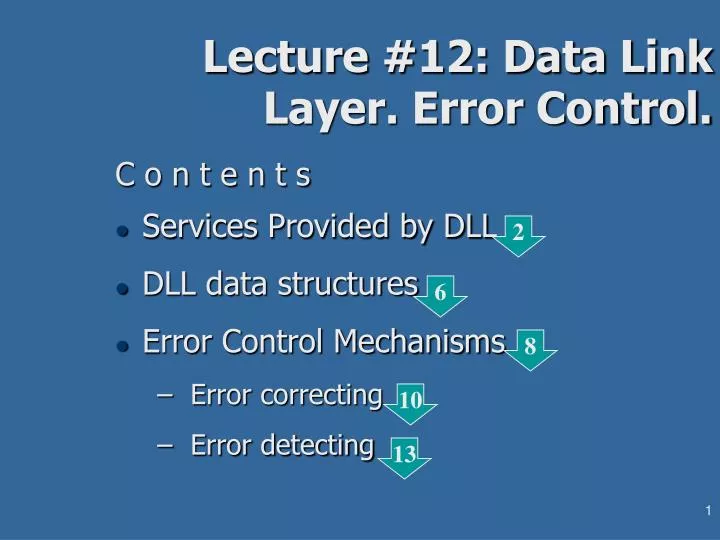
Lecture #12: Data Link Layer. Error Control.
E N D
Presentation Transcript
Lecture #12: Data Link Layer. Error Control. C o n t e n t s • Services Provided by DLL • DLL data structures • Error Control Mechanisms • Error correcting • Error detecting 2 6 8 10 13
DLL Services to the Network Layer Organizing the data transfer from source machine Network Layer to destination NL: • controls two interfaces - to the Network Layer (“upper”) and to the Physical Layer (lower”) • data on DLL level is presented by a bit stream in the Physical Layer interface and by a frame in the Network Layer interface • type of the DLL service vary between: • unacknowledged connectionless service • acknowledged connectionless service • acknowledged connection-oriented service
Types of DLL Services • Unacknowledged connectionless service • no feedback upon delivery of the frames in the remote machine • no connection establishment before the exchange • application: by low error rate channels; real-time applications and wherever the system promptness dominates over the correctness • Acknowledged connectionless service • frames which delivery is not acknowledged for certain time-out can be retransmitted to the destination • application: unreliable channels such as wireless data transfer • Acknowledged connection-oriented service • 3-phase transfer: connection establishment with initialization of parameters, allocation of local buffers etc.; frame[s] transmission and connection release • guarantees not only the frame delivery, but also the order of delivery Note that undelivered data might be required on some upper layer, but DLL has the smallest re- transfer overload because it repeats only the missed frames 3/2
DLL Frames • Frame is the data structure to which DLL brakes the incoming bit stream provided by the physical layer. • Frames’ framing methods: • time gaps - inapplicable for any asynchronous transmission • character counting - very hard error recovering because of possible counter’s damage • framing characters with character stuffing - starting and stopping ASCII character sequences at the frame’s boundaries: • starting characters DLE STX = “Data Link Escape” “Start of TeXt” • stopping characters DLE ETX = “Data Link Escape” “End of TeXt” • stuffing sequence DLEfor each incidental DLE sequence in the payload • Application: limited; suitable for ASCII oriented applications • framing flags with bit stuffing ... 3/3 3/4 5
DLL Frames • … framing flags with bit stuffing - starting and stopping bit sequences (“flags”) at the frame’s boundaries: • start/stop bit pattern 01111110 - 1 byte (6 “1”) • stuffing bit “0” for each incidental sequence of 5 “1” in the payload • Application: universal • framing with redundant signal codes: possible when the physical layer can distinguish more than 2 conditions (“1”/”0”) of the transferred signal; the exceeded signal states are used for flagging of the frames 3/5
Error Control • Two main mechanisms for error free transfer on DLL: • acknowledgement of each received frame • indexing of the sequence of outgoing frames • Acknowledged services require acknowledgement upon receiving of the frame. This mechanism includes: • sending acknowledgment frame from the receiver to the sender for each successfully received frame • initiation of one autonomous timer process by the sender for each outgoing frame - the going off the timer before the acknowledgement is interpreted by the sender as a transmission failure • Connection-oriented services require indexing of the outgoing frame sequence helps to keep up the consistency of the transmitted data in cases as: • repeated frames due to unacknowledged transmission • disordered frames due to transmission problems
Flow Control • Flow control synchronizes the rate at which frames are transmit between two heterogeneous computers in the case when faster sender transfers frame sequence to a slower receiver • Most developed control flow mechanisms are implemented in connection-oriented DLL protocols.
Error Codes - Main Terms n = m+r DF m EC r CW • Codeword (CW): n bits, m bits data field (DF) + r bits error check (EC) redundancy • Hamming distanced = ||CW1CW2|| - the number of different bits in two CWs. • ||{DF}|| = 2m , however ||{EC}|| < 2r - depending on the algorithm for check bits computation list of the valid CWs - “complete code”. • Hamming distance of complete code= min(||CWiCWj||; i, j:ij) • d-tiple error in a CW: d bits of the original CW are received inverted
Error Correction and Error Detection • Error-correcting codes: enough redundant information to reconstruct the original CW and its data field (DF) at the receiver. Application: simplex data channels that have no possibility for retransmission request. • Error-detecting codes: less redundant information that can only detect presence of corrupted bit[s] but is not enough to reconstruct the original CW. Application: more efficient than error-correction coding in all cases when feedback request is possible. • d-tiple error detecting needs coding of d+1 Hamming distance: thus after alterations of any d bits in a valid CW the obtained word is not a valid one (One more alteration could turn it in a valid one) • d-tiple error correction needs coding of 2d+1 Hamming distance: thus after alterations of any d bits in a valid CW the obtained word is still closer to the proper (original) CW in the list of legal words than any neighbor word of the list. Than the wrong CW can be replaced by the proper one.
Error Correcting Codes n = m+r DF m EC r CW • For error-correcting code of distance 1: • 2m valid data fields • n illegal CWs at distance 1 of each valid CW • n+1 bit pattern needed to distinguish each valid CWs • 2n total bit patterns (all CWs) one needs n: 2m(n+1) 2n (m+r+1) 2r 2r +r+1 m • Examples: for m = 4 rmin = 3; for r = 4 mmax = 11 • Parity check: CW consists of check bits (ci) and data bits (di) - the rest, Even(/odd) check sums modulo 2: si=0(/1): • ci=1, 2, 4,8, (...powers of 2) • di=3, 5, 6,7, … • s1 = c1d3 d5 d7 d9 …. • s2 = c2d3 d6 d7 d10 …. • s3 = c4d5 d6 d7 d12 ….
Check Sums S s1:= c1 d3 d5 d7 d9 d11 d13... di c1 c2 c4 c8 c16 3= 1 2 4 8 16 5= 1 2 4 8 16 6= 1 2 4 8 16 7= 1 2 4 8 16 9= 1 2 4 8 16 10= 1 2 4 8 16 11= 1 2 4 8 16 12= 1 2 4 8 16 13= 1 2 4 8 16
Check Sums • Application: • mostly: correction of single isolated errors • correction of burst errors - only by matrix presentation of CWs: transmission of equi-significant bits of CWs and parity check of the completed CWs transformation of a transmission burst error into single errors in sequence of CWs
Error Detecting Codes • Single block parity bit detects single error with unacceptably low probability (0.5) • n column parity bits in the last row of a nk matrix block detect burst errors of length up to n. The full probability for error detection of this coding is 2-n (the more parity bits the better detection) • Polynomial code (CRC - cyclic redundancy code) of length k. Based on presentation of bit strings as polynomials with binary coefficients: the k-bit string bk-1b k-2 …b1b0 is presented by the polynomial bk-1xk-1 + bk-2xk-2 + ... + b1x + b0
Cyclic Redundancy Code • Requisites: • m-bit message frame corresponding to polynomial M(x) • r+1-bit generator sequence with corresponding generator polynomialG(x): r < m, br=1 and b0=1 • Product:transmitted frame of size (m+r) bits containing the message and an r-bit checksum field. Transmitted frame polynomial form is T(x). The check sum field that turns guarantees that T(x) is dividable by the generator polynomial with a zero reminder (redundancy).
Cyclic Redundancy Code quotient reminder generator polynomial • CRC coding procedure consists of modulo 2 arithmetic operations: T(x) 2r G(x) = Q(x) [R(x) G(x) ] and [for modulo 2 arithmetic and (-) operations are equivalent; (-) operator does not exist]: [ T(x)2r ] [R(x) G(x)] = Q(x) i.e. the expression T(x) 2r R(x) has to be dividable by G(x) with NO reminder (in case of correct transmission)
Cyclic Redundancy Coding G(x) M(x) Q(x) T(x) R(x) {coding phase} R(x) {decoding phase} 1011 1111 10101 10011011 0011 10101 01100 00000 11001 10101 11001 10101 1100 0 1010 1 110 10 101 01 11 111 10 101 1 0101 1 0101 0 0000 1011 1111 10101 10011011 0000 10101 01100 00000 11001 10101 11001 10101 1100 0 1010 1 110 10 101 01 11 110 10 101 1 0110 1 0101 0 0011 coding decoding The divisor is going into the dividend if the last has as many bits as the former. Here 1001110101=1 though 10011 < 10101
Cyclic Redundancy Decoding • Error pattern E(x):xi= 1 means that i-bit has been erroneously converted during transmission • Erroneously transmitted frame Te(x) = T(x) E(x) • By CRC decoding Te(x)G(x) = [T(x) E(x)]G(x)= E(x) G(x) i.e. the error detection depends of whether the error pattern is dividable by the generator polynomial. Case study: • single errors: E(x)=xi. Detectable by any G(x) of more than 1 term; • double errors: E(x)= xi + xj = xj (xi-j +1). Detectable by any G(x) that is not of type x(xk+1)for k = 1, 2, …(i-j). • odd number errors: detectable by any G(x): G(x) = (x+1)G´(x) • burst errors of lengthk: E(x)= xi (xk-1+…+1). Detectable by any G(x): G(x) = G´(x)+1 and k-1< r. Standard CRC polynomials: CRC12 = x12+x11+x3+x2+x+1 - 6-bit character code CRC16 = x16+x15+x2+1 - 8-bit character code CRC-CCITT = x16+x12+x5+1 - 8-bit character code
3/3 Placement of the data link protocol.
3/3Framing A character stream. (a) Without errors. (b) With one error.