E-Discovery
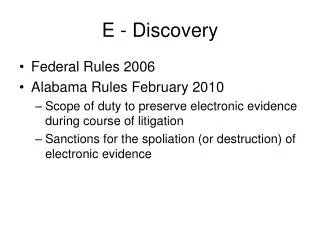
E-Discovery. ESI and E-Discovery Valid E-Discovery Plans Drafting/Granting Discovery Orders Case Studies. ESI & E-Discovery. Electronic Systems Information E-Discovery Process Goals of Discovery. ESI and E-Discovery requests are becoming a standard part of civil cases.

E-Discovery
E N D
Presentation Transcript
E-Discovery ESI and E-Discovery Valid E-Discovery Plans Drafting/Granting Discovery Orders Case Studies
ESI & E-Discovery • Electronic Systems Information • E-Discovery Process • Goals of Discovery ESI and E-Discovery requests are becoming a standard part of civil cases. 0101001101110000011001010110001101101001011000010110110001101001011100110111010001110011001000000110100101101110001000000100010100101101010001000110100101110011011000110110111101110110011001010111001001111001001000000110000101101110011001000010000001000100011010010110011101101001011101000110000101101100001000000100011001101111011100100110010101101110011100110110100101100011011100110000110100001010 ESI & E-Discovery E-Discovery Plans Court Orders Case Studies
Electronic Systems Information ESI & E-Discovery Electronic Systems Info… • The Digital Age • Electronic Hardware • Types of Information Extracted We use the term ESI to describe any information stored on electronics. At its core we are talking about 0s and 1s E-Discovery Process Goals of E-Discovery E-Discovery Plans Court Orders Case Studies
The Digital Age ESI & E-Discovery Electronic Systems Info… The Digital Age • Paper is hard to preserve, reference and search. • Electronic communication dominating workplace • Handwriting is slow and it is difficult to catch errors • Medical, financial and most other businesses moving to the paperless office. Paper is no longer the medium of choice. Typing has replaced writing. Electronic Hardware Information Extracted E-Discovery Process Goals of E-Discovery E-Discovery Plans Court Orders Case Studies
Electronic Systems/Hardware ESI & E-Discovery Electronic Systems Info… The Digital Age • Desktop Computers • Laptop Computers • Cell/Smart Phones • Tablets • Phone Systems • Video Cameras • Digital Key Systems Offices tend to have more electronics storing data than they have people. Electronic Hardware Information Extracted E-Discovery Process Goals of E-Discovery E-Discovery Plans Court Orders Case Studies
Information Extracted ESI & E-Discovery Electronic Systems Info… The Digital Age Electronic Hardware • Emails • Text Messages • Office Documents • Internet History • Social Media(Facebook, blogs, tweets) • Instant Messages (Skype, Yahoo, ooVoo) • Office Databases • Phone Conversations • Video Captures • Computer Use Logs The most requested information involves the Internet; emails and browsers. Information Extracted E-Discovery Process Goals of E-Discovery E-Discovery Plans Court Orders Case Studies
E-Discovery Process ESI & E-Discovery Electronic Systems Info… The Digital Age Electronic Hardware • Attorney: • Request for discovery of electronic systems information • Judge: • Drafts or approves order to define scope and terms • E-Discovery Team: • Identifies hardware possibly containing data • Preserves and collects the data from that hardware • Processes, reviews and analyses data • Produces findings to the court • Data and Digital Forensic Specialists • Analyze and summarize production • Provide expert opinions and feedback • Assist Attorneys in court The process for E-Discovery is often a give and take. Information Extracted E-Discovery Process Goals of E-Discovery E-Discovery Plans Court Orders Case Studies
Goals of ESI Requests ESI & E-Discovery Electronic Systems Info… E-Discovery Process • Find specific documents claimed to exist by the attorney’s client that support their position. • Prove that their client did not have or ever have documents, emails, images, etc. that they are being accused of possessing. • Prove the whereabouts of their client at a specific time. • Find documents that might exist or might have been deleted by the opposition that might discredit their position. • Show the opposition and/or client’s virtual persona in order to reinforce suspected real life activities. The goal is to find either documents entered by either party or find logs related to the use of the computer or system. Goals of E-Discovery E-Discovery Plans Court Orders Case Studies
Valid E-Discovery Plans ESI & E-Discovery Electronic Systems Info… E-Discovery Process Goals of E-Discovery • Identifying the Hardware • Preserving the Data • Collecting the Data • Processing the Collection • Review/Analyze for Accuracy • Production Recognizing a valid E-Discovery plan is necessary to avoid pitfalls such as data corruption. E-Discovery Plans Court Orders Case Studies
Identifying the Hardware ESI & E-Discovery E-Discovery Plans Identifying the Hardware Additional copies and backups of data on hardware may be discovered through the review stage. • Home Environment • Home Computers • Mobile Devices • Online Accounts/Social Media • Internet Service Provider Data • Office Environment • Central Servers that Store Data • Backup Systems • Desktops/laptops • Mobile Devices • Video/Voice and other recording devices Preserving Collecting Processing Review/Analyze Production Court Orders Case Studies
Preserving the Data ESI & E-Discovery E-Discovery Plans Identifying the Hardware • Placing the data on hold • Freezing the data in time • Seize hardware with no warning • Require shut down of system till matters are resolved • E-Discovery Team in “Read Only” mode • No Insert, Update or Delete instructions by team Preserving the data’s integrity requires a precise plan and clear documentation Preserving Collecting Processing Review/Analyze Production Court Orders Case Studies
Collecting the Data ESI & E-Discovery E-Discovery Plans Identifying the Hardware Preserving • Copy the Data Bit by Bit • Every “a” = 01100001 is copied perfectly to another drive as 01100001 • Bits are verified as accurate by copy software • Collected Data verified to be accessible • Original data (hard drives) never used in processing • Data can be collected live or offline The data from the hardware is copied using trusted forensic tools and software. Collecting Processing Review/Analyze Production Court Orders Case Studies
Processing the Collected Data ESI & E-Discovery E-Discovery Plans Identifying the Hardware Preserving • Search the drive for keywords, word patterns and/or date ranges • Use common data tools to find data in structured data files • Flag discovered data with ID Numbers Collecting Processing the data requires the use of automated software combined with skilled query writers Processing Review/Analyze Production Court Orders Case Studies
Review/Analyze for Accuracy ESI & E-Discovery E-Discovery Plans Identifying the Hardware Preserving • Look for irrelevant data flood • Evaluate completeness of data, possible oversights • Review the readability of the collection • Look for hidden or encrypted data Collecting Processing This requires knowledge of data structure and a clear unpartisan review of the data’s relevance and completeness. Review/Analyze Production Court Orders Case Studies
Production ESI & E-Discovery E-Discovery Plans Identifying the Hardware Preserving • Index all discovery for court use • Produce in standard formats like; PDF, TIFF and at times, print • Production as seen by the software used to create the file • Organize the production in logical sequences for readability Collecting Processing The production need to be well organized, indexed and in context to the software used to create the data Review/Analyze Production Court Orders Case Studies
Drafting/Granting Discovery Orders ESI & E-Discovery E-Discovery Plans Identifying the Hardware Preserving The order must carefully balance ensuring that all relevant data can be found with limiting the flood of data produced and costs incurred on both sides. • Defining a scope • Common Pitfalls • Abuses of the System Collecting Processing Review/Analyze Production Court Orders Case Studies
Defining a Scope ESI & E-Discovery E-Discovery Plans Court Orders Defining a Scope • Define possible related data • Eliminate specific hardware parameters • Set timeframe for stages of completion • Define expected output format • Determine number of production copies needed • Plan for Intellectual Property and confidential information filtering The scope narrows down the details of what is to be collected and produced. It clarifies the task for the E-Discovery team to respond to. Common Pitfalls Abuses of the System Case Studies
Common Pitfalls ESI & E-Discovery E-Discovery Plans Court Orders Defining a Scope • Cost of production and “low ball” bids • Time delays caused by unorganized E-Discovery teams scrambling to learn as they go through due process. • Hardware and software errors • Uncooperative I.T. staff from the other party, evasive disclosure. Pitfalls can be reduced by clear communication and expectations set in the order and well organized E-Discovery teams. Common Pitfalls Abuses of the System Case Studies
Abuses of the System ESI & E-Discovery E-Discovery Plans Court Orders Defining a Scope • E-Discovery Trolls • Similar to patent trolls, their goal is to force settlements by threatening “shut down” of business critical systems. • Data Flooding • The goal is to flood the opposite party with so much unreadable data that it masks the relevant data • Greedy E-Guess • These are IT based individuals who may undercut valid E-Discovery companies to entice unsuspecting lawyers into a “good deal”. Later in the process they continually request more and more finances and eventually break the client’s finances with little or no accurate production to show for it. Common Pitfalls Watch for broad requests that will cripple the opposite party with cost and excessive data to cause review time delays. Abuses of the System Case Studies
Case Study ESI & E-Discovery E-Discovery Plans Court Orders Defining a Scope • Wrongful Termination • Company terminated employee for not completing and sending a critical email and attachment to VIP customer. • Former employee claims the computer system must have lost the email because he sent it on time. Common Pitfalls With so much information stored on computers, its no wonder just about every type of case can involve ESI requests. Abuses of the System Case Study
Wrongful Termination ESI & E-Discovery E-Discovery Plans Court Orders Case Study • Request is made by the former employees attorney to disclose electronic data related to the email and the attachment in question. • The goal: show that the client did send the email and attach the critical document • No specific hardware is named • Requested that all possible relevant electronics be placed on hold. The Request The case of the lost email. Was it computer error or the employee not doing their work? The Order E-Discovery Production Data Specialist Report
Wrongful Term… The Order ESI & E-Discovery E-Discovery Plans Court Orders Case Study • Electronics that store email and files that the former employee had access to during the timeframe in question. • Email systems and file data storage systems where the attachment and emails would have been processed or saved according and active during the timeframe in question. • Data may be live collected from active servers or offline collected. • If additional electronics are identified as possibly containing data during the e-discovery process. Those electronics may be placed on hold as an amendment to this order. • Data may be collected from in-house e-discovery storage as long as the collection process is validated by both parties e-discovery teams. • The emails and files produced are limited to data created between 1/1/2001 to 1/15/2001 • Both parties agree to the allowance of the e-discovery team to act as expert data analysts to give opinion pertaining to the history and existence of that email and attachment in question. The Request Narrowing the scope and ordering the discovery of ESI. Refer to the handout for a complete list of items to be covered in the order The Order E-Discovery Production Data Specialist Report
Wrongful Term….E-Discovery Process ESI & E-Discovery E-Discovery Plans Court Orders Case Study • Identifying and Preserving • E-Discovery Team identifies electronics • former employees desktop, the email server, the file server and the email filter device as possibly containing relevant data. • Collection • Drives are collected and copied offline, onsite and put back into use. • Processing • Keywords used in the email, recipients names, senders name, emails sent around the time in question, documents containing keywords all discovered. • Review/Analyze • Other files in containing folders and versions of files found are reviewed • Alternate email logging systems are reviewed for search ability • Email found with search parameters was recorded as successfully sent by the company email server. Recipients server and intended client electronics data requested to verify receipt. • Production • PDF, TIFF and Printed Copies are made for 5 recipients The Request The Order The E-Discovery team identifies valid hardware, collects the data, and produces the requested output E-Discovery Production Data Specialist Report
Wrongful Term….Data Specialist Report ESI & E-Discovery E-Discovery Plans Court Orders Case Study • The Data Specialist places the data in context and creates a time-line chart show the history of the file and email in question. • The chart show the file being created and edited before and after the date and time the email and another similar to it was generated. • The first email was successfully sent to the client but did not contain the completed attachment. The attachment was named the same as the final document but was blank. • The client’s email server removed the blank attachment as spam and placed the invalid email on hold • The full email was also created on the employees machine with the attachment but was simply copied to the sent items folder and though the email showed it having been done earlier that day, metadata shows the file was created late that evening, after the deadline. • Conclusion, the former employee failed to complete the attachment and attempted to cover up the error by sending a blank attachment email and later trying to falsify a completed email at a later time. The Request The Order The specialist places all the produced data in context and paints a picture of the history of the email and attachment E-Discovery Production Data Specialist Report
E-Discovery ESI and E-Discovery Valid E-Discovery Plans Drafting/Granting Discovery Orders Case Studies