DieHarder : Securing the Heap
DieHarder : Securing the Heap. Previously in DieHard … . Increase Reliability by random positioning of data Replicated Execution detects invalid memory accesses Because objects are randomly placed , buffer overflows are likely to hit unused space. Memory Management Errors.

DieHarder : Securing the Heap
E N D
Presentation Transcript
Previously in DieHard… • IncreaseReliabilitybyrandompositioningofdata • ReplicatedExecutiondetects invalid memoryaccesses • Becauseobjectsarerandomlyplaced, bufferoverflowsarelikelytohitunusedspace
Memory Management Errors • Heap overflow: • char* f = newchar[10];f[11] = 'x'; • Heap underflow: • stack<int> mystack;mystack.pop();
Memory Management Errors • Danglingpointers: • char*dp = malloc(123);free(dp);dp[10] = 'a'; • Double free: • char *foo = dp;free(dp);free(foo);
Memory Management Errors • Invalid free: • char*dp = malloc(123);free(dp[10]); • Uninitializedread: • char *foo = dp;puts(foo); • All oftheseattackscanbe (andare) exploited!
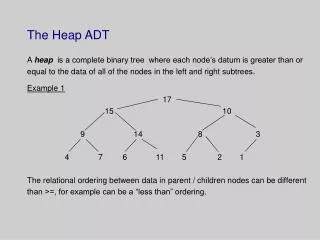
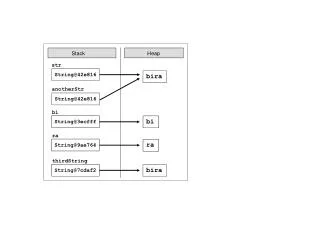
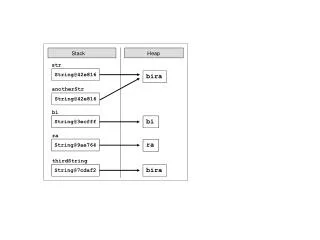
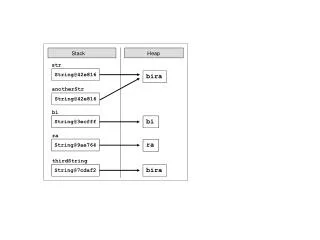
The Allocator‘s fault? • Freelist-baseallocatorsstoremetadatabetweentheobjects • Attackerscan not onlycorruptstoreddata, but also thefreelist, leadingtoarbitrarycodeexecution • Solution: BiBOP (Big Bagof Pages) Allocatorsstoremetadataseperately • SomeBiBOPsstoremetadataatthebeginningof a page, allowingittobeoverwritten (e.g. PHKmalloc)
OpenBSD‘sallocator • Based on PHKmalloc • Metadataisentirelystored in a different place • Pages arerandomlymmap‘edso thatthereareunmappedguardpages in between • Ifactivated, freedobjectsarescrambled • Objects areplacedrandomly in thepage • Reuse offreedobjectsis not predictable
Threats • First, memoryerrorshavetoexist • Toattacksystemsusingrandomizedplacement, theattackhastoberepeatable • The highertheentropy, thelongerittakestoattackspecificmemoryareas • In somecases, theattackerhasmoretriesthan in others (server vs. client)
PreviousCountermeasures • ASLR • Randomized Placement (seeOpenBSD) • Guard Pages • Canaries • W^X / DEP • Noheaders
Analysis ofDieHard • The probabilityofoverwriting a specifictargetis in O(1/N) with N beingthenumberofheapobjects • Much betterthanOpenBSD‘s 4 bitentropy • Because M timesmorespacethanneededisallocated, thereuseentropyis in O(log N) • Betterthan 5.4 in OpenBSD
ChangestoDieHard • Sparse Page Layout allocatedpages all overthepossibleaddressspace • Whilethisdecreasestheallocationperformance, itmeansthattherearemoreguardpages in between • This also increasesthesizeofthepagetable • Trade-Off betweensecurityandperformance
ChangestoDieHard • Byrandomizingreuseandoverwritingdeletedobjects, theattackercannotusethisinformationforhisattacks
Windows 7: Fault-Tolerant Heap • The ideahasbeenusedtobuildthe FTH in Windows 7 • Becauseoftheperformanceimplications, FTH isonlyactivatedforcrashingprograms (bydefault, 3 crashes in 60 minutes) • Thislimitstherepeatabilityofattacksdrasticallyandcanhelptoidentifyand fix problems