Developing an Information Technology Risk Management Program
Developing an Information Technology Risk Management Program Training for DHHS Information Security Officials and Backup Security Officials What this training covers . . What Risk Management means What NIST says you should do What ISO 17799 says you should do What C OBI T says you should do

Developing an Information Technology Risk Management Program
E N D
Presentation Transcript
Developing an Information Technology Risk Management Program Training for DHHS Information Security Officials and Backup Security Officials
What this training covers . . • What Risk Management means • What NIST says you should do • What ISO 17799 says you should do • What COBIT says you should do • What Microsoft says you should do • What HIPAA says you should do • What NC ITS says you should do • What DHHS says you should do • What you should do and when to do it
Risk “Take calculated risks. That is quite different from being rash.” General George S. Patton “Only those who risk going too far can possibly find out how far they can go” T.S. Elliot “Of course you have to go out on a limb sometimes; that’s where the fruit is”Unknown
Information Security is the protection of data against unauthorized access or modification
What is “Risk”? • Risk is the net mission impact considering both the likelihood that a particular threat-source will exercise (accidentally trigger or intentionally exploit) a particular information system vulnerability, and the resulting impact on the organization if this should occur (NIST) • Risk is the probability of a vulnerability being exploited in the current environment, leading to a degree of loss of confidentiality, integrity, or availability, of an asset. (Microsoft)
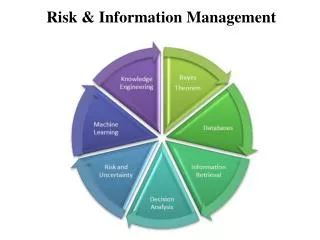
What is Risk Management? • The total process of identifying, controlling, and minimizing information system related risks to a level commensurate with the value of the assets protected • The goal of a risk management program is to protect the organization and its ability to perform its mission from IT-related risk
GoldenandSilver Rules of RM All risk is owned! Risk that is not assigned is owned by the organization’s Director
Why are we doing this? • Why do we do risk management? • Why does a car have brakes? A car has brakes so it can go fast We do risk management so we can take risks An organization that can take advantage of opportunities (and the inherent risks) will outlast an organization which cannot
Reactive Risk Management • Protect human life and people’s safety • Contain the damage • Assess the damage • Determine the cause of the damage • Repair the damage • Review response, and update policies
Proactive Risk Management Owners wish to minimize to reduce Controls impose value that may be reduced by that may possess Vulnerabilities may be aware of ThreatSources that exploit leading to Risk to give rise to that increase Threats to Assets wish to abuse and/or may damage
Proactive Risk Management Owners Controls Vulnerabilities ThreatSources Risk Threats Assets
Servers Desktop Computers Laptops and PDAs Switches and Routers Application software Development Tools Source Code VPN Access Backup Tapes Email Data Integrity All Files on the Server Consumer Information Network Infrastructure DHCP Web Site Availability Reputation Employee Morale What Assets are we Protecting?
Proactive Risk Management Owners Controls Vulnerabilities ThreatSources Risk Threats Assets
Protecting From What Threats? • Human Threats – Carelessness, Shoulder Surfing, User Abuse, Sabotage, Arson, Data Entry Errors, Intentional and Unintentional Procedure Violations • Technical Threats – Takeover of authorized session, Intrusion, Keystroke Eavesdropping, System Failure, Saturation of Resources • Environmental Threats – Fire, Earthquake, Hurricane, Tornado, Cable Cuts, Power Fluctuation, Hazardous Material Accident, Overheating
Proactive Risk Management Owners Controls Vulnerabilities ThreatSources Risk Threats Assets
Unlocked doors Unlocked windows Misconfigured systems Missing patches Antivirus out-of-date Poorly written apps Vendor backdoors Spyware Software Configuration Systems not monitored Unnecessary protocols Poorly defined procedures Stolen credentials Poor password protection Poor Disaster Recovery Violations not reported Threats to What Vulnerabilities?
Proactive Risk Management Owners Controls Vulnerabilities ThreatSources Risk Threats Assets
Proactive Risk Management Owners wish to minimize to reduce Controls impose value that may be reduced by that may possess Vulnerabilities may be aware of ThreatSources that exploit leading to Risk to give rise to that increase Threats to Assets wish to abuse and/or may damage
Two Approaches to Risk Assessment 1) Quantitative Risk Assessment • Value your assets • Determine the SLE (total amount lost from a single occurrence of the risk) Single Loss Expectancy • Determine the ARO (number of times you expect the risk to occur during one year) Annual Rate of Occurrence • Determine the ALE (amount you will lose in one year if the risk is not mitigated) Annual Loss Expectancy • Determine the ROSI (ALE before control) – (ALE after control) – (annual cost of control) = ROSI Return On Security Investment
Two Approaches to Risk Assessment 2) Qualitative Risk Assessment • Estimate relative values • Determine what threats each asset may be facing • Determine what vulnerabilities those threats might exploit in the future • Determine controls which will mitigate the risks, and the approximate cost of each control • Management performs a cost-benefit analysis on the results
Risks and assets are prioritized by financial values Results facilitate management of risk by Return on Security Investment Results expressed in terms management understands ($) Accuracy tends to increase over time Enables visibility and understanding of risk ranking Easier to reach consensus Not necessary to quantify threat frequency or determine financial value of assets Easier to involve people who are not experts on security or computers Comparing the Two Approaches – the BenefitsQuantitative Qualitative
Impact values assigned to risks are based on subjective opinion Very time-consuming Calculations can be very complex Results are presented only in monetary terms, and can be difficult for non-technical people to interpret Process requires expertise Insufficient differentiation between important risks Difficult to justify investing in control implementation when there is no basis for a cost-benefit analysis Results are dependent on the quality of the Risk Management Team that is created Comparing the Two Approaches – the DrawbacksQuantitative Qualitative
Effective Risk Management Threats Malicious attacks Sabotage Attempts to access private information Natural disasters User error Fraud Pranks Controls Protecting Data, Applications, LAN and Workstations Potential Damage Sensitive information disclosed Services and benefits interrupted Integrity of data and reports compromised Assets lost :Public’s Loss of confidence Failure to meet contractual obligations Critical operations halted
NIST - The National Institute of Standards and Technology • NIST is a non-regulatory Federal agency with the mission of developing and promoting measurement, standards and technology to enhance productivity and improve quality of life • They invent – an atomic clock; a cement-like substance that promotes bone regrowth • They develop - software for the 170 VA hospitals; complex computational models • The set standards – weights and measures, cholesterol testing, and . . . Information Security
Pertinent NIST Publications • SP 800-12 An Introduction to Computer Security: The NIST Handbook • SP 800-18 Guide for Developing Security Plans for Information Technology Systems • SP 800-26 Security Self-Assessment Guide for Information Technology Systems • SP 800-30 Risk Management Guide for Information Technology Systems
NIST SaysIt’s a Management Function • The goal of Risk Management is to protect the organization and its ability to perform its mission • The focus is the mission; not IT assets • Risk Management, therefore, is an essential management function of the organization
NIST SaysRisk Management has Three Parts • Risk Assessment - Determining where risks lie, and how big they are • Risk Mitigation - Prioritizing, evaluating, and implementing appropriate risk-reducing controls • Evaluation and Assessment – Since Risk Management is continuous and evolving, the past year’s Risk Management efforts should be assessed and evaluated prior to beginning the cycle again
Risk Management Process What is my risk? What will I do about it? How did I do? Risk Assessment Risk Mitigation RM Evaluation
National Institute of Standards and Technology SP 800-30The Ten Steps of Risk Assessment • System Characterization • Threat Identification • Vulnerability Identification • Control Analysis • Identify Threat-source/Vulnerability Pairs • Likelihood Determination • Impact Analysis • Risk Determination • Control Recommendations • Results Documentation
Risk Management Process What is my risk? What will I do about it? Risk Assessment Risk Mitigation
Risk Mitigation • Risk Mitigation is the process of identifying areas of risk that are unacceptable; and estimating countermeasures, costs and resources to be implemented as a measure to reduce the level of risk • Determining “appropriate risk-reducing controls” is a job for your Risk Management Committee
What is “Acceptable” Risk? • Setting your agency’s “risk appetite” is up to your Director and Senior Management • Because elimination of all risk is impossible, we must use the least-cost approach and implement the most appropriate controls to decrease mission risk to an acceptable level, with minimal adverse impact on the organization’s resources and mission
Risk Mitigation Options • Assumethe Risk – Accept the risk and continue operating (how big is your appetite?) • Avoidthe Risk – Stop running the program or sharing the data • Transferthe Risk – Use options to compensate for the loss, such as insurance • Lessenthe Risk – Implement controls that lessen the impact or lower the likelihood
Risk Mitigation Methodology • Prioritize based on risk levels presented • Evaluate recommended control options • Conduct a cost-benefit analysis • Select additional controls, as necessary • Assign responsibility • Develop an action plan, if necessary • Implement the selected controls
Cost-Benefit Analysis • If control reduces risk more than needed, see if a less expensive alternative exists • If control would cost more than the risk reduction provided, then find something else • If control does not reduce risk sufficiently, look for more controls or a different control • If control provides enough risk reduction and is cost-effective, then use it
Residual Risk • The risk remaining after the implementation of new or enhanced controls is the residual risk • If the residual risk has not been reduced to an acceptable level, the risk management cycle must be repeated to identify a way of lowering the residual risk to an acceptable level • Understand that no IT system can be risk-free
Risk Management Process What is my risk? What will I do about it? How did I do? Risk Assessment Risk Mitigation RM Evaluation
Evaluation and Assessment • People, systems, and networks change, so risk management must be ongoing • Federal agencies must conduct risk management at least every three years • Stay flexible to allow changes when warranted
NIST SaysGood Risk Management Depends Upon • Senior management’s commitment • Support of the IT Team • Competence of the Risk Management Committee • Cooperation and education of the users • Ongoing assessment of IT-related mission risks
ISO - International Organization of Standardization • In the late 1990s, the British Standard Institute (BSI) developed a program to accredit auditing firms, called “BS 7799” • When demand grew quickly for an information security standard, the ISO (International Organization for Standardization) adapted 7799 and released Part 1 in 2000 as “ISO 17799” • ISO 17799 defines a set of recommended information security management practices
On-line Purchases of ISO 17799 9 % 35 % 18% 9 % 6 % Others 9%
ISO 17799 – A Set of Recommendations • ISO does not expect you to apply every piece of the standard • Instead ISO suggests that you consider each recommendation as you try to improve your information security program • If a particular recommendation helps you address an important security need, then accept it – otherwise, ignore it
ISO 17799 Says “First, Understand” Perfect security may be achievable only for networkless servers located in rooms without doors in stone buildings without people on high ground with no earth faults in areas with very little rain
10 Key Contexts of ISO 17799 Security policy Compliance Organizational security Business continuity management Asset classification and control Integrity Confidentiality Information Systems development & maintenance Personnel security Availability Access control Physical and environmental security Communications and operations management