Migrating to Windows Server 2003 Active Directory
600 likes | 747 Views
This guide covers essential aspects of migrating to Windows Server 2003 Active Directory, including functional levels, deployment strategies, and preparation for forests and domains. Explore performing in-place upgrades, enhancements in Active Directory, and multi-forest support. Discover detailed steps for upgrading from Windows 2000 and NT 4.0, domain restructuring, tools used for migration, and schema upgrades. Learn about the impact on domain controllers and best practices for introducing new domain controllers in a forest to ensure a seamless transition.

Migrating to Windows Server 2003 Active Directory
E N D
Presentation Transcript
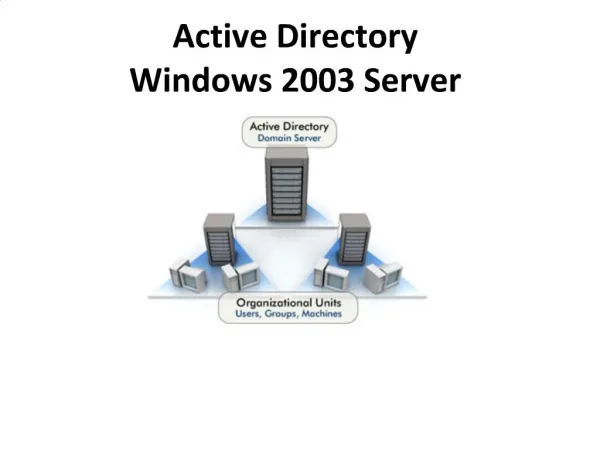
Agenda • Functional levels • General deployment strategies • Preparing the forest and domains • Performing in-place domain upgrades • Active Directory Enhancements • Active Directory Multi-Forest Support • DNS Enhancements
Domain Functionality Win NT4 Win2000 B A C mixed native Windows 2000 - mixed Windows 2000 -native Windows Server 2003 Interim Windows Server 2003 Windows Server 2003 Upgrade to Windows Server 2003 (DCPROMO) Prior to Windows Server 2003 UI (Users & Computers or Domains and Trusts) Happens automatically (when Forest version is raised during PDC upgrade)
Forest Functionality B A C Win2000 Win NT4 Win2000 Windows Server 2003 Interim Win2000 Windows Server 2003 Windows Server 2003 Recommended (choose option in DCPROMO during PDC upgrade) DCPROMO (Upgrade to Windows Server 2003) Workaround if you decide to go to level ‘1’ later (using LDP, adsiedit) UI (Domains and Trusts)
Deployment strategies • Domain restructure • In-place domain upgrade • From Windows 2000 • From NT 4.0 • - Upgraded domain is forest root • - Upgraded domain is additional domain in forest
MUD1 MUD2 RES1 RES2 RES3 Domain Restructure • “Consolidation” or “collapse” • Move security principals and DCs between domains • Allows you to design an ideal forest • Use restructuring tools • ADMT, Movetree, Clone Principal, 3rd party MUD Restructure RES1
Upgrade from Windows 2000 • Easy and seamless upgrade process • No restructuring necessary • No forest, domain, OU or replication planning necessary • No user / workstation / profile migration • Windows Server 2003 DCs fully compatible with Windows 2000 DCs • Windows Server 2003 DCs can play in Windows 2000 forest / domain in any role • - New DC (dcpromo) • - Upgrade of existing DC • Preparing forest and domains are separate step from introducing the first Windows Server 2003 DC
Windows 2000 Forest/Domain Upgrade • New features and fixes require upgrade operations • Tightens security on resources that use the Everyone group to grant access by: • Improving default security descriptors. • Changing group memberships: the Anonymous Logon group is no longer a member of the Everyone group. • Creates new objects used by individual applications. • Creates new containers that can be used to verify that the preparation was successful. • Updates the Active Directory Schema. • Previous schema modifications in your environment are not affected • Single tool (adprep) to accomplish all tasks • Run once per forest (adprep /forestprep) • Run once per domain (adprep /domainprep)
ADPREP /FORESTPREP • Schema upgrade • Needs to run on schema master • Does not cause a GC full-sync • Small number of new indexed attributes • SP3 DCs: No performance impact • Schema extension creates little replication traffic only • Display specifiers • Enables new features in UI • Creates around 100KB replication traffic
ADPREP /FORESTPREP • Adjusts ACLs to enable new features • RSOP, Everyone != Anonymous logon, PKI • Little replication traffic only • Adprep /forestprep has only small impact • Replication • Domain controller performance • No impact on Windows 2000 SP3 DCs • Small impact on pre-Windows 2000 SP3 DCs • AD database size • Creates special container when finished successfully • CN=Windows2002Update,CN=ForestUpdates,CN=Configuration, DC=<forest_root_domain>
ADPREP /DOMAINPREP • Needs to run on Infrastructure Master in each domain • Impact on Domain Controllers is hardly measurable (network traffic, DC impact) • Creates special container when finished successfully • CN=Windows2002Update,CN=DomainUpdates,CN=System, DC=<domain>
Introducing the First WS2003 Domain Controller in Forest • Once adprep has run, Windows Server 2003 Domain Controllers can join the forest • Two methods • Upgrade existing domain controller (Windows 2000 or Windows NT 4) • Install Windows Server 2003 as member server and run dcpromo • Choose any domain to hold the first Windows Server 2003 DC • Upgrade of PDC performs special operations again • Creates group for Terminal Service, internal groups • Role transfer to Windows Server 2003 DC triggers same operations • Best practice • Install Windows Server 2003 member server and promote to Domain Controller • Upgrade PDC to Windows Server 2003 early in the process • Or transfer PDC role to Windows Server 2003 DC, even if temporarily only
Features depending on Windows Server 2003 Version • More scalable KCC algorithm • Link value replication • Cross forest trust • Dynamic auxiliary classes • InetOrgPerson objectClass change • Schema delete • Domain rename
Agenda Enhancements in the areas of: • Building Domain Controllers • Active Directory versioning and functional levels • AD Replication • Global Catalog Improvements • Enhanced Administration • Active Directory Objects and Architecture • Schema deletes • Application directory partitions • Domain Controller & Domain Rename
DesignGoals • Incremental release • Build on Windows 2000 • Design fundamentals are the same • Build on existing Active Directory deployment • Impose no requirement to redesign • No specific planning considerations: continue with Windows 2000 planning/deployment • Review new security lockdown features • Scalability, management, monitoring • Improve deployment and manageability • Alleviate fear of making irreversible decisions
Windows Backup backup system state DCPROMO /ADV Store to media: DVD CDROM Tape File System Replica From Media DC Target Server Restore to an alternative location
Replication Model • Replication is at attribute level • The replication model is described as multimaster, loose consistency with convergence • Multimaster • Changes can be made at any DC • Loose consistency • There is a latency between changes being made and their availability throughout the enterprise • Convergence • Eventually the changes will propagate to all DCs and conflicts will have to be detected and resolved
Sally Members John Pete Problem: Group Replication Sally Members John G1 G1 Jane Srv2 Srv1 On Replication newer attribute wins Multivalue attributes are replicated as a single entity • One change, lots of data replicated • If the same group is simultaneously updated, after replication only one set of users will be retained
Solution: Linked-Value Replication • Store per-value replication metadata for linked multi-valued attributes • Replicate individual changes instead of whole membership • Storage and protocol incompatible with Windows 2000 - only works with Windows Server 2003 • Requires Windows Server 2003 or Windows Server 2003 Interim forest functionality • Eliminates the limit of 5000 direct group members
Problem: KCC Scalability • No issues for Intra-Site replication • Inter-Site replication topology (ISTG) can be a complex operation, similar to OSPF routing • Factors are • Number of Sites • Number of Domains • Transitiveness of Site-Links increases CPU cost of topology generation • Transitiveness is implemented as one Site-Link-Bridge that contains all Site-Links
Workaround: Windows 2000 Guidelines • Always disable transitiveness • Less than 500 sites: Use KCC • But test your hardware first • Follow guidelines in KB article Q244368 • More than 500 sites: Create connection objects manually • Branch Office deployment guide recommends manual topology for more than 100 sites
Solution: Improved ISTG • Vastly improved inter-site topology generation (ISTG) scalability • Eliminates need for manual topology • Vastly more scaleable • Current thinking is that it scales to 5,000 sites (3000 tested) • Still single threaded – uses only one CPU on SMP DCs • Generates different topology than Windows 2000 ISTG • Requires Windows Server 2003 or Interim forest functionality
Membership details in logon domain GC Builtin Domain Local Global Universal Membership details in GC Problem: Logon and GC Dependency • A user’s universal group membershipchanges by: • Adding the user to a universal group • Adding a global group of which the user is a member • Nesting appropriate global and universal groups • During the logon process the security access token is constructed Security Access Token User SID Group SIDs
Workaround #1 • A GC at every site to avoid logon failures when the network is down • Increased hardware costs • Replication overhead
Workaround #2 • Logon failed if GC not available • Administrators can still logon • Registry switch: HKLM\system\CurrentControlSet\Control \Lsa\IgnoreGCFailure • Logon with failed GC presents a possible security breach • Incomplete security token • Ignores access deny for universal groups
On first logon the users group details are cached GC Periodically updateddefault 8 hours Bellevue Solution: GC-less Logon DC London • The cached group information stored in the user’s • msDS-Cached-Membership attribute - Enabled as attribute of site object
Solution: Universal Group Caching • Domain controller caches complete group membership of an user • Cache is populated at first logon • Subsequent logons use cache • Cache is refreshed periodically • Source from nearest GC • Observe replication schedule on site link • All DCs in site perform cache refresh for users who have logged on to that site • Replicated to all other DCs in domain *
Design Implications of Universal Group Caching • Design benefit • GCs not needed permanently for logon • GC placement only driven by applications now • Reduces replication overhead for GCs in many deployments • Still good reasons to widely distribute GC servers (e.g. Exchange 2000)
Problem: GC Full Sync • Adding attributes to the GC partial attribute set causes all GCs to full sync • Equivalent to repromoting all GCs • No interruption in service • Bandwidth, CPU intensive • Applications may add attributes to the GC partial attribute set that trigger a mass replication • Exchange 2000
Solution: No GC Full Sync • Replicate only added attributes • Modification to replication protocol • Works in Windows 2000-mode domain / forest* • Works between Windows Server 2003 DCs only • If Windows Server 2003 DC cannot find Windows Server 2003 partner, it will full sync • Design benefit • Schema extensions that change GC PAS can now be deployed without GC full sync • Implication on deployment of Windows Server 2003 DCs in a Windows 2000 AD
AD as an Application Directory • Inappropriate to store volatile data • Only three choices of replication scope • Not replicated • Domain-wide (domain NC) • Forest-wide (configuration NC) • Data may go to places where not used • But the DS is a rich data store! • Powerful query, extensible schema, rich access control, and more
Application Directory Partitions • Provides the ability to create new naming contexts within the directory • The DCs that host the replicas of the NC can be controlled • Cross-domain replication is supported • With the exception of security principals any type of object/attribute can be supported • Will typically be created directly by applications
Domain Controller = Application Partitions • Domain1 Data • DNS Data • IP Telephony Data • Domain2 Data • IP Telephony Data Domain1 • Create on/replicate to any DC in a forest (can cross domain boundaries) • As few/many replicas as you want • Not replicated to GC • Observes existing forest site topology, replication schedule • Can contain any object type except security principals • Named/located via DNS (e.g., MyApp.xyz.com) Domain2 Forest • Domain1 Data • DNS Data • Domain2 Data • DNS Data • Domain1 Data
Forest Trust Scenarios Reasons for using forest trust • High security demands / not trusting all domain admin in forest / all DC in forest not physically secured. • Different AD schema requirements. • Isolation of DMZ. • Outsourcing IT operations (Operator creates separate forests and administrates using same credentials.) • Creating separate Application forest(s). • Sharing information with other organizations partners, customers, suppliers…
External Trust • Required for AD-NT4, AD-AD (inter-forest) and AD-AD (intra-forest shortcut trust) • Non Transitive – direct trust to each trusted domain required. • External trust is NT 4.0 style trust. Require NetBIOS name resolution (WINS or LMHOSTS file). • Kerberos fails over external trust • Only NTLM authentication and authorization possible over external trust. • No support for UPN logons
External Trust Management Forest A Forest B Forest C
NTLM only Kerberos Limits to W2K Multi-Forest Support: Kerberos Authentication Forest B Forest A External Trust Multi-tier Application User’s PC File Server
Logon as Alice@ForestA Limits to W2K Multi-Forest Support: UPN Logon Forest B Forest A External Trust Kerberos Fails NTLM Fails Alice’s DC
Forest Trust Overview • One way or two way Kerberos trust. • Established between forest root domains. • Transitive – between all domains in two forests. • Forest trust is NOT transitive between forests. • Kerberos trust – NTLM supported over trust. Trust A-B Trust B-C A B C Forest A Forest B Forest A does NOT trust forest C
Forest Trust Explained • Allows you to authenticate using account in trusted forest. • Allows Kerberos and NTLM authentication • Allows assigning rights to users, machines and groups in trusted forest. • Allow UPN logon using credential from any trusted domain. (Logon using NetBIOS domain name only possible between forest root domains.)
What Forest Trust NOT provide • For security, privacy and performance reasons it is NOT possible to perform LDAP browsing of trusted forests. (LDAP search is however possible – as long as you know the name of security principal you wish to add from the trusted forest.) • It is NOT possible to logon, using credentials from trusted domain, if client does not support UPN logon (except between the forest domain roots.) • Kerberos delegation is NOT supported over forest trusts.
Cross-forest Authentication • Network logon • Both Kerberos & NTLM are enabled • Interactive logon • Smartcard logon for Kerberos • Logon with UPN • Both Kerberos & NTLM are enabled • Type full UPN (no domain selection / dropdown or NT4 style names)