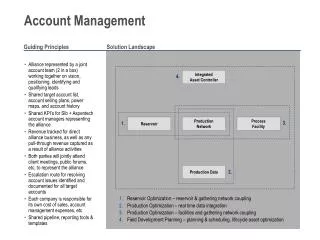
Account Management
Account Management. W.lilakiatsakun. The Purposes of Accounting (1). The focus of accounting is to track the usage of network resources and traffic characteristic Various accounting scenarios Network Monitoring User Monitoring and profiling Application monitoring and profiling

Account Management
E N D
Presentation Transcript
Account Management W.lilakiatsakun
The Purposes of Accounting (1) • The focus of accounting is to track the usage of network resources and traffic characteristic • Various accounting scenarios • Network Monitoring • User Monitoring and profiling • Application monitoring and profiling • Capacity planning
The Purposes of Accounting (2) • Traffic profiling and engineering • Billing • Security analysis • And etc
Network Monitoring (1) • A network monitoring solution can provide the following details for performance monitoring • Device performance monitoring • Network Performance monitoring • Service performance monitoring
Network Monitoring (2) • Device performance monitoring • Interface and subinterface utilization • Per Class of service utilization • Traffic per application • Network Performance Monitoring • Communication patterns in the network • Path utilization between devices in the network • Service Performance Monitoring • Traffic per server • Traffic per service • Traffic per application
User Monitoring and Profiling • Monitor and profile users • Track network usage per user • Document usage trends by user, group and department • Identify opportunities to sell additional value-added services to targeted customer • Build a traffic matrix per subdivision, group or even user • A Traffic matrix illustrates the patterns between the origin and destination of traffic in the network *Technology for user monitoring and profiling • RMON, AAA ,Netflow
Application Monitoring and Profiling (1) • Monitoring and profile application • In the entire network • Over specific expense link • Monitoring application usage per group or individual user • Deploy QoS and assign applications to different classes of service • Assemble a traffic matrix based on application usage *a collection of application specific detail is very useful for network baselining *
Application Monitoring and Profiling (2) • Application categories • Identified by TCP/UDP port number – well known (0-1023) , registered port number (1024-49151) (all assigned by IANA) • Identified by dynamic / private application port number (49152 -65535) • Identified via type of service (ToS) bit – voice and video conferencing (IPVC)
Application Monitoring and Profiling (3) • Based on the combination of packet inspection and multiple application-specific attributes • RTP – based on attributes in the RTP header • Subport Classification • HTTP: URLs, MIME types or hostnames • Citrix applications: traffic based on published application name * *Technology for Application monitoring and profiling • RMON2, NBAR ,Netflow
Capacity Planning (1) • Link Capacity Planning • MIB in the interface group • Network-wide Capacity Planning • The capacity planning can be done by mapping the core traffic matrix to the topology information • The core traffic matrix is a table that provides the traffic volumes between the origin and destination in a network
Traffic Profiling and Engineering(1) • Analyzing core traffic matrix per Class of Service (CoS) • CoS1 VoIP traffic • CoS2 Business critical traffic • CoS3 Best effort Traffic • What if analysis • Failure condition
Billing (1) • Data Collection – measuring the usage data at the device level • Data Aggregation – combining multiple records into a single one • Data mediation – converting proprietary records into a well known or standard format • De-duplication – eliminate duplicate records • Assigning usernames to IP addresses – performing a DNS and DHCP lookup and getting additional accounting records from AAA servers
Billing (2) • Calculating call duration – combining the data records from devices with RADIUS session information and converting sysUptime entries to time of day and date of month related to the user’s time zone • Charging – charging policies define tariffs and parameters to be applied • Invoicing – Translating charging information into monetary units and printing a final invoice for the customer
Billing (4) • Billing models can be the followings • Volume-based billing • Destination-Sensitive Billing (distance from source) • Destination and Source –Sensitive Billing • Quality of Service Billing (DiffServ Network) • Application and Content-Based Billing • Time/Connection-Based Billing • VoIP/IP Telephony Billing
Security Analysis (1) • Here ‘s a list of possible checks to detect a security attack • Suddenly highly increased overall traffic in the network • Unexpectedly large amount of traffic generated by individual hosts • Increased number of accounting recorded generated • Multiple accounting records with abnormal content (TCP SYN flood) • A changed mix of traffic applications such as increase in unknown application
Security Analysis (2) • A significantly modified mix of unicast multicast and broadcast traffic • An increasing number of ACL violation • A combination of large and small packets could mean a composed attack • The big packets block the network links • The small packets are targeted at the network component and servers
Authentication Authorization Accounting (AAA) W.lilakiatsakun
Authentication (1/3) • Authenticationis the act of establishing or confirming something (or someone) as authentic, that is, that claims made by or about the thing are true. • Commonly one entity is a client (a user, a client computer, etc.) and the other entity is a server (computer).
Authentication (2/3) • Authentication is accomplished via the presentation of an identity and its corresponding credentials. • Examples of types of credentials are passwords, , digital certificates, and phone numbers (calling/called).
Authentication (3/3) • One familiar use of authentication and authorization is access control. • Common examples of access control involving authentication include: • Withdrawing cash from an ATM. • Logging in to a computer • Using an Internet banking system. • Entering a country with a passport
Authorization (1/4) • Authorization is a process to protect resources to be used by consumers that have been granted authority to use them. • Resources include individual files, data, computer programs, computer devices and functionality provided by computer applications.
Authorization (2/4) • Examples of consumers are computer users, computer programs and other devices on the computer. • Authorization (deciding whether to grant access) is a separate concept to authentication (verifying identity), and usually dependent on it.
Authorization (3/4) • Authorization may be based on restrictions • time-of-day restrictions • physical location restrictions, • restrictions against multiple logins by the same user. • Most of the time the granting of a privilege constitutes the ability to use a certain type of service.
Authorization (4/4) • Examples of types of service • IP address filtering • QoS/differential services, bandwidth control/traffic management • compulsory tunneling to a specific endpoint, and encryption.
Accounting (1/2) • Accounting refers to the tracking of the consumption of network resources by users • It used for management, planning, billing, or other purposes. • Real-time accounting refers to accounting information that is delivered concurrently with the consumption of the resources. • Batch accounting refers to accounting information that is saved until it is delivered at a later time.
Accounting (2/2) • Typical information that is gathered in accounting may be: • the identity of the user, • the nature of the service delivered, • when the service began, and when it ended.
RADIUS (1/2) • Remote Authentication Dial In User Service (RADIUS) is a networking protocol that provides centralized access, authorization and accounting management for people or computers to connect and use a network service. • When a person or device connects to a network often times "Authentication" is required. • Networks or services not requiring authentication are said to be anonymous or open.
RADIUS (2/2) • Once authenticated Radius also determines what rights or privileges the person or computer is "Authorized" to perform and makes a record of this access in the "Accounting" feature of the server. • It is often used by ISP's, Wireless Networks, integrated e-mail services, Access Points, Network Ports, Web Servers or any provider needing a well supported AAA server.
RADIUS : Authentication and Authorization (1/8) • Authentication & Authorization are described in RFC 2865 • The user or machine sends a request to a Network Access Server (NAS) to gain access to a particular network resource using access credentials.
RADIUS : Authentication and Authorization (2/8) • The credentials are passed to the NAS device via the link-layer protocol - for example, Point-to-Point Protocol (PPP) in the case of many dialup or DSL providers • In turn, the NAS sends a RADIUS Access Request message to the RADIUS server, requesting authorization to grant access via the RADIUS protocol.
RADIUS : Authentication and Authorization (3/8) • This request includes access credentials, typically in the form of username and password or security certificate provided by the user. • Additionally, the request contains information which the NAS knows about the user, such as its network address or phone number
RADIUS : Authentication and Authorization (4/8) RADIUS Configuration
RADIUS : Authentication and Authorization (5/8) • The RADIUS server checks that the information is correct using authentication schemes like PAP, CHAP or EAP. • The user's proof of identification is verified, along with, optionally, other information related to the request, such as the user's network address or phone number, account status and specific network service access privileges.
RADIUS : Authentication and Authorization (6/8) • Historically, RADIUS servers checked the user's information against a locally stored flat file database. • Modern RADIUS servers can do this, or can refer to external sources - commonly SQL, Kerberos, LDAP, or Active Directory servers - to verify the user's credentials.
RADIUS : Authentication and Authorization (7/8) • The RADIUS server then returns one of three responses to the NAS; a "Nay" (Access Reject), "Challenge" (Access Challenge) or "Yea" (Access Accept). • Access Reject - The user is unconditionally denied access to all requested network resources. • Reasons may include failure to provide proof of identification or an unknown or inactive user account.
RADIUS : Authentication and Authorization (8/8) • Access Challenge - Requests additional information from the user such as a secondary password, PIN, token or card. • Access Challenge is also used in more complex authentication dialogs where a secure tunnel is established between the user machine and the Radius Server in a way that the access credentials are hidden from the NAS. • Access Accept - The user is granted access. • Once the user is authenticated, the RADIUS server will often check that the user is authorized to use the network service requested.
RADIUS : Accounting (1/3) • Accounting is described in RFC2866 • The primary purpose of this data is that the user can be billed accordingly; the data is also commonly used for statistical purposes and for general network monitoring • When network access is granted to the user by the NAS, an Accounting Start request is sent by the NAS to the RADIUS server to signal the start of the user's network access.
RADIUS : Accounting (2/3) • "Start" records typically contain the user's identification, network address, point of attachment and a unique session identifier • Periodically, Interim Accounting records may be sent by the NAS to the RADIUS server, to update it on the status of an active session. • "Interim" records typically convey the current session duration and information on current data usage.
RADIUS : Accounting(3/3) • Finally, when the user's network access is closed, the NAS issues a final Accounting Stop record to the RADIUS server, providing information on the final usage in terms of time, packets transferred, data transferred, reason for disconnect and other information related to the user's network access.
RADIUS Properties (1/4) • The RADIUS protocol does not transmit passwords in cleartext between the NAS and RADIUS server (not even with PAP protocol). • Rather, a shared secret is used along with the MD5 hashing algorithm to obfuscate passwords. • Because MD5 is not considered to be a very strong protection of the user's credentials, additional protection - such as IPsec tunnels - should be used to further encrypt the RADIUS traffic.
RADIUS Properties (2/4) • RADIUS is a common authentication protocol utilized by the IEEE 802.1X security standard (often used in wireless networks). • Although RADIUS was not initially intended to be a wireless security authentication method, it improves the WEP encryption key standard, in conjunction with other security methods such as EAP-PEAP.
RADIUS Properties(3/4) • RADIUS has been officially assigned UDP ports 1812 for RADIUS Authentication and 1813 for RADIUS Accounting by the Internet Assigned Number Authority (IANA) • However before IANA allocation, ports 1645 - Authentication and 1646 - Accounting were used unofficially and became the default ports assigned by many RADIUS Client/Server implementations of the time.
RADIUS Properties(4/4) • The tradition of using 1645 and 1646 for backwards compatibility continues to this day. • For this reason many RADIUS Server implementations monitor both sets of UDP ports for RADIUS requests. • Microsoft RADIUS servers default to 1812 and 1813 • Cisco devices default to the traditional 1645 and 1646 ports. • Juniper Networks' RADIUS servers also defaults to 1645 and 1646.