O.S security
E N D
Presentation Transcript
O.S security Ge Zhang Karlstad University
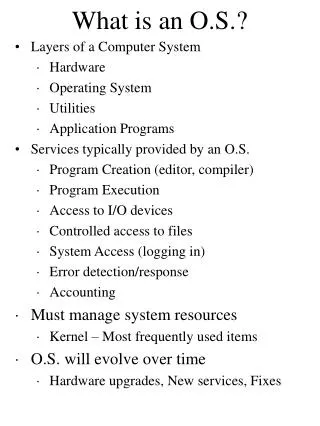
Outline • Why O.S. security is important? • Security schemes in Unix/Linux system • Security schemes in windows system
Why O.S. security is important? Applications: my sql, apache, open office, firefox, etc Operating system: Linux SUSE Hardware: memory, CPU, HD, etc • Application security can be bypassed from lower layer • Hardware layer is too narrow and inflexible • Application layer is too broad
Security schemes in Unix/Linux • Account security • User authentication • File system security • File access control • Management issues • Audit log • Environment variables • Manage the superuser
Account security (1) • User Accounts (/etc/passwd) • User name: a string up to 8 characters • User identities (UIDs) and group identities (GIDs) [Superuser (Root, UID=0)] • Unix does not distinguish between users with the same UID!!!! • Home directory • Shell root:x:0:0:root:/root:/bin/bash bin:x:1:1:bin:/bin:/bin/bash jim:x:500:100:Jim Smith:/home/jim:/bin/bash
Account security (2) • Shadow file (/etc/shadow) (only readable to the users with root privilege) • User name • Password (algorithm, salt, hashed password) • *: login is disabled • Empty: no password is required • Last password change • Minimum: the number of days left before the user is allowed to change his/her password • Maximum: The maximum number of days the password is valid (after that user is forced to change his/her password) root:$1$v3cNGjbW$WEvnoW8Cniswn3d:14523:0:99999:7::: bin:*:10933:0:99999:7::: jim::10933:0:99999:7:::
Account security (3) salt Password (plaintext) One-way function Password (encrypted) root:$1$v3cNGjbW$WEvnoW8Cniswn3d:14523:0:99999:7::: bin:*:10933:0:99999:7::: jim::10933:0:99999:7:::
Account security (4) • Groups • Users belong to one or more groups • To share files or other resource with a small number of users • Ease of user management (give privilege) • Group file (/etc/group) • Group name • Password • Group ID (GID) • Group list: members student:x:24:alice, bob, raj teacher:x:12:raj, nick
File system (1) • The inode: each file entry in a directory is a pointer to a data structure • mode: types of file and access rights • uid: who is the owner • gid: group which owns the file • atime: access time • mtime: modification time • itime: inode alteration time • block count: size of file • physical location
File system (2) • The type of the file: ‘-’ for regular file, ‘d’ for directory • File permissions • Link counter • Name of the owner and the group - rw-r--r-- 1 nick staff 1617 Oct 28 11:01 test.txt drwx------ 2 nick staff 512 Oct 25 17:55 tmp/
File system (3) • Owner (r, w, x), group (r, w, x), other (r, w, x) • Two ways to represent • String: rwxr--r-- • Octal number: 744 • Default permissions: 666 or 777 • (umask): a three-digit number specifying the rights that should be withheld • Default permissions AND NOT umask • For example: umask 777 (denies all)
File system (4) • Permission for directories • Read: find which files are in the directory (e.g., ls) • Write: add files or remove files • Execute: enter the directory and open files inside the directory (even for your own files)
File system (5) • “a real pain if you try and install a permanent file in someone’s directory.” • Sticky bit: restrict the right to delete a file. • only the file's owner, the directory's owner, or the root can rename or delete files. drwxrwxrwx 4 root sys 485 Nov 10 06:01 /tmp drwxrwxrwt 4 root sys 485 Nov 10 06:01 /tmp
File system (6) • Unix requires higher privilege temporarily to execute some operations • Change password • Open a port (0-123) • SUID (set userID), SGID (set groupID) • A user who is executing this program will get the privilege of the owner temporarily -rws--x--x 3 root root 16384 Nov 16 1996 passwd*
Processes • Each process has a process ID (PID) • Two pairs of UID/GID for each process • A real UID/GID • An effective UID/GID • The login process
File system (7) • To change the attributes • chmod • who: u, g, o, a • Permission: r, w, x, s, t • chmod 777 file • chmod o+r file • chown • chgrp
File system (8) • How to set? • Need a fourth number • 4??? set user ID on execution • 2??? set group ID on execution • 1??? set sticky bit
File system (9) • How to remove a file in a secure way? • Links • You removed the original file from its directory, but… • ncheck: list all links to a file • Furthermore, the file is not really deleted! • User wipe
File system (9) • Protection of devices • Unix treats devices like files • Devices commonly found in the /dev is: • /dev/console • /dev/men • /dev/kmem Devices should be world-unreadable and world-unwritable
Changing the root of the filesystem • Sandbox: access to objects outside the sandbox is prevented • chroot <directory> <command> • Changes the root directory from / to <directory> when <command> executes • For example, a web server
Search path • Shell: a command line interpreter • For easy-to-use: user input command without specifying the full pathname • Searchpath in the .profile • PATH=.:$HOME/bin:/usr:/bin:/usr/bin:/usr/local:/usr/new:/usr/hosts
Audit logs • /usr/adm/lastlog: records the last time a user has logged in • /usr/adm/utmp: records a list of users who are currently logged into a computer • /var/adm/wtmp: records every time a user logs in or logs out • /var/adm/acct: records all executed commands • Others: ps…
Manage the superuser • Superuser is the major weakness • Compromise the account • Weak password • Change UID to 0 • Crash the process with root privillege • Presentation • Admin should not use root as their personal account (using SU, SUDO) • Strong password protection
Windows security • Separation between user mode (ring 3) and kernel mode (ring 0) • User programs make API calls to invoke operating system services • Device drivers are running in kernel mode • Security subsystem • Log-on process (winlogon): the authentication process (winlogon.exe) • Local Security Authority (LSA): verification and auditing (lsass.exe) • Security Account Manager (SAM): user account database
Domains • Domains: to facilitate single sign-on and centralized security administration • A domain is a collection of machines sharing a common user accounts database and security policy • DC: domain controller
User authentication: interactive logon • Secure attention sequence CTRL+ALT+DEL • Winlogon.exe • Lsass.exe: verification • Start a shell (explorer.exe)
Key points (1) • The mechanism of user authentication in Unix. Where are the user’s account and password stored? • Root account • What is salt? How to use it and why it is important? • What is the “group” in Unix? Why to use it? • /etc/passwd, /etc/shadow, /etc/group • What are the A real UID/GID and An effective UID/GID? • What is an inode? • The permissions to access a file or a directory • umask • Sticky bit, SUID, SGID
Key points (2) • chmod • How to delete a file in a secure way? • Protection of devices • Search path • Audit logs in windows and unix • Security subsystem in windows • Why users should press CTRL+ALT+DEL to get a logon window in windows?