Designing Security Architecture Infrastructures
180 likes | 558 Views
Designing Security Architecture Infrastructures. CISSP . CISSP - Certified Information System Security Professional . https://www.isc2.org CISSP examination http://www.cccure.org CISSP Studying Information . CISSP Certification Examination.

Designing Security Architecture Infrastructures
E N D
Presentation Transcript
Designing Security Architecture Infrastructures CISSP LTU CISSP
CISSP - Certified Information System Security Professional • https://www.isc2.org • CISSP examination • http://www.cccure.org • CISSP Studying Information LTU CISSP
CISSP Certification Examination • The CISSP Certification examination consists of 250 multiple-choice questions. Candidates have up to 6 hours to complete the examination. • Ten CISSP information systems security test domains are covered in the examination pertaining to the Common Body of Knowledge: • Access Control Systems & Methodology • Applications & Systems Development • Business Continuity Planning • Cryptography • Law, Investigation & Ethics • Operations Security • Physical Security • Security Architecture & Models • Security Management Practices • Telecommunications, Network & Internet Security LTU CISSP
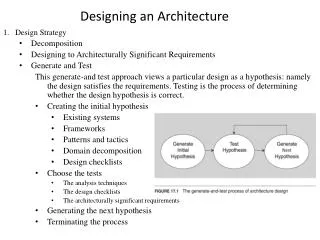
Agenda • Common Body of Knowledge – 6 Topics • Cover the examination topics – but will emphasis what works and what does not • Homework – yes • Skim the chapter • do some projects • do practice tests and discuss results. • Discussion of Sample Tests • Why topics are important • Hand-outs • Electronic Viewgraphs will be available at the end of the course. • Still Being Improve LTU CISSP
Mapping LTU CISSP
ITU / CISSP Two Classes • Designing Security Architecture Infrastructures • Focuses on the technical items • Security Assessment • Management Infrastructures • Plans • Polices & Procedures • Test Readiness LTU CISSP
Instructor • Jim Bullough-Latsch • jbl@4terrorism.com • 818-775-1015 • Security Experience • Recent security assessments, plans, policies, procedures for Web Systems. • Worked on Classified Systems. • Architect for Several Systems with Sensitive Data • Consulted on automating alarms and physical security systems • Has plenty of Degrees and Lots of Years • Available for consulting! LTU CISSP
Why are you here? • What do you know? • What do you want to learn? LTU CISSP
Security Trends – Quick Summary • On-line Business • On-Line Information • Access to Information • Home Land Security • Traditional Closed Systems – New DoD Business LTU CISSP
Dollars! • Security = $ LTU CISSP
Jim’s Definition of Computer Security • “Protecting tomorrow systems against yesterday’s threats” • Advice – Follow the Money LTU CISSP
Security Trends – Book Chapter 2 • Many organizations incorrectly assume that information security is a technical issue. • Information security is a management issue that may require technical solutions. • Agree – and it requires operational solutions as well. • More and More Companies are coming online and connecting their closed systems to the internet. • Agree – Need to stay in business • Lots of Advice about multiple layers as a security feature • Disagree • Each new interface causes lots of problems and access points! LTU CISSP
Internet – Information and Vulnerability • Cardholder Information Security Program - Check List • Will Review some each Session LTU CISSP
Visa U.S.A. Cardholder Information Security Program (CISP) • The Visa U.S.A. Cardholder Information Security Program (CISP) defines a standard of due care and enforcement for protecting sensitive information. • Because the payment industry places a high priority on maintaining the confidentiality and integrity of account and personal data, the CISP requirements are directed to all entities that store, process, or transmit cardholder information. • The program ensures the annual validation of merchants that accept Visa and all service providers on both the Issuing and Acquiring side of the business. • Includes advice on best practices and information sources! LTU CISSP
Information Security Program – Digital Dozen Requirements • Install and maintain a working firewall to protect data • Keep security patches up-to-date • Protect stored data • Encrypt data sent across public networks • Use and regularly update anti-virus software • Restrict access by "need to know" • Assign unique ID to each person with computer access • Don't use vendor-supplied defaults for passwords and security parameters • Track all access to data by unique ID • Regularly test security systems and processes • Implement and maintain an information security policy • Restrict physical access to data LTU CISSP
Rest Of Today • Internet Sources • CISP Overview • Access Control LTU CISSP
http://commoncriteria.org http://csrc.nist.gov/ http://iase.disa.mil/policy.html#guides http://niap.nist.gov/ http://sepo.spawar.navy.mil/sepo/index2.html http://us.mcafee.com http://usa.visa.com/business/merchants/cisp_index.html http://v4.windowsupdate.microsoft.com/ http://www.cert.org http://www.criticalsecurity.com http://www.fas.org/irp/doddir/dod/5200-1r http://www.hq.nasa.gov/office/codeq/ns871913.htm http://www.isalliance.org/ http://www.microsoft.com/security http://www.nsa.gov http://www.pogner.demon.co.uk/mil_498 http://www.radium.ncsc.mil/tpep http://www.sans.org/top20/ http://www.symantec.com/ https://sans20.qualys.com/ Internet Resources LTU CISSP