Signatures for Network Coding
Signatures for Network Coding. Denis Charles Kamal Jain Kristin Lauter Microsoft Research. Network Coding Set-up. A directed graph of users G A server (source) distributing content Content is divided into packets and represented as vectors in a vector space

Signatures for Network Coding
E N D
Presentation Transcript
Signatures for Network Coding Denis Charles Kamal Jain Kristin Lauter Microsoft Research
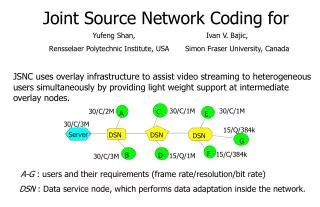
Network Coding Set-up • A directed graph of users G • A server (source) distributing content • Content is divided into packets and represented as vectors in a vector space • Each node receives linear combinations of packets from other nodes • At each node, new linear combinations of received packets are formed and sent out along new edges • Extra bits keep track of which linear combination at each step
Pollution attacks • A malicious node can inject garbage into the distribution network • If undetected, the garbage will pollute the whole network, as meaningless packets are combined with others and redistributed • Signatures on received packets can be used to check for garbage
Assumptions • Public key digital signatures • Only the server possesses the secret key for signing • Any node can verify signatures using public information • So how can nodes re-sign linear combinations of received packets?
Homomorphic signature scheme • Our solution is based on: • Elliptic curves • Bilinear pairing (Weil pairing) • Homomorphic hashing of content onto points on the elliptic curve • BLS-type signatures (Boneh-Lynn-Schacham) • Security reduction to ECDLP (Elliptic curve discrete logarithm problem)
Elliptic curves over finite fields • Finite field Fq with q elements, A, B in Fq • Elliptic curve over Fq with equation y2 = x3 + Ax + B • E(Fq)={(x, y): y2 = x3 + Ax + B} Ụ ∞ has a group structure and a bilinear pairing • em : E[m] × E[m] alg(Fq)* satisfying • em(S1 + S2, T) = e(S1, T)e(S2, T) • em(S, T1 + T2) = e(S, T1)e(S, T2).
Homomorphic hashing and signing • Vectors (packets) with coefficients vi in Fp are hashed to linear combinations of public p-torsion points on E/Fq R1, · · · ,Rk, P1, · · · , Pd in E(Fq)[p] k=# of vectors, d = dimension of vector space • Server has secret keys for signing s1, · · · , sk and r1, · · · , rd in Fp signs the packet by computing the signature of hash ΣsiviRi +ΣriviPi • Server also publishes Q, sjQ and riQ • Q is another point in E(Fq)[p] which is linearly independent from the points R1,…,Rk, P1,…, Pd
Bilinearity of the pairing • Verification of signatures uses bilinearity of the pairing since em(siviRi, Q) = em(viRi, siQ) • Received valid signatures can be recombined to accompany new outgoing combinations of packets since the signature of the sum is the sum of the signatures
Security • Theorem: Finding a collision of the hash function h is polynomial-time equivalent to computing the discrete log on the elliptic curve E. • Fact: Forging signatures is as hard as the computational Diffie-Hellman problem on the curve E. • Our scheme establishes authentication in addition to detecting pollution.
Implementation • If we take the prime p 170-bits, this is equivalent to 1024 bits of RSA security. We can setup the system with q ~ p2. • Communication overhead per vector is two elements of Fp (the x and y coordinates of a point) = 340 bits. We can reduce this overhead to 171 bits at the cost of increasing computational cost. • Computation of signature of vector at an edge e is O(indeg(in(e)) operations in Fp. • Verification requires O((d+k) log2+εq) bit operations • Complete setup of the system at the server can be done in polynomial time (assuming a number theoretic conjecture of Hardy-Littlewood).