Comprehensive Overview of Information Security, Digital Identity, and Ethical Considerations
This recap delves into crucial aspects of information security, covering topics such as the defense-in-depth strategy, password strength, and safeguards against social engineering, phishing, and spyware. It further explores digital identity components, including the balance between freedom of speech and the right to reputation, and the implications of online presence through social media. Additionally, ethical considerations in business practice, transparency, integrity, and case studies highlight the importance of maintaining ethical standards within organizations. This comprehensive guide serves as a valuable resource for understanding today’s digital security landscape.

Comprehensive Overview of Information Security, Digital Identity, and Ethical Considerations
E N D
Presentation Transcript
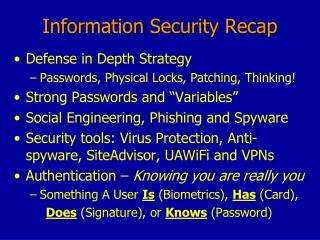
Information Security Recap • Defense in Depth Strategy • Passwords, Physical Locks, Patching, Thinking! • Strong Passwords and “Variables” • Social Engineering, Phishing and Spyware • Security tools: Virus Protection, Anti-spyware, SiteAdvisor, UAWiFi and VPNs • Authentication – Knowing you are really you • Something A User Is (Biometrics), Has (Card), Does (Signature), or Knows (Password)
Digital Identity Recap • Competing Rights • Freedom of Speech vs. Right to Reputation • Components of Online Reputation • Location-based (Geo-tagging), Social media and networking, Blogging and Messaging • Employment Background Checking • 63% Filter before the interview (discrimination issues) • Dimensions of privacy • Anonymity, Confidentiality, Security
Ethics in Business and Eller • Recognizing ethical situations • Gut check, Transparency test, Ethical drift • Case Study: David Myers (MCI/Worldcom) • Ethical Dilemmas • Who Am I? Integrity vs. Loyalty Whistleblowing • Who Are We? Organizational Ethical Values Short term vs long term • Integrity Testing Job Screening • E-TegrityGoodcat hotline Board of Honor and Integrity