Chapter 4: Network Administration for Windows, Linux, and VMware
Chapter 4: Network Administration for Windows, Linux, and VMware. Lecture Materials for the John Wiley & Sons book: Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions. System Administration Skills.

Chapter 4: Network Administration for Windows, Linux, and VMware
E N D
Presentation Transcript
Chapter 4: Network Administration for Windows, Linux, and VMware Lecture Materials for the John Wiley & Sons book: Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions
System Administration Skills This chapter provides a introduction to the most commonly needed skills. These skills are the foundation you need to become a hands-on professional. • Administrator and Root Accounts • Hardware Installation • Re-Imaging Operating Systems • System Protection / Anti-Malware • Networking Setup • Application Installation and Archiving • System Management Controls / Settings • Remote Login / Management • User Administration • Services Management e.g. DNS • Disk Mounting • Moving Data Between Systems on Networks • Advanced File Formatting • Disk Backup and Reformatting • Firewall Configuration • Virtual Machine Conversion and Migration Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions
System Admin Interfaces • On Windows • Using menus • Start>Control Panel • Start>Run then type mmc • Start>Control Panel>View by: Small Icons (pulldown)>Administrative Tools • Or use the Windows Command Line Interface (CLI): Start>Run>All Programs>Accessories>Command Prompt • CLI denoted in this book with prompt: C:\> • On Linux • Use a command line shell, e.g. Bash • Bash denoted in this book with prompt: # • Use menus to access settings screens on desktop, e.g. KDE, Gnome Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions
Administrator and Root Accounts • All users should normally use unprivileged accounts, e.g. for Internet surfing • Administrative operations should be effectively separated from other user activities • If a privileged account is attacked, the entire network could be compromised • Internet-based malware can use cross-site attacks to access administrative tabs in the same browser, e.g. controlling network devices, electrical power systems,… • See the antipattern Webify Everything Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions
Hardware Installation Steps for installing a pedestal computer system for end user computing • Gather the hardware components • Guide the cabling between (floor) pedestal and desktop • Connect network, monitor, mouse, and keyboard cables • For a new Uninterruptable Power Source (UPS) open the device cabinet and connect the battery cable • Connect the electrical pigtail to the pedestal, then to the UPS • Verify your work, check all connections. In any situation when systems are not working, always check the physical connections first! Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions
Re-Imaging Operating Systems • Installation Sequence for Windows/Linux • Obtain installation disks and install hardware • Disconnect the system from the network • Power on the machine and open CD/DVD drive, insert the installation disk • Follow on-screen instructions for installation • Insert the DVD containing device drivers (or download drivers from Internet). Install drivers for all devices, e.g. monitor, keyboard, mouse… • Reboot system and follow the next steps/slides • Windows Activation • Microsoft requires that a new installation be activated. This can be done on the Internet. Failing that, you can activate with a phone call to an interactive voice response (IVR) system. Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions
System Protection / Anti-Malware Host-Based Security Protections can include: • Antivirus • Anti-spyware • Firewall • Intrusion detection • Intrusion prevention • Blacklisting • Real-time integrity checking • Periodic policy scanning • Rootkit detection • Patch management Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions
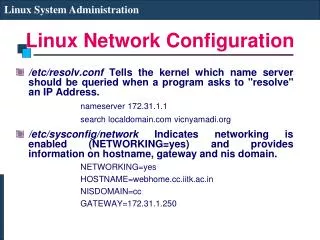
Networking Setup • On Windows, network setup uses Graphical User Interfaces (GUI) accessed from the Control Panel • On Linux • If Dynamic Host Configuration Protocol (DHCP) is running, setup networking with command: ifup eth0 • Manual networking setup steps include: • Setup Domain Name Server (DNS): • # echo “nameserver 10.10.100.100” >> /etc/resolv.conf • Configure interface: # ifconfig eth0 10.10.100.10/24 • Add a gateway: # route add default gw 10.10.100.1 • Command syntax may vary with your Linux distribution Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions
Application Installation • On Windows, simply run the installer program and follow onscreen instructions • On Linux, installation commands vary by distribution, for example: • Debian: # dpkg application.deb • Red Hat: # rpm application.rpm • Or use the Yum Extender app • Ubuntu use apt-get command Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions
Remote Login / Management • Connecting to a Windows machine • Connect to other Windows machines: • Start>All Programs>Accessories>Remote Desktop Connection • From Linux, connect to Windows with command: rdesktop • Connecting to a Linux machine • On the remote machine, start SSH from KDE: K>Services>SSH>Setup SSHD then Start SSHD • Connect: # ssh MyUserName@10.10.100.10 Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions
User Administration • On Windows • Windows Client: select User Accounts in the Control Panel • Windows Server: use the MMC>Local Users • Alternatively, use the CLI command: net user • On Linux • Create accounts with command: • # useradd –d /home/MyAccount MyAccount • Modify accounts with command: • usermod –G admin –a MyAccount • Other commands: userdel, groups, and view or modify the file /etc/passwd Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions
Services Management • On Windows • Start>Run then typeservices.msc • The services management GUI will open • Also the CLI commands netsh and sc • On Ubuntu, for example, configure CUPS • # apt-get install cups • Add to /etc/cups/cupsd.conf <Location /admin> Allow from 127.0.0.1 </Location> • # /etc/init.d/cups start • On Red Hat, use the service command • # service iptables stop • #service iptables start Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions
Disk Mounting • On Windows • Disk will automount after you attach USB • Unmount by detaching USB • On Linux • Mount • # fdisk –l • # mkdir /mnt/sda1 • # mount /dev/sda1 /mnt/sda1 • Unmount • #umount /mnt/sda1 Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions
Moving Data Between Systems on Networks • Moving data is very important skill for cybersecurity testers, i.e. moving test data • Between Windows • Use file sharing, right click on a folder, Properties>Sharing tab • Between Linux and Windows use CIFS • # mkdir /mnt/MyShare • # mount –t cifs //10.10.100.10/MyShare /mnt/MyShare –o user=MyUser • Between Linux – use command: sftp Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions
Converting Text Files • This skill is closely related to moving data • Converting text files between Linux and Windows and MacOS formats • # dos2unix file.txt • # unix2dos file.txt • # mac2unix file.txt … etc Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions
Disk Formatting • On Windows • Control Panel>Administrative Tools>Computer Management • Use the GUIs under Disk Management • On Linux • A typical formatting procedure: # fdisk –l – locate new disk /dev/sda # fdisk /dev/sda – enter commands to create disk table fdisk: m – display help fdisk: o – create new partition table in RAM fdisk: n – new partition creation fdisk: p – partition choice fdisk: 1 – choose first partition (sda1) fdisk: <Enter> – default: 1st cylinder is 1 fdisk: <Enter> – default: Last cylinder fdisk: p – print partition table fdisk: w – write table to disk and exit # mkfs –V /dev/sda1 – format the data partition # mkdir /mnt/sda1 – create mount directory # mount /dev/sda1 /mnt/sda1 – mount disk to test it Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions
Firewall Configuration A typical command sequence for a CISCO ASA 5000 series: $ enable Password: # show run # config t (config)# interface vlan 2 (config-if)# nameif inside (config-if)# security –level 100 (config-if)# ip address 10.10.100.1 255.255.255.0 (config-if)# no shut (config-if)# exit (config)# (config)# interface vlan 3 (config-if)# nameif outside (config-if)# security –level 0 (config-if)# ip address 192.168.10.2 255.255.255.0 (config-if)# no shut (config-if)# exit (config)# route outside 0.0.0.0 0.0.0.0 192.168.10.1 (config)# int e0/1 (config-if)# switchport access vlan 2 (config-if)# speed 100 (config-if)# duplex full (config-if)# no shut (config-if)# exit (config)# int e0/2 (config-if)# switchport access vlan 3 (config-if)# speed 100 (config-if)# duplex full (config-if)# no shut (config-if)# exit (config)# wr mem (config)# exit # show run # exit Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions
Virtual Machine Conversion and Migration • VM conversions/migrations are frequent activities in security test labs • Example: Convert a running VMware image on ESXi to a VMware Player image • On Windows, the VMware Converter Server and Converter Agent are Windows services, created when Converter was installed. Verify that they are started. • Start VMware Standalone Converter application. 2. Click the Convert Machine button. 3. From the pull-down menu select Powered-On Machine and then select the A Remote Machine radio button. 4. Enter a target IP address and login credentials. 5. Select the OS family. 6. Set up and run the SSH service on the target machine. 7. Select VMware Infrastructure and Virtual Machine as the destination. 8. Enter the VM name and then click Finish. Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions
Additional Network Administration Knowledge • As a hands-on cybersecurity professional, especially in security test labs, you will constantly research new commands, new procedures, and new technologies • This chapter provides a basic grounding in these skills, but continued mastery of sys admin skills is a lifelong learning endeavor • Remember this… Keep detailed notes! • Search for the answers and you will find them! • Google is your friend! • You are NOT Magellan! • Keep learning every day • Tackle these challenges TOGETHER with your colleagues and friends! That’s the most fun way! Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions
Cyber Security: Managing Networks, Conducting Tests, and Investigating Intrusions REVIEW Chapter Summary