Web Infrastructure Security
Web Infrastructure Security Using Linux as a Tool to Eliminate Security Vulnerabilities Agenda Market Problems Top 10 Internet Security Vulnerabilities per SANS Institute And how to plug security holes Using Linux to Secure Web Infrastructure A virtually “cracker proof” Linux OS

Web Infrastructure Security
E N D
Presentation Transcript
Web Infrastructure Security Using Linux as a Tool to Eliminate Security Vulnerabilities
Agenda • Market Problems • Top 10 Internet Security Vulnerabilities per SANS Institute • And how to plug security holes • Using Linux to Secure Web Infrastructure • A virtually “cracker proof” Linux OS • Protection for both the applications and the operating system • Summary
Market Problems • $45 billion of lost e-commerce revenues for companies due to “hacking” in 1999* • Online security of Dot com’s and regular businesses is a BIG CONCERN • DDoS attacks are a serious threat • Internet infrastructure needs 99.999% uptime *PriceWaterhouseCoopers
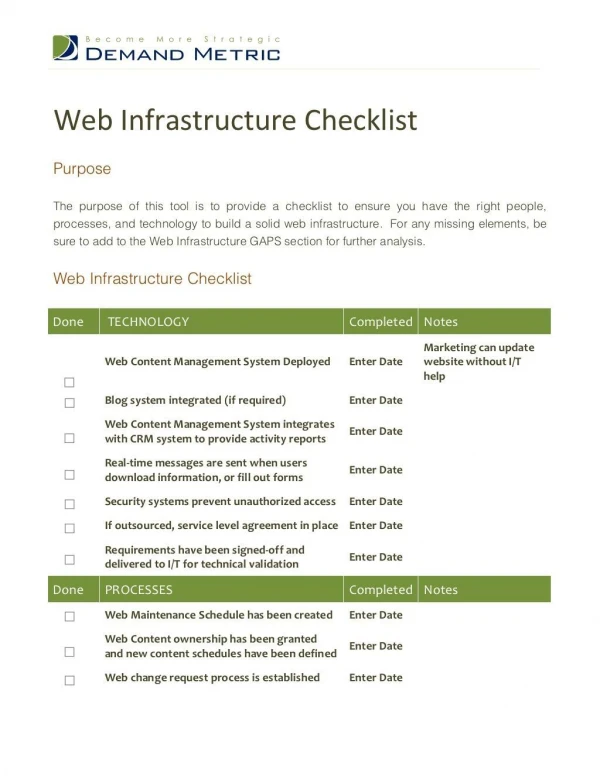
Vulnerability 1. DNS/BIND 2. CGI Programs To Dos: Use the latest release: 8.2.2 patch level 5 Run BIND as unprivileged user “dns” in a “chroot prison.” Remove Samples Remove unsafe and unnecessary scripts Run Apache as unprivileged user in a chroot prison. Top Ten Security VulnerabilitiesAccording to SANS (System Administration, Networking, and Security) Institute
3. RPC 4. Microsoft IIS 5. Sendmail buffer overflows 6. Sadmind and Mountd 3. Don’t run if you don’t have to. 4. Don’t use it if don’t have to. 5. Replace with Qmail. Qmail has never been cracked. StackGuard protects against buffer overflows. Qmail is run in a chroot prison as a non-privileged user. 6. Don’t run if you don’t have to. Cont.
7. NFS global file sharing 8. User ID esp. root 9. IMAP and POP overflows 10. Default SNMP settings 7. Don’t run NFS on Web servers. 8. System accounts are not able to login (set to /bin/false) It is up to users to set good passwords. Include a password cracker on the machine to verify good passwords. 9. Use Qmail. It’s never been cracked. 10. Don’t run SNMP on your Web servers. Cont.
Overview of a Secure Server Operating System • Server Application Protection • Stack Smashing Prevention • Middleware Library protection • Various security items not covered • Removing system user accounts, etc. • Non-Executable Stack Area • Auditing software
Server Application Protection • Turn off setuid binaries • Run “out of box” Firewall, a variation of IP Chains that gives the protection of a firewall to every server • Force a root login on single user mode. • Restrict system utilities to user “root” only • Place named in chroot prison
Stack Smashing Prevention • Replace C Compiler GCC compiler • Stop Stack Smashing attacks by adding a termination string or canary word. • Halt attempted operations and logs intrusion attempts • Every compiled app should be protected.
Middleware Library protection • Protect against as yet unidentified exploits. • Watch the library calls for buffer overruns. • Protect applications that users install, even RPMs. • Do not allow overrun of stack or stack smashing attacks.
Various Security Enhancements • Place applications like qmail and Apache Web Server in a chroot prison. • Turn off all unnecessary daemons • Turn off telnet and ftp and force secure protocols like SSH (WUFTP is available in our vHost products) • Turn off world readable to some directories and files.
Non-Executable Stack Area • Non-executable stack area. • Restricted links in /tmp • Privileged IP aliases. Protects users on virtual hosts only root has additional access. • Restrict user behavior in /proc
Auditing Software • Notify users in case of stealth port scans. • Detect attempts at buffer overflows • Detect CGI attacks • Detect SMB probes • Detect OS fingerprinting attempts
Security Summary • Close the security exploits that exist • Pro-actively prevent new security exploits • Minimize your exposure so even an exploit can only hurt one application and not your whole server • Notify systems administrators of unusual behavior
Why Linux? Scalability Reliability, and Security Ideal Linux Unix NT High Cost Low Cost
Why Linux? • Additional benefits of Linux for the corporate market • Because the source code is open, security patches can be implemented much more rapidly than in closed-proprietary software • Because the source code is open, bugs can be fixed quickly and easily without having to wait for proprietary vendors to issue fixes on a schedule that suits them more than their customers. • Because the source code is open, groups of companies can collaborate on software problems and issues without being concerned about an anti-trust lawsuit. • Linux programs can be installed on practically any machine— including older, outdated computers—and offer business owners a degree of flexibility they wouldn't find with other operating systems.
Why Linux? • Did you know… • Linux server shipments grew 190% from 1997-98 and another 140% from 1998-99* • Currently 40% of all internet servers are running on Linux* • Over 2000 different applications currently run on or are being ported over to Linux, including applications from over half of the major e-commerce software vendors** *IDC **Investors Business Daily
Some Useful URLs • http://bastille-linux.sourceforge.net • www.snort.org • www.netsaint.org • http://www.tripwire.com/products/linux.cfm? • http://www.openwall.com/linux/README • http://www.bell-labs.com/org/11356/libsafe.html • http://www.lids.org/ • www.stackguard.org