Understanding Message Integrity Through Cryptography Basics
250 likes | 359 Views
Learn about message integrity checking, cryptographic hashing, digital signatures, and solving identity problems with asymmetric cryptography. Dive into hands-on labs using Cryptool and nslookup to understand practical demonstrations.

Understanding Message Integrity Through Cryptography Basics
E N D
Presentation Transcript
T101 Networks 13 – Message Integrity
Labs • practical demonstrations • part 3 is based on Cryptool • Part 2 is based on nslookup • review Lab 10 • find the “real” TTL of an A record • set type=ns, then enter the domain to get a nameserver • server nameserver • set debug • set type=a, then do the query • find the first mail exchanger for an email address
Lesson Objectives • describe message integrity checking • describe cryptographic hashing • explain digital signatures • explain how digital signatures can help to solve the identity problem
Cryptography Basics • Cryptography is… • protecting privacy • authentication of identities • preservation of integrity • …in an environment of mistrust
Problem from last week • the Man-in-the-Middle attack (MITM) • intercepts the request for the bank’s public key, and sends his own public key to Alice
MITM • Alice uses the MITM’s public key to encrypt the symmetric key • the MITM can then decrypt the message and then send it to the bank • Alice needs to be able to validate that the public key belongs to the bank • asymmetric cryptography can solve this problem, but first, we need a way to check the integrity of a message
Message Integrity • in the early days of communication, parity and CRC checksums were added to messages • exercise on handout, page 1 • they help to identify errors in transmission • they do not guard against deliberate mistkaes
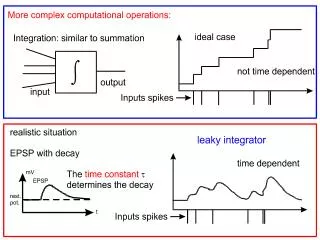
Cryptographic Hashing Key = Messagei • Message is broken in blocks the same size as the key • H0 has to be defined and published • actually a bit trickier than this • final hash Hn is the hash of the message Plaintext = Hi-1 Symmetric Encryption Hi
Hash Values • hash values are typically 128-256 bits long • there must be multiple messages that produce the same hash • for 128 bits, we only have 2128 different hash values • surely we can find two messages with the same hash???
Hash Collisions • two different messages with the same hash are called hash collisions • there must be plenty of them • tricky to find • try brute force? • for a 128 bit hash, you need to calculate the hash of 2128 different messages
Brute Force? • 2128 different messages • if you can try 1,000,000,000 messages per second, then it will take: 2128 seconds 1,000,000,000 to find a collision
Which is… • 10,782,897,524,556,318,080,696 years • so brute force doesn’t work • but there could be a shortcut if there is a problem is found with the hashing algorithm • more of this in the lab…
Signatures • two things that make a signature a signature • only one person can create the signature • everybody else can verify the signature
Digital Signatures • take a document to be signed and produce the hash for it Hash function Document Hash Document now if the document changes, we will notice, because the hash will be different obvious flaw in this scheme!
Digital Signatures • asymmetric encryption can use the private key to encrypt, instead of the public key Private key Plaintext Asymmetric Encryption Ciphertext • an example similar to this was seen in last week’s lab
Digital Signatures • if you encrypt with the private key, then you need the public key to decrypt Public key Asymmetric Decryption Plaintext Ciphertext
Digital Signatures • this means that • only the owner of the private key can encrypt (or sign) • anybody can decrypt (or verify the signature) • but what to encrypt (or sign)? • you don’t need to encrypt (sign) the entire message, only the hash of the message • The encryption of the hash value, using the private key, is called a digital signature.
Digital Signatures • take a document to be signed and produce the hash for it Hash function Hash Private key Document asymm encrypt Document Signature
Check the Signature • take the document and calculate the hash for it, compare it against the decrypted signature Public key asymm decrypt Hash function = ? Signature Document Hash Hash
Example • see page 5 of the notes
Digital Signature • a digital signature is the encryption of the hash value, using the private key • the public key is used to check the signature is correct • if the signature is correct, then the document is valid • how does this help with the MITM problem of symmetric key exchange?
Maybe the bank can sign it’s public key??? • Alice needs to check the validity of the public key, so maybe the bank should sign it’s own public key? • in order for Alice to check the bank’s signature, she needs the bank’s public key • Catch 22!
Trusty Bob • maybe we can get a third party (Trusty Bob) to sign the bank’s public key • then to check the signature of the bank’s public key, Alice needs Trusty Bob’s public key • how does Alice get Trusty Bob’s public key? • the MITM can intercept Trusty Bob’s public key if it sent over the network • back to square one…?
Are we there yet? • who do we trust to sign the bank’s public key? • who is Trusty Bob? • how do we get Trusty Bob’s public key, whilst being secure against the MITM? • next week, the final piece to the jigsaw
Summary • message integrity using hashing • key exchange is susceptible to the MITM • digital signature is the asymmetric encryption of the hash, using the private key • who do we trust to sign public keys? • how do we get their public key to check their signature?