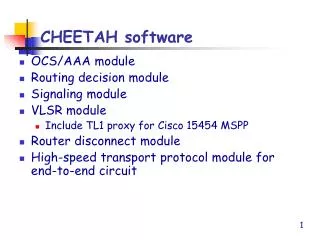
CHEETAH software
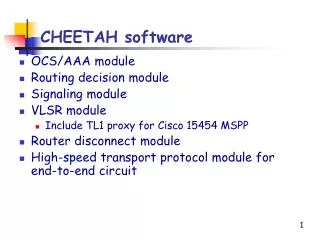
CHEETAH software. OCS/AAA module Routing decision module Signaling module VLSR module Include TL1 proxy for Cisco 15454 MSPP Router disconnect module High-speed transport protocol module for end-to-end circuit. End-host CHEETAH software. 1. 3. 4. Local testbed configuration. 2. 5.

CHEETAH software
E N D
Presentation Transcript
CHEETAH software • OCS/AAA module • Routing decision module • Signaling module • VLSR module • Include TL1 proxy for Cisco 15454 MSPP • Router disconnect module • High-speed transport protocol module for end-to-end circuit
1 3 4 Local testbed configuration 2 5
Proposed applications • End-to-end file transfers • Modified FTP/SFTP + FRTP • Video-telephony • Web application • High-speed optical Dial-Up Internet access service
Agenda • Router Disconnect • OCS • AAA
Router Disconnect • Research on possible router-disconnect solutions • Link Bundling (ingress decision support is needed). • Channelized Card • Traffic Shaping • Tried Link-bundling and Distributed Traffic Shaping router configuration. • Work in progress • Simulations for a paper on the above. • Router disconnect software.
Link-bundling - How it works • group multiple point-to-point links together into one logical link. A virtual interface is created for each link bundle • You can dynamically add and delete links to the virtual interface. The virtual interface is treated as a single interface on which you configure an IP address and other software features used by the link bundle, instead of configuring them on individual GE and POS interfaces. • Packets sent to the link bundle are forwarded on one of the links in the bundle. Load balancing is supported on all links in a bundle using per-destination load balancing based on a hash calculated using the source and destination IP addresses in the IP packet. Per-destination load balancing ensures that packets are delivered in order.
Channelized OC – How it works • Use Distributed Multilink PPP to bundle the channelized channels during the default mode. • Remove and add certain amount of component links (channelized channels) in the mode transfer.
Distributed Traffic Shaping – How it works • Shape the output traffic to the specified bit rate. Excessive packets are stored in a buffer in the traffic shaping queue and transmitted later. • Traffic Shaping does not recognize separate STS channels. DTS does not support channelized cards. Hence, it can not be used for router disconnect.
Software Interface Architecture • Interface software accepts signaling message (Cheetah circuit reserve or release message). • Interface software translates the signaling message to the according CLI language to control the router to do link-bundling or undundling. • Interface software acknowledges Cheetah host that the router-disconnect is done. Cheetah Host 1 2 Interface Software Singling Protocol Router 3
Simulations • Use OPNET to simulate router-disconnect. • Interested statistic parameters • Goodthroughput ratio(%)= Throughput before router disconnect / Throughput after router disconnect • Ftp response time ratio(%) = Ftp response time before router disconnect / Ftp response time before router disconnect • Other parameters ?
Agenda • Router Disconnect • OCS • AAA
OCS – Working Status • OCS server is configured (server address: 134.74.17.77) – using DNS software BIND (Berkeley Internet Name Domain). • TXT type resource record in DNS database is used to store OCS information. • Webpage is created for OCS lookup (No additional software is needed from the client side).
Agenda • Router Disconnect • OCS • AAA
AAA – Working Status • A proprietary AAA system is established. (Reference : http://www.stockholmopen.net) • Work in progress: • Install the Generic AAA • Compare the proprietary AAA and the Generic AAA • Interfacing either of the two AAAs for Cheetah system
Components of our AAA • Web server (134.74.17.77) • Radius client • Radius Server • Access Control daemon/scripts • DHCP server • PostgreSQL database (134.74.17.77/pg/)
Key features of RADIUS Accounting (RFC 2866) • Client/Server Model • Radius protocol uses a shared key to send the authentication and accounting messages. • A Network Access Server (NAS) operates as a client of the RADIUS server. The client is responsible for passing authentication and accounting information to a designated RADIUS server. • The RADIUS server is responsible for receiving the authentication and accounting request and returning a response to the client indicating that it has successfully received the request. • The RADIUS server can act as a proxy client to other kinds of AAA servers. • All transactions are comprised of variable length Attribute-Length-Value 3-tuples. New attribute values can be added without disturbing existing implementations of the protocol.
Generic AAA – RFC 2903, 2904 • The Basic Authorization Entities
Glossary • User -- the entity seeking authorization to use a resource or a service. • User Home Organization (UHO) -- An organization with whom the User has a contractual relationship which can authenticate the User and may be able to authorize access to resources or services. • Service Provider -- an organization which provides a service.
Single Domain Case • In general, the User Home Organization and the Service Provider are different entities or different "administrative domains". • In the simplest case, the User Home Organization and the Service Provider may be combined as a single entity. • We use Single Domain Case to describe three authorization sequences
Authorization Sequences • Agent sequences, • Pull sequences • Push sequences
Agent Sequences Example: A regular user may ask for 1 Mb/s bandwidth (1). The bandwidth broker (AAA Server) tells the router (Service Equipment) to set this user into the 1Mb/s "queue" (2). The router responds that it has done so (3), and the bandwidth broker tells the User the bandwidth is set up (4).
Pull Sequences • The pull sequence is what is typically used in the Dialin application, Mobile-IP proposal, and some QoS proposals. The User sends a request to the Service Equipment (1), which forwards it to the Service Provider's AAA Server (2), which evaluates the request and returns an appropriate response to the Service Equipment (3), which sets up the service and tells the User it is ready (4).
Push Sequences • The push sequence requires that the User get from the Service Provider's AAA Server a ticket or certificate verifying that it is o.k. for the User to have access to the service (1,2). The User includes the ticket in the request (3) to the Service Equipment. The Service Equipment uses the ticket to verify that the request is approved by the Service Provider's AAA Server. The Service Equipment then sends an o.k. to the User (4).
What is “Roaming” • Roaming -- the User Home Organization is not the Service Provider • Examples of roaming include an ISP selling dialin ports to other organizations or a Mobile-IP provider allowing access to a user from another domain.
Distributed Services • Any service that is provided by more than one Service Provider a distributed service • An example would be a user who requires a QoS service for a session that crosses multiple ISPs.
Policy • Policy Retrieval • Policy Evaluation • Policy Enforcement
Policy Retrieval • Policy definitions are maintained and stored in a policy repository by the organization that requires them. • Policy retrieval is typically done by the administration that defines the policy. • An example policy may define the times of day that a particular User is allowed to connect to the network.
Policy Evaluation • Evaluation of policy requires access to information referenced by the policy. • Often the information required is not available in the administration where the policy is retrieved. • For example, checking that a user is allowed to login at the current time can readily be done by the User Home Organization because the User Home Organization has access to current time. But authorizing a user requiring a 2Mb/s path with less than 4 hops requires information available at a Service Provider and not directly available to the UHO • So the UHO must either 1) have a way to query a remote administration for the needed information or 2) forward the policy to the remote administration and have the remote administration do the actual evaluation or 3) attempt somehow to "shadow" the authoritative source of the information (e.g by having the Service Provider send updates to the UHO).
Policy Enforcement • Policy Enforcement is typically done by the Service Provider on the Service Equipment. • Examples: • NAS enforces destination IP address limits via “filters”. • Router may enforces QoS restrictions on incoming packets.