Putting the P ieces Together
University of Central Arkansas Trista Davis Jennifer Landowski Justin Rasnick Joseph Hawkins Putting the P ieces Together The Impact of Information Technology on Student Affairs Information Technology

Putting the P ieces Together
E N D
Presentation Transcript
University of Central Arkansas Trista Davis Jennifer Landowski Justin Rasnick Joseph Hawkins Putting the Pieces Together The Impact of Information Technology on Student Affairs
Information Technology • “The development, implementation, and maintenance of computer hardware and software systems to organize and communicate information electronically.” • - dictionary.com • Referred to as “IT” for short • Includes personal computers, email systems, network servers, WebCT, iPods, Microsoft Office, Second Life, cellular phones • Has changed the way people share information and interact on campus • So integrated into life that we now have a full support staff (professionals, paraprofessionals, student workers, etc.) When you see this icon, please click to proceed.
History of Information Technology 1940 Computers called mainframes fill entire rooms. 1979 The invention of microprocessor chips dramatically reduces the size of computers. 1990 Newly developed programming changes how information is sent across networks, creating the internet as we know it. All the information for this timeline was taken from the following websites: BBC News U.S. Census Bereau Ian Peter's History of the Internet The Internet Society 1960’s Computers connected together across phone lines using modems, creating the first network. 2003 61.8% of American households have computers and 54.7% of households have internet access. (Davis, Janus, Cheeseman Day,2003) 1982 More than 100,000 computers in U.S. schools.
Who are the “Millennial Students?” The Beloit Mindset List “Each August for the past decade, as faculty prepare for the academic year, Beloit College in Wisconsin has released the Beloit College Mindset List. Its 70 items provide a look at the cultural touchstones that have shaped the lives of today’s first-year students, most of them born in 1989.” • “Off the hook” has never had anything to do with a telephone. • American rock groups have always appeared in Moscow. • Thanks to MySpace and Facebook, autobiography can happen in real time. • They’re always texting each other. • Humvees, minus the artillery, have always been available to the public. • Born between 1982-2002 • More diverse than any previous generation • Skilled at multi-tasking • Accustomed to teamwork • Expect structured environments • Expect instant results
Born before 1980 The Millennial Generation
Why put the puzzle together? • To highlight the impact of technology on the services offered and methods of operation on campus • To examine the benefits and drawbacks of the technologies examined • To reflect on the past in order to better be able to predict and prepare for the future
Puzzle Pieces Recruitment Accessibility Information Delivery Safety and Security Distance Learning
Puzzle Pieces This area has gone from being completely paper-based to primarily technology based. Not only can students apply online to schools and research the thousands of schools out there, but they can also receive virtual tours of the school they want to attend. Accessibility Information Delivery Safety and Security Distance Learning Recruitment
Recruitment • The process where institutions create an organizational program of attracting prospective students. • Traditional recruitment: • newspapers, the trade press, word-of mouth, faxed/mailed pamphlets • The traditional method of recruitment has been revolutionized by the emergence of the internet • Students today can now apply for colleges and universities online as well as take virtual tours of campuses, see video footage or pictures of residence halls and apartments, submit résumés to graduate school or masters programs, and take online courses.
Online Recruitment Texas Christian University in Fort Worth believes it will become the first in Texas to move to an entirely electronic application process. “A couple of years ago, I predicted that within five years we’d be all-electronic; it arrived a bit earlier than I expected. Eighty-three percent of TCU’s applications for enrollment this past year were submitted over the internet. The more compelling figure was the 50,000 plus applications sent via email and only 1 percent returned completed via mail.” - Raymond Brown, Dean of Admissions at TCU Laptop Recruitment Students Laptop Mandates: Creating the Competitive Campus says: “Campuses that offer incoming students laptop computers have a recruitment and retention edge. Laptop mandates help universities create a completive, attractive environment, and therefore help recruit and retain students; this is evidence by increases in enrollment and student retention in colleges and universities that have such programs.” Blog Recruitment “Most schools wouldn’t consider using a picture of a campus restroom on an admissions brochure paired with a direct quote from a current student saying, ‘There’s no freakin’ way in JOHN!’ But in a sense, that’s the direction which recruiting appears to be heading as more colleges turn to student-written blogs to give prospective students and their parents a glimpse of life in college. Blogs create a constant contact stream between a school and a potential student over a long period of time. As a result, schools using blogs already have a leg up on competing colleges that are only using traditional marketing efforts.” -Ball State University
IM Recruitment-Susquehanna University “Instant Messenger is changing how students write, creating much shorter attention spans. The web has also changed application patterns. Students are doing 50-90% of their college research online. They’re going to the website and taking our virtual tour; it’s one of the key elements of our site. Forty percent of our applications are coming online. Only a couple of years ago that number was about 10-15%.” IM Recruitment-Binghamton University “Instant messaging has become a quick and easy forum for students to ask questions and get answers immediately. Rather than being a fad, it allows us to share information and build the kind of relationship that we both can benefit from. We get to know them and vice versa. It’s a real win-win.” “There are 8-10 telecounselors to work with students after office hours Monday-Thursday to call, email, and instant chat with prospective students. Around 430 schools including: Iowa State, University of Alabama, Southwest Minnesota State, and Harvard University have signed up for the Boston-based Chat University online services to recruit students.”
Online Recruitment • Cost-effective • A great tool to reach the global market • Time saving-people respond faster • Slowly increasing demographic scope • Offers access to sizeable amounts of information • Websites are far more useful than brochures • Less formal contact • Impersonal • Discrimination towards internet non-users • May have a disparate impact on certain groups: ethnic minority • Language barrier • Limited demographic scope Pros VS Cons “Having access to wealth of knowledge means you won’t waste your time applying for a role to which you are not suited.” - Unknown
Where are we headed? Recruitment is key for growth in any organization. It is how one goes about recruiting that changes things. Technology has taken over the recruitment process and will continue to grow. From newspapers to websites, from snail mail to email, from telephone to instant messaging, change is inevitable. As student affairs professionals we need to be sure to be in the constant know of what is changing and taking place in our world. Before we know it, instant messaging will be a thing of the past and something else will take its place. “I think it's fair to say that personal computers have become the most empowering tool we've ever created. They're tools of communication, they're tools of creativity, and they can be shaped by their user.” - Bill Gates
Puzzle Pieces The degree to which a product is accessible by as many people as possible and is strongly related to Universal Design, making things accessible to all people. In the past people who were challenged in these certain areas did not have the proper access they do today. People in wheelchairs weren’t able to enter a building without having someone hold open the door for them. People who were blind or had visual problems weren’t able to read their text books on their own. Even students who lived in the residence halls didn’t have the proper access needed to get through the day. Today is a new day. Huge developments within technology benefit not only people with disabilities but everyone else. We have ramps for wheelchair access, electric door openers, and tapped text and CCTV (closed caption television) that help students who struggle with vision to succeed in reading their books. Recruitment Information Delivery Safety and Security Distance Learning Accessibility
Universal Design An approach to the design of all products and environments to be usable by everyone, to the greatest extent possible, regardless of age, ability, or situation. It serves people who are young or old, with excellent or limited abilities, in ideal or difficult circumstances. Universal Design benefits everyone by accommodating limitations.
UALR (University of Arkansas at Little Rock) and Universal Design The Seven Principles of Universal Design • Equitable Use - The design is useful and marketable to people with diverse abilities. • Flexibility in Use - The design accommodates a wide range of individual preferences and abilities. • Simple and Intuitive Use - Use of the design is easy to understand, regardless of the user’s experience, knowledge, language skills, or current concentration level. • Perceptible Information - The design communicates necessary information effectively to the user, regardless of ambient conditions or the user’s sensory abilities. • Tolerance for Error - The design minimizes hazards and the adverse consequences of accidental or unintended actions. • Low Physical Effort - The design can be used efficiently and comfortably and with a minimum of fatigue. • Size and Space for Approach and Use - Appropriate size and space is provided for approach, reach, manipulation, and use regardless of user’s body size, posture, or mobility. Universal Design is a concept that has emerged from the architectural field and is now being applied in other areas. The term “Universal Design” was defined by the team of architects, environmental researchers, engineers and product designers who are credited with its origin. They define Universal Design as “the design of products and environments to be usable by all people, to the greatest extent possible, without the need for adaptation or specialized design.” This same team of professionals developed a set of seven principles which guide designers in the development of products and environments to maximize usability and accessibility.
Universal Design and Disability Services The accommodation model of disability services is currently the most prevalent model in the postsecondary setting. This realization, for many disability service providers, results in a recognition that a change must occur in the DSS office before it can occur across the campus. One way to approach this change is to engage in a strategic planning process.
Disability Support Services at the University of Central Arkansas (UCA) “The goal of DSS is to maximize each student's educational potential while helping him or her develop and maintain independence. Our philosophy is one that encourages self-awareness, self-determination, self-advocacy and independence in a comprehensively accessible environment. While complying with the letter of the law, DSS also embraces the spirit by providing services to all students with permanent or temporary disabilities to ensure that all University programs and activities are accessible. The student's responsibility is to become informed about and to make use of the resources and services that are available.” –University of Central Arkansas “DSS had to evolve with our student population at UCA. The computer technology needs of students in general have grown substantially within the past 10-15 years, as has the assistive technology needs of students with disabilities. When I arrived here in 2000, we had already purchased our first version of Kuzweil 3000, Dragon Dictate, the Braille printer, and an older model CCTV. Most of the technology that DSS provides is in the library room 222, our assistive technology lab. Decentralized access to assistive technology- Students having access to needed software within our university's general use computer labs, would be a logical next step in our department.” – Crystal Hill, Director of DSS
Universal Design with Technology What UDL represents: • In 1990, the Americans with Disabilities Act was signed into law. That act prompted a rethinking of architectural design to give disabled citizens greater access to public buildings as well as commercial facilities and transportation. • The concept of designing technology for a broad range of personal needs and abilities is known as Universal Design. In educational technology, it means designing software and hardware that everyone can access and learn from. • Universal Design for Learning (UDL) draws upon principles of Universal Design that are now widely accepted in architectural and product development, and applies these principles to the needs of teaching and learning. • UDL represents a convergence of thinking about the best uses of technology. • UDL calls for multiple means of representation, multiple means of expression, and multiple means of engagement. • Universal Design goes hand-in-hand with technology because computer-based materials are the most practical way to provide the needed flexibility.
Four Tenets of UDL: Universal Design goes hand in hand with technology because computer-based materials are the most practical way to provide the needed flexibility. Our goal is to make software with multiple options to support mathematical problem description and problem solving. • Rather than constituting a separate category, students with disabilities fall along a continuum of learner differences. • Teacher adjustments for learner differences should occur for all students, not just those with perceived disabilities. • Curriculum materials should be varied and diverse, and should include digital and online resources rather than centering on a single textbook. • Instead of "remediating" students so that they can learn from a set curriculum, curriculum should be made flexible to accommodate learner differences.
Accessibility • Not everyone will take advantage of access • Lack of motivation on students part • May not meet specific needs but overall needs • Opportunity to be a crutch for some students • Lack of knowledge or recourse • Access for everyone • Success for students in class • Motivation • New opportunities for students • Self-identity • Challenges others Pros VS Cons
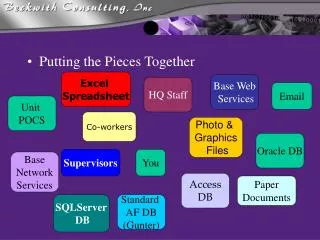
Puzzle Pieces • How are people really communicating within student affairs? • Email- mail through the internet • Social Networks- online communities such as Facebook • Portable devices- iPods, Blackberries, cell phones laptops, palm pilots and more • Portals- URSA remote access portal • GroupWise- groupware software • Intranet- a private network protected by a firewall Recruitment Accessibility Safety and Security Distance Learning Information Delivery
Social networks have become one of the most widely used forms of information delivery, helping with communication between different groups of people. Facebook is one of the largest Social Networks around. It was founded in 2004 and has since then grown exponentially. Who is using Facebook? 64,000,000 active users. 250,000 new registrations a day since January 2007. A little under half of Facebook users are in college. Facebook maintains 85% of the 4-year university market share. Social Networks
GroupWise GroupWise provides a power that allows users to synchronize information between nearly any mobile device and their Novell GroupWise accounts. This latest technology innovation opens the door to allow total freedom. GroupWise allows users unrestricted, protected access to email, appointments, contacts, tasks and notes from their personal handheld portable information device. Another dynamic aspect of GroupWise is their “push” technology. The push technology instantly pushes data from the GroupWise Mobile Server to the user’s mobile device as soon as it arrives in the user’s inbox via WiFi or another internet carrier of the users choice. GroupWise has also allowed for documents to be seen in their original format. Word processing documents, spreadsheets, and presentations can be viewed from your portable device without any formatting issues.
Intranet • Four Main Benefits: • Better internal communication- university information can be stored centrally and accessed at any time. • Sharing of resources and best practice- a virtual community can be created to facilitate information sharing and collaborative working. • Improved customer service- better access to accurate and consistent information by faculty and staff enhanced levels of student service. • Reduction in paperwork- forms can be accessed and completed on the desktop, and then forwarded as appropriate for approval, without ever having to be printed out. What does this mean for universities? Intranets enhance communication between employees, and provide a common knowledge base and storage area for everyone in your business. They also provide easy access to university data, systems and email from their individual desktops. What is an intranet? An intranet is a private website that uses the same underlying structure and network protocols as the internet and is protected from unauthorized users by a firewall. What does this mean for everyone? Because intranets are secure and easily accessible through the internet, workers and students can access these intranets from almost anywhere. What this means is that faculty, administration, and students can access the information they need whenever they are on a trip, sick at home, at another university, and the list can go on and on. Due to portable devices, this day and age anyone can access their university’s intranet from literally anywhere in the world and work as if they are sitting at their own desk.
Email Information Delivery Universities across the nation are using email. Even though email has been around for a very long time the application has changed over the decades. • How email is being used today: • To communicate with students/coworkers as a group between classes/meetings. • To extend discussion beyond the classroom to the student that is a shy person, absentee, or a reflective thinker. • To make the thinking process of students visible. Teachers can “lurk”, an internet term which means to read messages but not comment on them, behind students and see their thought process. • Allows for individual one-on-one attention to help students excel. • Allows for answering a question once and forwarding it to others so they do not have to answer the same question over and over. This saves a lot of time. • Email allows the instructor to assign group projects and students can participate more than ever before. Email even makes it possible for students across America to participate in the same academic virtual case study!
Portable Devices “Over the past decade, progress in Portable Information Devices (PIDs) has revolutionized telecommunications, information engineering, and entertainment systems. PIDs have become an essential part of everyday life and business. They make it possible to have vastly enhanced lifestyles - from basics such as reading, note taking, or listening to music, to crunching numbers, watching videos, and following news and sports events while on the go. Today's PIDs include cellular phones, personal digital assistants, medical devices, intelligent clothing, and iPods. Some devices provide built-in organizers for shopping lists, scheduling and appointments, phone numbers, address books, customer contacts, even games and video display.” www.ieee-portable.org
The First Portable Device The Past In 1981 the world saw the first portable device, the Osborne 1. It cost $1,795 and weighed around 25 pounds. The purchasing power of $1,795 during 1982 was the equivalent of $4,045.40. However, the Osborne 1 came with $1,500 of free software installed. It had a five inch monitor and had 64kb of memory and two 91kb drives. It also had a 4 Mhz processor and you could purchase an internal battery pack so that it would not have to be plugged in to work. Today Portable devices today are far more advanced. The newly released Apple Air costs $1,800, and it comes stock with 2 GB of RAM, an 80 GB hard drive, and a 1.6 GHz processor.
Portable Devices: What people are saying… The PEP (Palm Education Pioneers) teachers concluded that the main benefits to the student were increased time using the technology, increased student motivation, increased collaboration and communications, and benefits from having a portable and accessible personal learning tool. Likewise, 67% of student teachers felt that the PDAs increased student motivation and interest, 71% felt that they increased the ability to collaborate and communicate, and 80% of the student teachers increased their productivity by having a portable and accessible learning tool. • An estimated 95% of college students will show up to class with some type of electronic device. This creates added opportunities for academic dishonesty. A variety of responses were added to stop cheating with the portable devices: • Ban electronic equipment during exams • Create multiple versions of a test • Embrace wireless technology, but control it Visit blackberry.com
Portals An entrance, entry point, or means of entry -bnet.com “At the most basic level, portals gather a variety of useful information resources into a single, ‘one stop’ Web page, helping the user to avoid being overwhelmed…”(Looney & Lyman, 2000) Potential Issues: The system must be able to differentiate between a John Doe and a Dr. John Doe who has access to sensitive material. It is very difficult to organize an infrastructure and institutional information and services to perform this way. Campus specialists are likely to be displaced. In order to truly make web-based services user friendly and compatible with self-services and role-based ideals, users cannot have multiple user IDs and passwords. Institutional policies will be stretched into new shapes and configurations by these technologies and ethical, legal, and policy constraints concerning student information will be called into question. Why it’s important: Throughout our history, colleges and universities have described themselves as communities of scholars. Creative, web-sophisticated, commercial, and academic organizations are harnessing the evolving technologies and new organizing principles to create powerful and compelling communities. When the communities are created they reinforce stakeholder loyalties in ways our traditional campuses do.
Portal Information Delivery • Colleges and universities both compete and realize the full benefits of their investments in data warehouse, enterprise systems, and other elements of the campus infrastructure • Integrate information, services, and infrastructure across a seamless and easy-to-navigate web interface • Regulation of advertising on institutional websites • Creating portals that remain compelling to users but does not violate institutional privacy policies • Integrating physical and virtual sites to foster social and intellectual interactions Pros VS Cons
Puzzle Pieces Technology has been used to address many campus safety and security problems while at the same time creating new vulnerabilities. Recruitment Accessibility Information Delivery Distance Learning Safety and Security
Keeping People Safe in a New Generation • On April 17th, 2007, a deadly shooting at Virginia Tech resulted in the death of 33 people. • February 8th, 2008, a woman entered a Louisiana Tech classroom and shot two people before shooting herself. • February 14th, 2008, 22 people were shot with a death toll of six during a classroom shooting at Northern Illinois University.
Rice University used a similar system in August 2007 to warn of floods on campus, reaching about 60% of people on campus. Can Technology Prevent Tragedy? Text Messaging and Email Alert Systems • In 2007, more than 100 colleges had signed up for text and instant message systems via 3n, a community alert company.
Community Alert Systems • People tend to hang up on computerized voice messages • Enrollment is voluntary, resulting in a smaller reach • Text messages reach students more quickly than emails • More than 90% of students carry cell phones • Students can be reached at anytime, anywhere Pros VS Cons
Identity Theft “Security is, I would say, our top priority because of all the exciting things you will be able to do with computers. If we don't solve these security problems, then people will hold back. Businesses will be afraid to put their critical information on it because it will be exposed.” - Bill Gates • According to the Federal Trade Commission, close to 10 million Americans fell victim to identity theft in 2003. • More than a dozen campus security breach incidents have occurred in January 2008. • In 2006, 30% of colleges stated that security was their top technology-related concern.
Given the percentage of growth, the reality is that most of us will become the victim of identity theft sometime in our lives, if not multiple times. - Linda Goldman-Foley, Executive Director Identity Theft Resource Center College students are uniquely vulnerable to identity theft because of the public availability of their personal information, their easy access to credit, and their lack of attention to credit issues. University of Minnesota Parent Program Connection
Identity Protection • Many colleges are hiring chief security officers to develop network protection policies. • Schools are requiring software scans, such as antivirus and anti-spyware, before allowing connection to the network. • The University of Texas is moving beyond password-based security for services like registration and grade access by adding extra steps to the log on process.
Social Security Numbers • Created in 1936 and has since become a national identifier. • The theft of a SSN can result in the use of bank accounts, credit cards and other personal information. • 2003, Georgia Tech became the first college in Georgia to end the use of Social Security numbers as identification. • Currently there are about 20 states lacking laws against this liberal use of Social Security Numbers.
Puzzle Pieces Recruitment Accessibility Information Delivery Safety and Security • In the beginning, distance learning involved mail- and video- based courses. Now, online course enrollment is growing faster than ever. • 62% of four-year colleges offered distance learning courses in 1998. • 87% of four-year colleges offered distance learning courses in 2004. • In 2006, nearly 20% of all postsecondary students took at least one online course. Distance Learning
Distance Learning “Technology works best when it is solving a problem that people have come up against.” - Robert Zemsky, Learning Alliance for Higher Education “Technology is the fuel on which distance education runs and is a primary focal point in virtually all distance education professional organizations and publications.” (Dare, Zapata, Thomas 2005) “Distance learning can help solve two fundamental problems: Time and Space.” - Gene Maeroff, Hechinger Institute on Education and the Media, Columbia University
Why Students Choose Distance Learning • 76.2% work schedule accommodation • 42.3% family obligations • 42.1% live too far away • 16% financial situation (Dare, Zapata, Thomas 2005) Distance learners are a segment of the student population that can no longer be ignored by the student affairs profession. Originally, distance learners were primarily older and limited by family obligations, but as technology increases, so will the population of traditional demographic students earning degrees via distance learning.
Student Affairs & Distance Learning: Strengthening the Bond • Distance learners benefit from a feeling of connection to their institution just as traditional learners do. • Instant Messaging, Email and Video Conferencing can assist in person-to-person interaction. • Online services should be interactive, not just information-based. • Some existing programs can be adapted for online learners, but administrators should not shy away from creating other services specifically for this population.
Distance Learning • Not all courses and schools are created equal • Difficulty reaching students and creating engagement • Reliant on technology • Self-teaching with less involvement from faculty • Less structured time • Increased access and choices • Promotes lifelong learning • Anonymity leads to more comfort • Flexibility of time • Self-directed for independent learners Pros VS Cons “E-learning will never, and should never, be the dominate method of educating students, but it will be a fixed part of the delivery system of higher education.” -Gene Maeroff
Completing the Puzzle Recruitment Accessibility Information Delivery Safety and Security Distance Learning • Students now use computers in their college search and application process. Instant Messenger, internet blogging and online tours have revolutionized the recruitment process. • Thanks to technology, more students than ever are able to benefit from a college education. Technology and Universal Design will only increase these numbers. • Computers deliver a wealth of new ways to reach and educate an increasingly diverse student population. The profession of student affairs should be prepared to cater to the unique needs of these students. • Students communicate with their professors and each other in many ways. Thanks to Facebook and personal devices, they are always connected. • Technology has been utilized to notify the community in the case of an emergency and help secure the campus. However, with the growth of technology and information access, there is an increase in identity theft risk.
References All-electronic admissions. (2006, June). Recruitment & Retention in Higher Education, Retrieved February 16, 2008, from Professional Development Collection database. Anton, C. (2006, April). Student blogs in recruitment. Recruitment & Retention in Higher Education, 20(4), 1- 2. Retrieved February 16, 2008, from Professional Development Collection database. The Beloit Mindset List. (2007). Retrieved February 16, 2008, from http://www.beloit.edu/~pubaff/mindset. Carnevale, D. (2006, August 4). U. of Texas may add second layer of security to foil hackers. The Chronicle of Higher Education 52(48). A27. Retrieved February 15, 2008, from www.chronicle.com/weekly/v52/i48/48a02702.htm. The Chronicle of Higher Education. (2007). E-learning: Successes and failures. Retrieved February 15, 2008, from http://chronicle.com/weekly/v53/i18/18b02001.htm. Dare, L., Zapata, L., & Thomas, A. (2005, Winter). Assessing the needs of distance learners: A student affairs perspective. New Directions for Student Services, Retrieved February 16, 2008, from Academic Search Elite database. Distance learning benefits. Retrieved February 16, 2008, from http://www.distance-learning-college-guide.com/distance-learning-benefits.html. Fischman, J., & Foster, A. (2007, April 27). New phone technologies can help colleges communicate campuswide in emergencies. Chronicle of Higher Education, 53(34), A16. Retrieved February 6, 2008, from Academic Search Elite database. Floyd, D., & Casey-Powell, D. (2004, Winter). New roles for student support services in distance learning. New Directions for Community Colleges, 2004(128), 55-64. Retrieved February 16, 2008, from Academic Search Elite database. Foster, A. (2006, January 6). Technology: Safeguarding networks is priority no. 1. Chronicle of Higher Education 52(18), A11. Retrieved February 16, 2008, from Academic Search Elite database. Foster, A. (2007, October 5). After Va. Tech, campuses rush to add alert systems. Chronicle of Higher Education54(6), 3-3. Retrieved February 16, 2008, from Academic Search Elite database. Galanaki, E. (2002). The decision to recruit online: A descriptive study.Career Development International, 7(4), 243-251. Gregory, P. & Read, J. Using GroupWise to stimulate academic discussion with computing students. Retrieved on February 16, 2008, from http://www.chici.org/references/using_groupwise_to_stimulate.pdf. Handheld messaging with GroupWise Mobile Server, powered by Intellisink. Retrieved February 16, 2008, from http://www.novell.com/products/groupwise/mobileserver/. Horwitz, P. & Tinker, R. (2008). Universal design with technology: Universal design for learning will transform math education. Retrieved February 16, 2008, from http://www.concord.org/publications/newsletter/2005-spring/universal.html. How IM and virtual tours are shaping student recruitment. (2004, June). Recruitment & Retention in Higher Education, Retrieved February 16, 2008, from Professional Development Collection database. Katz, R. N. (2002). Web portals and higher education: Technologies to make IT personal. San Francisco: Jossey-Bass. Laptops help recruit and retain students, paper says. (2005, September). Recruitment & Retention in Higher Education, Retrieved February 16, 2008, from Professional Development Collection database. Lederman, D. (2008). We get no respect – Well, maybe a little. Retrieved February 16, 2008, from http://www.insidehighered.com/news/2008/01/24/online. Looney, M.A. & Lyman, G.P. (2000). Portals in higher education: What are they, and what is their potential? EDUCAUSE review 35(4), 29-36. Olive, B. Pros and cons of distance education. Retrieved February 16, 2008, from http://www.helium.com/tm/788046/imagine-degree-comforts-think. Othman, R. M. & Musa, N. (2006). E-recruitment practice: Pros vs. cons. Public Sector ICT Management Review, 1(1), 35-40. Read, B. (2004). Wired for cheating. The Chronicle of Higher Education. Retrieved February 14, 2008, from http://chronicle.com/weekly/v50/i45/45a02701.htm. Read, B. (2007, November 2). 5 ways sloppy campuses can clean out personal data. Chronicle of Higher Education, 54(10), 35-35. Retrieved February 6, 2008, from Academic Search Elite database. Rose M. What’s behind the explosive growth in distance learning? Retrieved February 16, 2008, from http://ezinearticles.com/?Whats-behind-the-Explosive-Growth-in-Distance-Learning?&id=49691. Santovec, M. L. (2005). IM in recruitment. Recruitment & Retention in Higher Education, 19(1), 1-2,8. Stiller-Rikleen, L. (2007, May 11). Virginia Tech: the Challenge of Assuring Safety. The Chronicle of Higher Education, 53(36). B14. Retrieved February 15, 2008, from www.chronicle.com/weekly/v53/i36/36b01402.htm. Vaas, L. Security watch. eWeek [serial online]. October 22, 2007:64, 64. Available from: Academic Search Elite, Ipswich, MA. Accessed February 6, 2008. Wangemann, P., Lewis, N., & Squires, D. (2003, November). Portable technology comes of age. T H E Journal, 31(4), 26-32. Retrieved February 16, 2008, from Professional Development Collection database. Thank you.