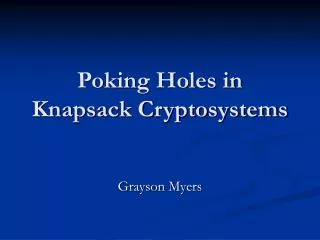
Knapsack Cryptosystems: Historical Background to Modern Security Concerns
420 likes | 504 Views
Delve into the evolution of knapsack cryptosystems, their vulnerabilities, and compare Merkle-Hellman with RSA for robust encryption strategies. Explore attacks, parameters, and security implications, shedding light on the intricate world of cryptographic protocols.

Knapsack Cryptosystems: Historical Background to Modern Security Concerns
E N D
Presentation Transcript
Knapsack Cryptosystems Dinara Barshevich JASS’05 St. Petersburg Knapsack Cryptosystems
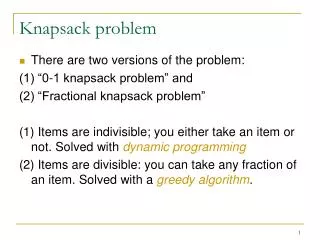
Brief historical background • 1976, Diffie & Hellman – Public Key Cryptosystem • 1977 RSA – the first incarnation of such system • 1978 Merkle – Hellman Cryptosystem • 1980s years: attacks to MH Knapsack Cryptosystems
Agenda • Idea of Public-Key Cryptosystems • Knapsack problem: setting, comlexity and basic analyses • Knapsack Public-Key Cryptosystems • Algorithm of Merkle – Hellman • Attacks to Merkle – Hellman Cryptosystem • What next? Knapsack Cryptosystems
Public key cryptosystems M - plaintext Receiver Encryption: sender Key generation E(M, K1) = C - cyphertext C - ciphertext Public key - K1 Private key - K2 Decryption: receiver D(C, K2) = M - original M - plaintext Knapsack Cryptosystems
The Knapsack problem – closely related to subset-sum problem. Knapsack Cryptosystems
Some observations on Knapsack • The general knapsack problem is known to be NP-complete • Efficient algorithm of the feasibility form of the problem helps to find such a solution easily. • Assuming that {ai } are not too large, the trivial algorithm for solving knapsack needs O(2ⁿ) steps Knapsack Cryptosystems
A better algorithm for Knapsack • Compute: • Sort them, and scan for a common member: • using O(n2^(n/2)) time+ O(2^(n/2)) storage space. • It’s the fastest algorithm! Knapsack Cryptosystems
Easy-solvable knapsacks: Knapsack Cryptosystems
Knapsacks with super-increasing sequence • A sequence {ai} is called a super-increasing sequence if • O(n) - algorithm for Knapsack with super-increasing weights: for j = n downto 1 { If s ai then { xi = 1; s = s - ai; } else xi = 0; } return (x1, x2,..., xn). • Solution if exists is unique! Knapsack Cryptosystems
Basic idea: Public key Private {A1,.An} {B1,.,Bn} Alice Alice Bob Public Private Bob:encoding Alice:decoding Alice X1,..Xn C=∑BiXi X1,..Xn S=∑AiXi Charlie Hard knapsack Easy knapsack Knapsack Cryptosystems
MH system: key generation • Start with a super-increasing knapsack {b1,…, bn} such that: • Choose M and W such that: Knapsack Cryptosystems
MH system (cont.) • Compute Knapsack Cryptosystems
MH system: encryption Knapsack Cryptosystems
MH system: decryption The {b1,…, bn} are super-increasing Easy to solve Knapsack Cryptosystems
Two variants of Merkle-Hellman cryptosystem • singly-iterated Merkle-Hellman cryptosystem • multiply-iterated Merkle-Hellman cryptosystem Knapsack Cryptosystems
Multiply-iterated MH cryptosystem Knapsack Cryptosystems
MH vs. RSA • MH is about 100 times faster than RSA (MH: n ~ 100, RSA: m ~ 500bits) • MH : n bits are encoded in 2n bits, RSA: n bits are encoded in n bits • MH’s public key is of size 2n² ~ 20,000 for n ~ 100 and RSA’s is 2m ~ 1000 for m ~ 500bits • MH assumes P <> NP, while RSA assumes factorization is in NP (<> P) Knapsack Cryptosystems
Security of MH cryptosystem:general doubts. • What if P = NP? • What if most instances of knapsack used by MH are easy to solve? • What if one can deduce from the public Knapsack what the construction method is? Knapsack Cryptosystems
Security of MH cryptosystem:special doubts. • Result of Brassard: if breaking a cryptosystem is NP-hard, then NP = Co-NP. • If NP <> Co-NP, then breaking the MH cannot be NP-hard! • Linearity of MH equation: e.g. provides a single bit of information about plaintext (as we may assume:not all the ai are even) Knapsack Cryptosystems
Parameters choice • If some bj is large we get inefficient knapsack • If, say, b1 = 1 then aj = W for some j • One can try all aj as a candidate for W Knapsack Cryptosystems
Parameters choice – cont’d Knapsack Cryptosystems
Attacks on MH Cryptosystem • modular multiplication does not disguise enough the easy knapsack using Private Key Attack method B1,…Bn Easy C1,…Cn Easy A1,…An General Charlie Alice Knapsack Cryptosystems
Attacks on MH Cryptosystem • try to solve the general knapsack problem, when the ai are large enough using Private Key A1,…An General but large enough B1,…Bn Easy Alice Knapsack Cryptosystems
Attacks on MH knapsack cryptosystem • Rely on the fact that the modular multiplication does not disguise enough the easy knapsack: 1. Shamir’s polynomial algorithm for the singly-iterated Merkle-Hellman, 1982 2. Brickell’s attack on the multiply-iterated Merkle-Hellman, 1985 Knapsack Cryptosystems
Shamir’s attack on basic MH system Knapsack Cryptosystems
This means that all of the kj /aj are close to U/M • In MH: b1,…, bq~ 2ⁿ: q – small enough • Let • We obtain • Subtracting i=1 term: • That implies: Knapsack Cryptosystems
kji aj1 is on the order of 2^4n, then the kj,and aj should be of very special structure • In most cases the kji ,1≤ i ≤ q are determined uniquely by this equation • invoking H. W. Lenstra’s theorem: the integer programming problem in a fixed number of variables can be solved in polynomial time! • This yields the kji ,1≤ i ≤ q Knapsack Cryptosystems
Now we have the kji ,1≤ i ≤ q • we can construct a pair (U´, M´): U´/M´ close to U/M such that: if compute the weights cj by - form a super-increasing sequence when arranged in increasing order • The cj can be used to decrypt the message! Knapsack Cryptosystems
But how to find j1,…, jq ? • As permutation π is secret, we do not have j1,…, jq • The solution is easy: the cryptanalyst considers all possible choices of them, and still remains in polynomial time! Knapsack Cryptosystems
Difficulties of Shamir’s method • The crucial tool in the attack was Lenstra’s result on integer programming in a fixed number of variables • Lenstra’s algorithm running time is given by a high degree polynomial – never implemented! • Continued fraction can be used instead of Lenstra’s result, but when the bj are large enough, it fails Knapsack Cryptosystems
Attacks to low-density general knapsack problems • try to solve the general knapsack problem, when the ai are large enough • 2 famous attacks: - Lagarias and Odlyzko, 1983 - Brickell low-density attack, 1984 Knapsack Cryptosystems
On integer lattices • An integer lattice is an additive subgroup of Zⁿ that contains n linearly independent vectors over Rⁿ • A basis (v1 ,…, vn ) of L is a set of elements of L such that L = {z1 v1 +…+ zn vn : zi – integer} • Input: (v1 ,…, vn ) – basis of L - lattice • SVL: Find the shortest non-zero vector of L • quite hard problem – yet not proved! Knapsack Cryptosystems
Lovasz-reduced basis • Lovasz’ polynomial-time algorithm: • given a basis for a lattice, constructs Lovasz- reduced basis (v1 ,…, vn ): Knapsack Cryptosystems
The low-density attack itself • Given the ai and s, form the (n+1)-dimensional lattice with basis Knapsack Cryptosystems
And the miracle is • If {xj | j = 1..n} solve the knapsack problem, then • Since the xj are 0 or 1, this vector is very short • The basic attack: 1. run the Lovasz lattice basis reduction algorithm on the basis V 2. check if the resulting reduced basis contains a vector that is a solution or not Knapsack Cryptosystems
How it works: • If {aj} are large: most vectors in the lattice are large. So the vector X corresponding to our solution might be the shortest: • If aj ~ 2^(βn) whereβ>1.54725 then Xis the shortest in most lattices • So: if we could efficiently solve SVL – we can solve most low-density knapsacks Knapsack Cryptosystems
How we solve SVL • Proved: we can solve knapsacks with aj ~ 2^(n^2) – extremely large! In practice: much better Knapsack Cryptosystems
Summary: • MH algorithm itself • Attack using revealing an easy knapsack from public • Attack using solvability of low-density knapsacks Knapsack Cryptosystems
In conclusion: • Both of two main fears were borne out. • A few knapsack-based Cryptosystems still remain unbroken: e.g. Chor – Rivest 1988 • Since 1) high speed • 2) factorization and logarithm procedures can turn out efficiently solvable someday • 3) elegance of the algorithm search is going on… Knapsack Cryptosystems
Example - exercise • Make a private key: with n = 6 • (2, 3, 6, 13, 27,52) • M = 105, W = 31 • aj : (62, 93, 81, 88, 102, 37) Knapsack Cryptosystems
Encryption • Let Mes = 011000110101101110 • Shift it: 011000 – 93+81 = 174 • 110101 – 62+93+88+37 = 280 • 101110 – 62+81+88 +102 = 333 • Cipher = (174, 280, 333) Knapsack Cryptosystems
Decryption Knapsack Cryptosystems