Revolutionizing Email Security: A Blueprint for Ubiquitous Internet Privacy
This document presents a comprehensive approach to enhancing email security through the implementation of open standards and personal privacy protocols. It emphasizes the necessity of user-centric, frictionless security models that require no extra effort from users. By building on legacy systems and utilizing cutting-edge cryptographic techniques, the goal is to facilitate secure communications for 2 billion users globally. The proposal invites collaboration from architects, testers, and coders to create a system that provides effortless, strong email encryption while ensuring personal privacy remains paramount.

Revolutionizing Email Security: A Blueprint for Ubiquitous Internet Privacy
E N D
Presentation Transcript
PRISM-PROOF Email Phillip Hallam-Baker Comodo Group Inc.
Goal Make Internet security ubiquitous for 2 billion users
Why the Web succeeded: • Open Standards • HTML / HTTP / URI • Build on legacy (e.g. SGML) • Open architecture • Don’t tie users to one publication model • Public domain Reference code • Please take our code and sell it • Some good technical innovations • URIs • Punt on the hard stuff (indexing, consistency)
PPE • Open Standards (or proposals) • All specifications are submitted as Internet Drafts • Build on legacy (e.g. S/MIME) • Open Architecture • Don’t tie users to one trust model • Open Source Code • Generated from the specifications • Some technical choices • Strong Email Addresses • Punt on the hard stuff
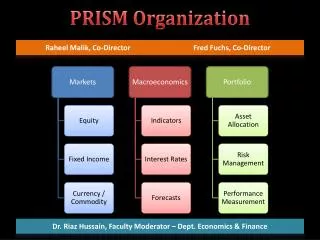
Dividing the Problem Share this Research here Trust Model Transport • Mail system integration • Distribution infrastructure
Why I am here • Recruit • Users • Testers • Coders (not just for crypto!) • Web Site (Bootstrap) • Architects • Reviewers • Evangelists
So why isn’t email secure today? Patents Limited machine capabilities The cryptowars Standards wars
Public Key Infrastructure Use Digital Signatures to authenticate keys Use Public key encryption to exchange symmetric keys Use symmetric key encryption to protect data
PEM (1993) Kings Lords Knights Serfs Peasants DSHs • Privacy Enhanced Mail • Hierarchy of Certificate Authorities
Antithesis • PGP Web of Trust • Everyone is a peer • S/MIME • Rework of PEM with multiple roots of authority
15 Year Standards Stalemate S/MIME • Deployed in 5 billion clients PGP • Monopoly of mindshare
Why has neither won? S/MIME PGP Incomprehensible to many Too much hassle to use • Too hard to get certificates • Too much hassle to use
Frictionless Security • Secure system must require no additional effort • No additional configuration • No additional steps in use • No maintenance or renewals • Except if the user wants to verify that their security is correct.
PPE 0.1 (Windows Live Mail Experience)
Configuring to receive encrypted mail • Run Key Manager, Generates • Strong email address with • Phinger • Recovery codes • Publish Phinger on Web Server • Now anyone can send you encrypted mail • And you can read it on 95% of EXISTING clients
Help Wanted! • UI experts to perform integration for • Outlook • Thunderbird • Apple Mail • iOS Mail • <Android client>
Personal PKI Master Online Monthly Encryption Per Device Authentication
Strong Email Address AD6TK2-NDKN2W-JRME7DA-RXYYHZ-T4A?alice.prism.proof@orac.hallambaker.com <phingerprint>?<account>@<domain> <phingerprint> The fingerprint of the root of Alice’s personal PKI hierarchy <account> The account to send the email to <domain> Website where the phinger is published
Phinger • Contains • Personal Public key hierarchy • Offline Master / Online / Use Keys • Policy Statements (per protocol) • Email • SMTP to example.com with STARTTLS phingerprint = X • S/MIME preferred under cert/key X. • By invitation only use cert/key Y.
[ KeyManager 1.0 ] • Publication to the Web site is automatic • Enroll certificate in key server infrastructure • Make use of Google Certificate Transparency • Register encrypted secret keys • To enable recovery if they are lost • To enable easy registration of a second device • Can tell people ‘encrypted mail is preferred’
Sending a secure email Mail Client PEEP Machine • Introducing PEEP • Privacy Enhancing Proxy
PEEP 0.1 • Looks for messages sent to a Strong Email Address • These MUST be sent encrypted • Retrieves the phinger • Encrypts the message as directed • (Currently only S/MIME could be PGP as well)
[ PEEP 1.0] • Checks every outbound address • Queries a service to see if the user prefers encrypted mail • Introduces trusted parties • Certificate Authorities • Peers
PPE 1.0 Interesting research here Key Broker Key Broker OmniPublish OmniQuery Key Manager Mail Sender
Endorsement • Current research issue • How to make it easy to endorse another person? • QR codes make strong email address transfer easy. • Please don’t laser engrave your iPhones yet
SPAM • End to End Encryption defeats (some) Spam filters • So you might not want to use end to end encryption all the time. • Instead publish the encryption key of your spam filter • Only release your end to end key to selected parties • Require messages to be signed by approved sender
Conclusion • Privacy Protected Everything provides • Secure email encryption • Security rests on well tested/reviewed standards • Frictionless security • No additional user effort at all • I need your help to make it happen. • http://prismproof.org/