Model Checking of Software
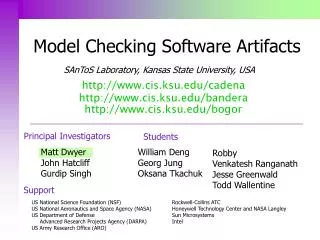
Model Checking of Software. Mooly Sagiv (Contributions from Orna Grumberg and Eran Yahav). What is model checking?. c-000157-mp-000001.jpg. Yes. What is software model checking?. Program. Property. Model Checker. No/Erroneous Input. Yes. P0: while (1) do { wait(turn==0);

Model Checking of Software
E N D
Presentation Transcript
Model Checking of Software Mooly Sagiv (Contributions from Orna Grumberg and Eran Yahav)
What is model checking? c-000157-mp-000001.jpg
Yes What is software model checking? Program Property Model Checker No/Erroneous Input
Yes P0: while (1) do { wait(turn==0); CR0; turn =1; } P1: while (1) do { wait(turn==1); CR1; turn =0; } Mutual exclusion Model Checker
typedef struct element { int value; struct element next; } Elements void main() { Elements y; … search(7, y); bool search( int value, Elements head) { Elements elem = head;while ( head != NULL ) { if (elem val == value) return TRUE; elem = elem next; } return FALSE; } No null dereferences NO head,y elem 1 2 3 NULL MC
Specification Challenge • How does one specify what the application software is supposed to do? • Different correctness notions • Can be very difficult and impossible on a real application • Software is constantly modified
Toward Realistic Specification • Partial • Only addresses certain aspects • Can be wrong • Different formalisms • Executable • Declarative • First order logic • Temporal logic • Some mechanisms for modularity
Model Checking Challenges It is not decidable even to check properties such as absence of NULL dereferences
Coping with Undecidablity(Classical Theorem Proving Approach) • Allow user interaction • Specify loop invariants • The model checker need not terminate on all programs • Manually write proofs of certain parts
Coping with Undecidablity(Classical MC Approach) • Extract a finite state machine that conservatively describes program behavior (model) • Specify the property using a formula in propositional temporal logic • Automatically check that the model satisfy the formula • Refine the model when spurious counter examples occur
Model temporal propotional formula Model Checker No/Erroneous Input Yes Classical MC Approach High level specification Program Front-End
l0,l1 turn=0 l0,l1 turn=1 NC0,l1 turn=0 l0,NC1 turn=1 l0,NC1 turn=0 NC0,l1 turn=1 CR0,l1 turn=0 l0,CR1 turn=1 NC0, NC1 turn=0 NC0, NC1 turn=1 CR0,NC1 turn=0 NC0,CR1 turn=1 l0: while (1) do { NC0: wait(turn==0); CR0: turn =1; } l1: while (1) do { NC1:wait(turn==1); CR1: turn =0; } Mutual exclusion (pc0=CR0 pc1=CR1) Front-End
l0,l1 turn=0 l0,l1 turn=1 NC0,l1 turn=0 l0,NC1 turn=1 l0,NC1 turn=0 NC0,l1 turn=1 CR0,l1 turn=0 l0,CR1 turn=1 NC0, NC1 turn=0 NC0, NC1 turn=1 CR0,NC1 turn=0 NC0,CR1 turn=1 l0: while (1) do { NC0: wait(turn==0); CR0: turn =1; } l1: while (1) do { NC1:wait(turn==1); CR1: turn =0; } Accessibility pc0=CR0 pc1=CR1 Front-End
No null dereferences typedef struct element { int value; struct element next; } Elements void main() { Elements y; … l1: search(7, y); bool search( int value, Elements head) { l2: Elements elem = head; l3: while ( head != NULL ) { l4: if (elem val == value) l5: return TRUE; l6: elem = elem next; } l7: return FALSE; } (pc=l4 pc=l6 elem l3 e=,h l3 e,h l4 e,h l6 e,h l5 e,h l7 e=,h= l3 e=,h=
Coping with Undecidablity(Abstract Interpretation) • Define operational semantics of the program • Safety properties can be defined a program condition • Liveness properties require trace semantics • Collecting semantics define the set of states • Abstract states conservatively represent many concrete states • Use an abstract interpretation algorithm to provide a sound solution • Finite number of explored abstract states
How to give a presentation • What to say and how to say it • Getting through the audience • Visual aids
What to say and how to say it • Communicate the Key Ideas • Don’t get bogged down in Details • The best talk make you read the paper • Structure your talk • Use Top-Down approach • Introduction • Body • [Technicalities] • The Conclusion Use Examples
Introduction • Define the problem • Motivate the audience • Introduce terminology • Discuss earlier work • Emphasize the contributions • [Provide a road map] Use Examples
The body • Abstract the major results • Explain the significance of the results • Explain the main techniques • Use enlightening examples • Demonstrations are welcome
[Technicalities] • Expert only part • Show something really interesting beyond the paper/tool
The Conclusion • Hindsight is clearer than Foresight • Give open problems/further work • Indicate that your talk is over
Know your audience • Background
Getting through the Audience • Use Repetitions • Remind, don’t assume • Don’t over-run • Maintain Eye Contact • Control your voice • Control your motion • Take care of your appearance
Visual Aids • PowerPoint transparencies • Don’t overload transparencies • Don’t use too many transparencies • Use Overlays Properly • Use Color Effectively • Use Pictures and Tables • The blackboard can be used too
The input of the program can be arbitrary. Let x be a prime number, i.e., all the numbers z<x do not divide x. y be the next prime number, i.e., etc. Arbitrary input Prime number x The next prime y Don’t overload transparencies
Use overlays (im)properly • Item 1 • Item 1.1 • Item 1.2 • Item 2 • Item 2.1 • Item 2.1.1
Use colors properly • Item 1 • Item 2 • Item 3
Model Checking, Abstractionsand Reductions Orna Grumberg Computer Science Department Technion Haifa, Israel
Program verification Given a program and a specification, does the program satisfy the specification? Not decidable! We restrict the problem to a decidable one: • Finite-state reactive systems • Propositional temporal logics
Model Checking An efficient procedure that receives • Description of a finite-state system (model) • Property written as a formula of propositional temporal logic It returns yes, if the system has the property It returns no+counterexample, otherwise
Finite state systems • hardware designs • Communication protocols • High level description of non finite state systems
Properties in temporal logic • mutual exclusion: always ( cs1 cs2) • non starvation: always(request eventuallygrant) • communication protocols: ( get-message) until send-message
Model of a systemKripke structure / transition system a,b a a b,c b a,c a,b c
Model of systems • M=<S, I, R, L> • S - Set of states. • I S - Initial states. • R S x S - Total transition relation. • L: S 2AP - Labeling function. • AP – Set of atomic propositions
=s0s1s2... is apath in M from siff s =s0 and for every i0: (si,si+1)R
Propositional temporal logic In Negation Normal Form AP– a set of atomic propositions Temporal operators: Gp Fp Xp pUq Path quantifiers:A for all path E there exists a path
Computation Tree Logic(CTL) CTL operator: path quantifier + temporal operator Literals:p , p for pAP Boolean operators: f g , f g Universal formulas: AX f, A(f U g), AG f , AF f Existential formulas: EX f, E(f U g), EG f , EF f
Semantics for CTL • For pAP: s |= p p L(s)s |= p p L(s) • s |= fgs |= fand s |= g • s |= fg s |= fors |= g • s |= EXf =s0s1... from s:s1 |= f • s |= E(f Ug) =s0s1... from s j0 [sj |= gand i : 0 i j [si |= f] ] • s |= EGf=s0s1... from s i 0: si |= f
Linear Temporal logic (LTL) Formulas are of the form Af, where f can include any nesting of temporal operators but no path quantifiers
CTL* Includes LTL and CTL and more ACTL*, ACTL (LTL) Universal fragments of CTL*, CTL ECTL*, ECTL Existential fragment of CTL*, CTL
Example formulas CTL formulas: • mutual exclusion: AG ( cs1 cs2) • non starvation: AG(request AF grant) • “sanity” check: EF request LTL formulas: • fairness: A(GFenabled GF executed) • A(x=a y=bXXXXz=a+b)
Property types (cont.) Combination of universal safety and existential liveness: “along every possible execution, in every statethere is a possible continuation that will eventuallyreach a reset state” AGEFreset
Model Checking M |= f[Clarke, Emerson, Sistla 83] • The Model Checking algorithm works iterativelyon subformulas of f, from simplersubformulas to more complex ones • When checking subformula g of f we assume that all subformulas of g have already been checked • For subformula g, the algorithm returns the set ofstates that satisfy g ( Sg) • The algorithm has time complexity: O( |M| |f| )
Model checking f =EF g Given a model M= < S, I, R, L > and Sg the sets of states satisfying g in M procedureCheckEF(Sg ) Q := emptyset; Q’ := Sg ; while Q Q’ do Q := Q’; Q’ := Q { s | s' [ R(s,s’) Q(s’) ] } end while Sf := Q ;return(Sf)
f f g f g f f g f Example: f =EF g f
Model checking f =EG g CheckEGgetsM= < S, I, R, L >and Sg and returnsSf procedureCheckEG(Sg) Q := S ; Q’ := Sg ; while Q Q’ do Q := Q’; Q’ := Q { s | s' [ R(s,s’) Q(s’) ] } end while Sf := Q ; return(Sf)
g g g g g g Example:f =EG g
Symbolic model checking[Burch, Clarke, McMillan, Dill 1990] If the model is given explicitly (e.g. by adjacent matrix) then only systems with about ten Boolean variables (~1000 states) can be handled Symbolic model checking uses Binary Decision Diagrams ( BDDs ) to represent the model and sets of states. It can handle systems with hundredsof Boolean variables.
Binary decision diagrams (BDDs) [Bryant 86] • Data structure for representing Boolean functions • Often concise in memory • Canonical representation • Boolean operations on BDDs can be done in polynomial time in the BDD size