Enhanced Image Authentication with Content-Based Compression
This paper introduces a robust image authentication method using content-based compression, emphasizing significant points and features for creating a unique signature. The process involves finding feature points, weighting functions, compression data, and creating a secure signature to authenticate images effectively against malefic tampering. The approach utilizes a foveated image model, discrete wavelet transformation, and uniform to foveated image conversion. By recognizing the localized nature of illegal operations and the global nature of permissible operations, this method enhances image authentication.

Enhanced Image Authentication with Content-Based Compression
E N D
Presentation Transcript
Robust Image Authentication Using Content Based Compression Source:ACM Multimedia Systems, Vol.9, August 2003, page 121-130 Authors: Ee-Chien Chang, Mohan S. Kankanhalli, Xin Guan, Zhiyong Huang, Yinghui Wu Speaker:Kuo-Wei Weng Date: 2005/05/03
Outline • Introduction • Creation of signature • Authentication • Conclusion
Introduction Permissible operations:global operations Ex:resizing , JPEG compression Malefic tampering:localized operations Ex:Cropping , alteration
Introduction Cont’ I0 +signature I A B
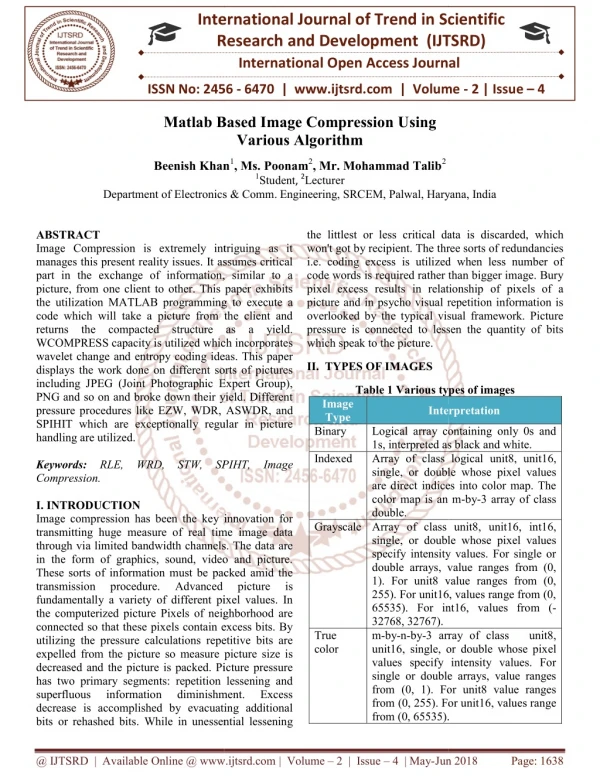
Creation of signature Find Feature points Weighting Function (W) Compression Data (S) Signature (S,W)
Creation of signature Cont’ Content-based: Salient points Weighting function
Creation of signature Cont’ Weighting function w: α:rate of resolution falls off γ:foveal location β:foveal resolution
Creation of signature Cont’ Foveated image: (with the center of the right eye as the fovea)
Creation of signature Cont’ Compression Image: Uniform resolution image Foveated image
Creation of signature Cont’ DWT(Discrete Wavelet Transformation)
Creation of signature Cont’ Compression image
Authentication Receive I and signature Extract Compression Image Authentication
Authentication Cont’ Where I0 is the original image I is the receive of image
Conclusion • Important content information is not uniformly • distributed across the image and that illegal • operations are usually localized while permissible • operations are global in nature.