Handy Penetration Testing tools
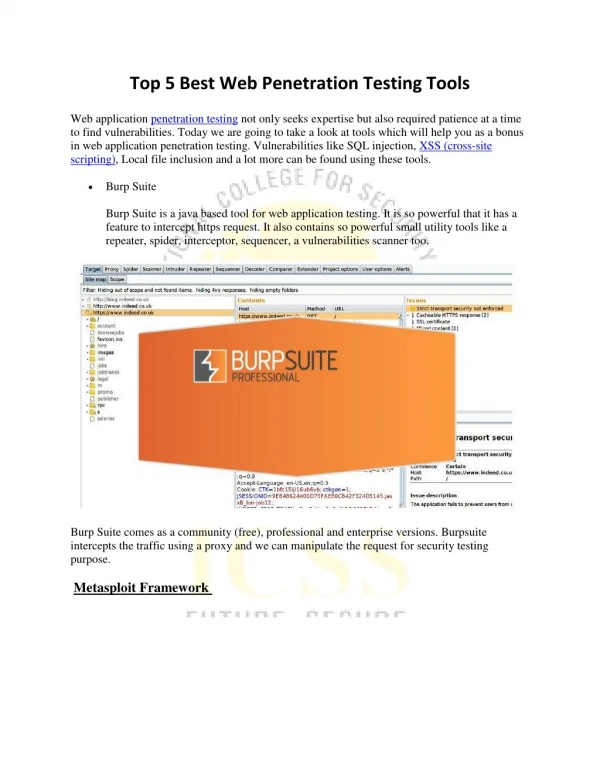
Often the overall security of a software application is impacted due to loopholes in the operating systems, networks, system configuration, third-party services, or endpoints. The QA professionals perform penetration testing to identify the loopholes that make the software vulnerable to targeted security attacks by gaining access to the application’s features and data.

Handy Penetration Testing tools
E N D
Presentation Transcript
Often the overall security of a software application is impacted due to loopholes in the operating systems, networks, system configuration, third-party services, or endpoints. The QA professionals perform penetration testing to identify the loopholes that make the software vulnerable to targeted security attacks by gaining access to the application’s features and data. The QA professionals need to combine manual and automated ethical hacking techniques to identify all security vulnerability in the application. But they must perform penetration testing continuously throughout the software development life cycle (SDLC) to make the application 100% secure. That is why; it is important for software QA testing professionals to know the pros and cons of handy penetration testing tools.
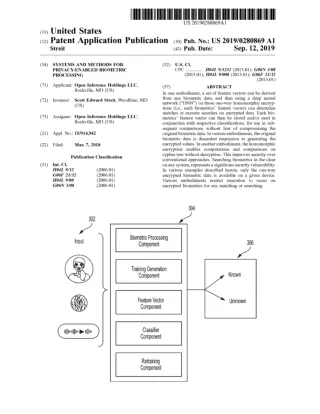
Overview of 4 Widely Used Penetration Testing Tools METASPLOIT The commercial penetration testing tool supports Windows, Linux and OS X. It can also be used for identifying the security vulnerabilities in web application, servers and networks. Metasploit is designed based on a concept called exploit. Exploit is written as a code that can enter the targeted system by surpassing its security features. After entering into the system, exploit run a code called payload additionally to perform a variety of operations on the targeted system. Hence, Metasploit makes it easier for testers to perform end-to-end penetration testing based on custom code. At the same time, it allows testing professionals to use a command-line tool and a GUI clickable interface.
WIRESHARK Wireshark is designed specifically as a network protocol analyzer. It enables testers to gather in-depth information about a wide range of network protocols. In addition to supporting multiple operating systems, Wireshark provides a three-pane packet browser, reads and writes different capture file formats, decompresses compressed file formats, and provides decryption support for many protocols. Also, it allows users to browse the captured network data efficiently, use advanced display filters, and simplify test data analysis by applying color rules to packet lists.
W3AF As a web application attack and audit framework, w3af is designed with features to identify and exploit all vulnerabilities in web applications. It supports Windows, Linux and OS X, and allows users to choose from both console and graphical user interfaces. At the same time, the tool allows users to integrate web and proxy servers into the code. Also, it facilitates fast HTTP requests, along with allowing testers to inject payloads into different types of HTTP requests.
CORE IMPACT PRO The commercial penetration testing tool enables users to assess the security of their software through advanced techniques used by cyber criminals. Core Impact Pro further allows software QA testers to use both command-line and GUI clickable interfaces. But it supports only Windows platform. The testers can use Core Impact Pro to identify security vulnerabilities in web application, mobile apps, and network and network devices. The wireless penetration testing capabilities of the tool further enables users to assess the vulnerability of the application to the real-work security attacks executed over Wi-Fi networks.