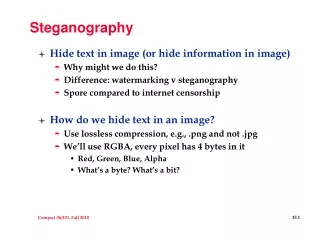
How does it work now? Encrypt Plaintext Cyphertext Stegotext Covertext
Steganography Examples • This first photo is that of a tree (obviously) • By making this image 85% brighter the result is the image of the cat below
Steganography Examples M1 = Steganographyis the art and science of communicating in a way which hides the existence of the communication. In contrast to cryptography, where the "enemy" is allowed to detect, intercept and modify messages without being able to violate certain security premises guaranteed by a cryptosystem, the goal of steganography is to hide messages inside other "harmless" messages in a way that does not allow any "enemy" to even detect that there is a second secret message present
Other Uses Hidden messages can also be implemented into audio files using the LSB method. Sounds and noises at the LSB level can not typically be heard by the human ear. Therefore when playing the original file it sounds just like a normal .wav or .mp3 file However it can be decrypted to reveal another sound file or any file for that matter. File must be big enough to hold hidden message.
Steganography In The News Bin Laden: Steganography master? USA Today reported that Bin Laden and others "are hiding maps and photographs of terrorist targets and posting instructions for terrorist activities on sports chat rooms, pornographic bulletin boards and other websites, U.S. and foreign officials say."
Popular Programs Steghide .bmp .wav .au MP3Stego .mp3 Snow Text files E-Mail
S-Tools One of the most reliable tools for steganography is S-tools This program was created in 1994 by Andy Brown There has been no updates since then because of its encryption algorithm. Nearly impossible to break
Why S-tools is so good for this! 4 different types of encryptions to choose from IDEA, DES, Triple DES, MDC The password is entered and confirmed by the user and then is encrypted using the desired algorithm To reveal any image one must know the password along with the encryption algorithm This makes it extremely difficult to break even using a brute force attack.
WinBatch attempt Using a script designed for winbatch an attempt was made to brute force a few files that supposedly had hidden files Script was designed to brute force using a dictionary file The script also tried every possible encryption method Dated machines didn’t have enough virtual memory to conduct this test but if they had it would have taken a LONG time!
More Modern day uses KFC Ad Digital Watermarking
References http://en.wikipedia.org/wiki/Steganography Including the history, modern uses, and KFC refrences http://www.winbatch.com/download.html Site where Winbatch was found http://www.phrack.org/archives/52/P52-08 Site explaining LSB and provides script used for Winbatch http://www.jjtc.com/Security/stegtools.htm Site where S-tools comes from