TRUST Center Activities
200 likes | 555 Views
TRUST Center Activities. Stephen B. Wicker Cornell University. Center Activities. Focus on creative, collaborative events designed to stimulate and disseminate TRUST research Faculty/student workshops TRUST/AFOSR International Collaboration DHS collaboration External Advisory Board.

TRUST Center Activities
E N D
Presentation Transcript
TRUST Center Activities Stephen B. Wicker Cornell University
Center Activities • Focus on creative, collaborative events designed to stimulate and disseminate TRUST research • Faculty/student workshops • TRUST/AFOSR • International Collaboration • DHS collaboration • External Advisory Board Center Activities
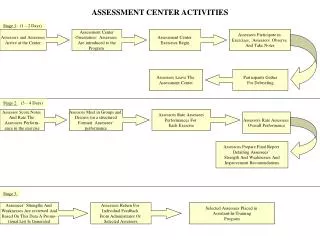
Exemplary Workshops • Participation from faculty, students, industry, and government. • Sensor Networking • Technology • Privacy Issues • Electronic Medical Records • Secure/Privacy-Aware Transport • Multi-Level Access • Computer Security • Trustworthy Interfaces • Securing E-Commerce • DHS • Beyond SCADA Center Activities
Sensor Networking Workshops • Sensor Networking Workshop - Cornell University, October 11, 2005 • Cornell CS, Information Science, ECE, Civil Engineering • New York Dept. of Health/Wadsworth Labs • Sample Talks: • Resilience in Critical Infrastructure Networks • Application Specific Sensor Networks • Co-Interpreting Sensor Networks • Tools for Enhancing Social Navigation in Public Spaces • Lipid Bilayer Sensors (Fabrication and Measurements) • SiC Based Betavoltaic radioisotope micro-batteries Center Activities
Sensor Networks and Privacy - Cornell University, March 28, 2006 • Cornell CS, Information Science, ECE, Civil Engineering • Berkeley Law School • Sample Talks: • The Future for Sensor Networking: Technology, Applications, and Policy Issues • Infrastructure Data and Security: Conflicting Agendas • Sensor Networks and Privacy Law • Sensor Networks in Public Spaces • Medical Sensor Networks: State of the Art • Privacy-Aware Approaches to Data Collection • Visualizing Spaces and the Sharing of Sensor Data Center Activities
Electronic Medical Records Workshops • Design Workshop for an Integrative Project related to Patient Portals- Vanderbilt University, December 16, 2005 • Vanderbilt CS, Medicine • Cornell ECE, Berkeley EECS • Sample Talks: Center Activities
Computer Security Workshops • Trustworthy Interfaces for Passwords and Personal Information - Stanford University, June 13, 2005 • Stanford, Berkeley, MIT • Bank of America, RSA, Microsoft • Sample Talks: • Trustworthy Interfaces for Passwords and Personal Information • Trusted Path in Heterogeneous Environments • Trusted Interfaces for Sensitive Data • Evolution of The Threat and its Impact on Requirements • Securing Online Transactions with a Trusted Digital Identity • Fixing the Web Trust Model • Trustworthy User Interface Design: Dynamic Security Skins • Delayed Password Disclosure Center Activities
Trustworthy Interfaces for Passwords and Personal Information II - Stanford University, June 19, 2006 • Statement of Purpose • Despite tremendous advances in computer technology in general and information security in particular, users still typically provide personal information and credentials such as passwords the same way they did 30 years ago: through a text interface that they assume they can trust. • The purpose of the workshop is to facilitate an effective solution to these problems by bringing together the designers of the cryptographic protocols with the implementers of the user interfaces. Center Activities
AF-TRUST-GNC • A new spinoff TRUST-related center focused on the needs of Air Force and other military vendors as the GIG/NCES rollout occurs • Will operate as a PRET with funding of about $1M per year. Emphasis is on mid-term to long-term opportunities, collaboration • Includes about 10 TRUST researchers Center Activities
The Proposed NCES/GIG Architecture? Center Activities
Need: Information Assurance & Security Tools • Problem • Assuring that legacy applications in a GIG setting can’t disrupt the GIG through malfunction (or malice) • Solution • Invent new containment options linking virtual private networks, virtual machine monitors, and powerful management tools to automate the administration and tracking of key material, firewall configuration information, and security policies. • Proof that this is feasible? • DETER containment for in-vitro study of viruses/worms Center Activities
Need: Scalability, Real-Time and Fault-Tolerance Tools • Problem • Many applications need R/T response, high availability, scalability • Web Services target operators of commercial data centers, where such requirements are relatively uncommon. • Solution • We will develop solutions and use them to augment the NCES/GIG technology base • Then work with the Air Force to ensure that standards bodies and vendors pick up the necessary solutions. • Proof that this is feasible? • Our team has an unparalleled track record in these areas • Web Services are a new “context” for this work and pose some new problems, but our prior work in related settings offers a deep technology base on which we can draw. Center Activities
Need: Discovery, Info. Arch., Mediation • Problem: • NCES includes a discovery component; it assists info consumers in finding providers . Existing WS standards don’t scale to large settings. • Scenario: airborne application needs radar imaging for a region over Faluja. Client must find the right sources; sources have affinity policies, platform has security policies. • Solution: • New technology options for service discovery and policy-based mediation • Explore vendor incentives to ensure that they will cooperate in developing needed information standards. avoiding stovepipe solutions • Feasibility • Our team is recognized for international leadership in new technologies for discovery, security and other policy representations and enforcement • TRUST brings us into close dialog with the major industry players and gives us leverage to establish needed standards Center Activities
International Collaboration • One of TRUST’s central goals: dissemination • Thrust: international collaboration • Focus: small number leading international groups • First major collaboration Taiwan • Authorized by Taiwan legislature • Personal attention from Taiwan Minister of State Center Activities
International collaborations: TAIWAN • About Taiwan • Internet users14.6 million • Broadband users 10.5 million • Population 22.7 million • In top three Asian software industry and web services industry (with Japan & South Korea) • Has a high incident of security incidents • Large fraction appear to originate from China Center Activities
Taiwan groups • TWISC: Taiwan Information Security Center • Modeled on TRUST • Major members • STAG: Science and Technology Advisory Group • Executive Branch group • Personally directed by a Minister-level staff member • NSC: National Science Council (Taiwan’s NSF) • III: Institute for Information Industry • Public/Private software industry coordinating group • ITRI: Industrial Technology Research Institute • Public/Private eloectronics industry coordinating group • Major infrastructure groups (telecoms) • Government groups (law enforcement, public safety, etc) Center Activities
Anticipated collaboration • Parliament authorized funds effective 4/1 for TRUST collaboration • Initial collaboration with Berkeley & CMU • Plans for extension throughout TRUST • Estimated level: $2 million/year • Directed by Dr. D. T. Lee • former NSF program officer Center Activities
DHS TRUST Activities • Phishing, Spyware and Identity Theft work started with initial seed funding from NSF (PM Maughan) • DETER testbed funded with joint NSF/DHS funding. DHS is transitioning the research testbed into an Operational Testbed to be named DECCOR starting July 2006. • DETER was used in a major national cyber attack and defense exercise called Cyberstrom in February 2006, details still need to be cleared for release by DHS. Center Activities
DHS/TRUST Activities • DHS has established a center of excellence at SRI which is strongly partnered with TRUST (the PI at SRI Lincoln is a former student of Mitchell’s). • DHS-Cybersecurity Center and TRUST participants have held numerous tech transfer forums for the financial sector including Schwab, Bank of America, Symmantec, Oracle, Sun, … and numerous start ups (usually every 3-4 months). Rodriguez (former USSS) has been the facilitator • TRUST will be organizing an identity theft workshop at the Oakland ACM/IEEE Security conference in May 2006 with DHS and USSS sponorship. Center Activities
DHS Workshop and Outreach Activities • Visits paid by Birman, Gehrke, Sastry, Reiter to US Dept of Treasury to discuss tech transfer to financial institutions. TRUST planning to hold workshop at Cornell’s Wall Street campus. • Visits paid and testimony given by Schneider, Sastry, Birman,… to House Science Committee, Senate Armed Services Committee, House Homeland Security Select Committee, House Intelligence Committee on privacy and security • NITRD/DHS “Beyond SCADA: Secure Networked Embedded Control Sysems” organized by TRUST with Wicker, Joseph, Karsai, … in March 2006. Center Activities