98%
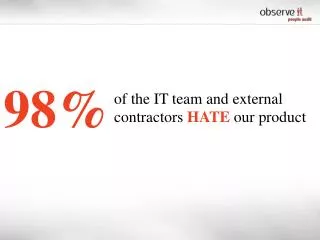
98%. of the IT team and external contractors HATE our product. of data breaches are undetected by the breached organization. 85%. Verizon Data B reach R eport 2013. Employees with legitimate access to enterprise information assets are i nvolved in most security violations. “. ”.

98%
E N D
Presentation Transcript
98% of the IT team and external contractors HATEour product
of data breaches are undetected by the breached organization 85% Verizon Data Breach Report 2013
Employees with legitimate access to enterprise information assets are involved in most security violations “ ” Gartner, Conduct Digital Surveillance Ethically and Legally: 2012 Update, Andrew Walls, March 27, 2012
Surveillance Cameras+Law Enforcement Deter, Detect & Investigate Crime
Intelligent virtualcamera with malicious intent detectors… The IDEA VirtualCamera
Big BROTHER Watch, record and transcribe anything privileged users or external consultants access remotely Virtual Camera Virtual Camera
No EXCUSE It wasn’t me…I didn’t do anything
Report of Abnormal ACTIVITIES Who is displaying confidential files over a WebEx session?
Snoop DETERRENCE Stopmalicious insidersfrom peeking at unauthorized data without leaving behind evidence
Provide security officers peace-of-mindabout how confidential data is used by external contractors and privileged users