ELECTRIC POWER GRID INTERDICTION
210 likes | 257 Views
Learn about VEGA, a tool for assessing vulnerability and defense strategies against terrorist attacks on power systems. Discover key studies on the vulnerability of U.S. grids and potential threats from terrorist groups. Explore modeling assumptions, mathematical analysis, and optimization techniques for grid protection. Delve into levels of optimization to minimize disruptions and ensure grid resilience. Suitable for utilities, analysts, and government entities.

ELECTRIC POWER GRID INTERDICTION
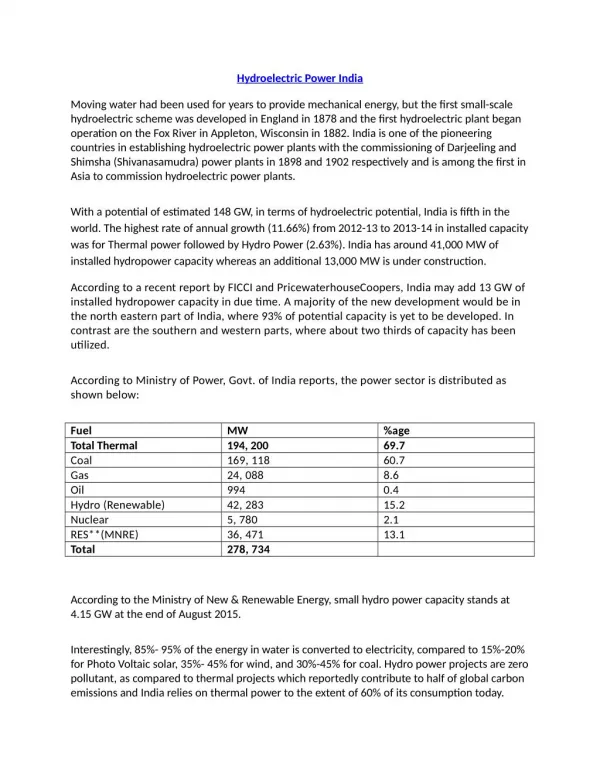
E N D
Presentation Transcript
ELECTRIC POWER GRID INTERDICTION Javier Salmeron and Kevin Wood, Naval Postgraduate School Ross Baldick, University of Texas at Austin Sponsored in part by Department of Homeland Security, Office of Domestic Preparedness
What is VEGA? VEGA is a tool for analyzing the vulnerability and defense of electric power systems under threats posed by terrorist attacks. • VEGA determines the worst possible disruption that could be caused by a terrorist attack, • Compares multiple attack plans terrorists might undertake under different resource-constrained assumptions, • Assesses security enhancement through preemptive measures, and • VEGA is based on powerful optimization techniques.
Vulnerability of Electric Power Grids: A Long-Recognized Issue • “One can hardly imagine a targetmore ideal than the U.S. domestic energy” (A.B. and L.H. Lovins, 1983) • “Any U.S. region could suffer lasting and widespread blackouts if three or more substations were targeted.” (OTA, 1990) • “The U.S. is at, or is fast approaching, a crisis stage with respect to reliability of transmission grids.” (NERC, 2001) • “The U.S. electric power systems must clearly be made more resilient to terrorist attack.” (Committee on Science and Technology for Countering Terrorism, NRC, 2002)
Terrorist Threat? • “And the threat isn't simply academic. U.S. occupation forces in Afghanistan discovered Al Qaeda documentation about the facility that controls power distribution for the eastern U.S., fueling fears that an attack on the power grid may one day become a reality.”(Energy Pulse, 2003) • (On Ahmed Ressam) “They were specifically trained to attack critical infrastructure, including electric power plants.” (CNN, 2002) • (On Colombian FARC) “They are leaving entire regions without service. We can’t post a soldier at every tower” (ISA spokesman, 2002)
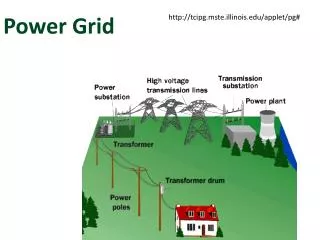
Terrorist Threat? (cont.) Potential targets: • Generating plants • Transmission and distribution lines • Substations Easy disruption + Widespread damage + Difficult recovery
Modeling Assumptions • U.S. systems are operated so that a single failure does not disrupt the system (N–1 security) • We investigate vulnerability to multiple, coordinated failures (N–m). • Our approach uses optimization theory to: • Mathematically represent a power grid and power flows • Identify worst-case attacks to the grid (most “disruptive”) • Provide insight into physical vulnerabilities, and help guide protective plans that will mitigate disruptions should attacks occur • (We maintain the assumption of information transparency)
Key Questions • What are the best • New investments (e.g., new facilities, lines, spare transformers) • Upgrades (e.g., replacing conductors) • Protective measures (e.g., hardening, surveillance...) • in • Generating systems and/or • Transmission and distribution systems • that substantially reduce system vulnerabilities? • “Best”= Improve Security + Affordable (+ Market Benefits???)
Mathematical Analysis • To defend an electric grid, first learn how to attack it! • Optimal power flow model (minimize load shedding) • Interdiction model (maximize disruption, i.e., load shedding) • Additional features of the problem are: • Time scale: Very short-, short-, medium- and long-term • Customer types; ability to “share the pain” • Uncertainty about terrorist resources • (Protective measures???)
Level 2: Interdiction model to maximize “Level-1 disruption” • Data: Power grid data and terrorist resources • Level 3: Protective model to minimize “Level-2 interdiction” • Data: Power grid data, terrorist resource and counter-terrorist resources (budget for expansion, spares, upgrades, hardening) Integrating Three Levels of Optimization • Level 1: Optimal power flow model to minimize “disruption”: • (disruption = load shedding + increased costs) • Data: Power grid data • (See mathematical details at the end of this presentation)
Slow repair Days to one week MW shedding No Repair Lines Trafos with Spares t (months) One to several days Weeks (Attack) Other Factors: System Restoration, Demand Curves...
C BUS 18 BUS 17 C BUS 21 BUS 22 BUS 23 C B G A A A BUS 19 BUS 20 B BUS 16 D 230 kV BUS 14 A A Synch. Cond. A BUS 13 BUS 15 E A B B B BUS 11 BUS 12 BUS 24 C BUS 6 BUS 3 BUS 10 BUS 9 cable BUS 4 F A MW BUS 5 BUS 8 138 kV B C A B cable BUS 7 +360h +768h BUS 1 BUS 2 t Attack +72h IEEE Reliability Test System 96-99 Total Load: 2,850 MW Salmeron, Wood and Baldick (2004), IEEE Transactions on Power Systems
VEGA VEGA: Vulnerability of Electric Power Grids Analyzer Potential Users: • Utilities, ISOs... • Government analysts
VEGA: Main Menu • File mgmt. • Grid data • Optimization • Results • One-Line GUI • Help
DC-OPF: Power Flow Model (DC Approx.) s.t. i: bus, l: line, g: generator, c: customer sector PLine, PGen: power (MW) S: power shed : bus phase
I-DC-OPF: s.t. Interdiction max-min problem I-DC-OPF: Can be converted into a standard mixed-integer model Interdiction Model
Interdictthe assets that maximize “Total Value” Interdiction Model Heuristic Solve the DC-OPFPower Flow Modelgiven the current grid configuration () Based on present and previous flow patterns, assign a “Value” (V) to each interdictable asset
The VEGA Team Javier Salmeron, NPS jsalmero@nps.edu Kevin Wood, NPS kwood@nps.edu Ross Baldick, UT Austin baldick@ece.utexas.edu