Memory Management
Memory Management. A memory manager should take care of allocating memory when needed by programs release memory that is no longer used to the heap. Memory management also deals with

Memory Management
E N D
Presentation Transcript
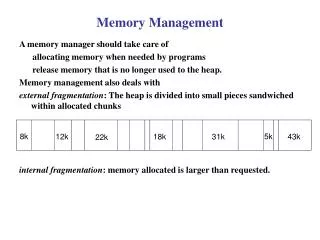
Memory Management A memory manager should take care of allocating memory when needed by programs release memory that is no longer used to the heap. Memory management also deals with external fragmentation: The heap is divided into small pieces sandwiched within allocated chunks internal fragmentation: memory allocated is larger than requested. 8k 5k 12k 18k 31k 43k 22k
Memory Management green areas are allocated memory Suppose that we have a request for 12KB and the manager allocated 16K for that request Because of internal fragmentation, 4K are wasted 32k 8k 32k 16k 4k wasted 12k is actually used
Memory Management Basics The memory manager should support the following two operations: acquire() and release(). Acquire: which locates a region of contiguous, unused memory locations of a specified size and returns a pointer to that region. The region is marked reserved. Release: which returns a region of reserved memory locations to the heap.
Free List Implementation: Singly Linked Lists A data structure plus implementation of acquire() and release() operations over this data structure is needed. Chosen implementation should consider speed (of memory allocation and deallocation) as the most important metric. One implementation of free list is based on Linked Lists. length length length length next next next next . . . : : : : : : : :
Implementation with Singly Linked List (cont'd) The acquire() method is called when memory is requested. It takes as a parameter the size of the requested memory It returns a reference to the allocated memory . The acquire() method should search the free list for a free area. IF an area of larger size than the requested was found, split into two areas, allocate one and insert back the other. There could be many nodes in the free list that satisfy the request. The one to be chosen depends on the searching policy.
Implementation with Singly Linked List (cont'd) Example. A request is received: p= aquire(20); Assume that we use first-fit sequential search. 10 30 20 8 5
Implementation with Singly Linked List (cont'd) release() operation The release() operation returns reclaimed memory to heap. In addition to freeing memory, release() also combines free memory areas with contiguous addresses to generate larger areas. Memory areas in the free list should be kept sorted by address so that they we can combine adjacent memory areas.
Implementation with Singly Linked List (cont'd) Example. Release() method: Suppose that the same memory area we allocated in the previous slide is released now. Note that our linked list should be sorted according to the starting address of the free blocks, this is the only way to allow adjacent nodes to be combined. 10 25 30 20 8
Implementation with Singly Linked List (cont'd) The singly-linked free list should be kept sorted The running time of the release() operation is O(n) in the worst case, where n is the number of nodes in the list. One problem with singly-linked free list is that, given a pointer to an area, we cannot extract that area from the free list without traversing the list because in order to extract an element from a linked list, we need to know the predecessor of that element.
Implementation using Doubly Linked List To overcome the problems of singly linked list implementation we can use doubly linked list length length length length next next next next . . . . . prev prev prev prev status status status status : : : : head
Implementation: Doubly Linked List (cont'd) Release()To release a free area, we just insert the free area node at the head of the free list length length length length next next next next . . . . . prev prev prev prev status status status status : : : : head
Implementation: Doubly Linked List (cont'd) The acquire() method must traverse the free list using any sequential allocation strategy ( first-fit/best-fit/worst fit/next-fit). While acquire() is searching for a memory area, the adjacent memory areas are combined. When an area (node) is visited, the area that immediately follows that area is examined. If free it should be combined with the area corresponding to the visited node.
Implementation: Doubly Linked List (cont'd) We can know if the adjacent memory area is free by checking the status field. If the adjacent area is free, we combine the sizes of the two areas into an area of the size equal the sum of the sizes of the two areas and we extract the other node Keep combining adjacent nodes until you reach a reserved node.
Implementation: Doubly Linked List (cont'd) } Length = 15 Suppose that we want to allocate 15KB using the first fit strategy. next prev Status = reserved } Length = 20 next prev Status = free .. ..... … Length next prev Status = reserve head
Comparing the Two Implementations Both of them use acquire() and release() and both should consider the segmentation problem by combining adjacent memory areas. For both implementations, we found that the acquire() method has complexity of O(n). For doubly linked list we could have release() method to be of O(1) but it is O(n) for singly linked list. One advantage of doubly linked list is that we don't need to maintain the linked list sorted, which means that small segments are subject to accumulate at the beginning of the free list
Buddy Systems We describe two storage pool implementations that both use a linear list to keep track of the free areas. The singly-linked list should be sorted by address. For doubly-linked, the order of the areas is random. When allocating memory, the free lists are searched to find an area that is sufficiently large to satisfy the request. Which is of complexity O(n) for the worst case. In Buddy Systems, only limited range of sizes can be allocated. It maintains many free lists of memory areas of given allowed sizes.
Buddy Systems (cont'd) In a buddy system, we can only allocate areas of sizes powers of two. When a request is made for an area of size 2^k we first look in the corresponding free list. If there are no areas of that size left, we can obtain one by splitting an area of size 2^(k+1) in two. If there are no areas of size 2^(k+1) left, try 2^(k+2) and so on. Whenever an area is freed, we check to see if its buddy is also free. If free, combine them to generate a larger area and insert in the next larger list. Otherwise insert it in its list.
Buddy Systems (cont'd) The buddy of any block of length 2^k is determined by complementing the (k+1)th bit Example: assume that we have a memory of length 8 For blocks of size 4, the difference in address is in the third bit. 010 000 001 011 100 101 110 111
Buddy Systems: Allocation Algorithm If block of size (N) is requested, allocate a block of size 2^k where k = ceil(log N). Examine the free list avail[k] If the block of that size is available Remove a block from this list. If a block of size 2^k is unavailable, try a block of size 2 x 2^k split it into (buddies) one for the request, one for the free list of sizes k blocks. If no block of size 2 x 2^k is available, repeat for a block of size 4 x 2^k and so on.
Buddy Systems: Release Algorithm (cont'd) When a block is to be released, check whether its buddy is free If its buddy is free the two buddies should be combined Repeat combining into larger buddies recursively, until no more buddies can be combined.
Buddy System: Example Suppose that the allocated 16KB is returned 1 2 4 8 16 32 64
Buddy Systems: Adv. and Disadv. + Fast memory allocation: all what is needed is a simple recursive splitting operations. + Fast memory release and fast combining of free memory areas. - Internal fragmentation: specially if the requested size is slightly larger than a power of 2. - External fragmentation: because we can only combine a free block if its buddy is free.