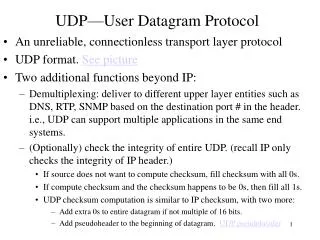
UDP: User Datagram Protocol
UDP: User Datagram Protocol. Chapter 12. Introduction. Multiple application programs can execute simultaneously on a given computer and can send and receive datagrams independently of each other Each executing program is called a process or a task (thus the term multitasking)

UDP: User Datagram Protocol
E N D
Presentation Transcript
UDP: User Datagram Protocol Chapter 12
Introduction • Multiple application programs can execute simultaneously on a given computer and can send and receive datagrams independently of each other • Each executing program is called a process or a task (thus the term multitasking) • Processes are created and destroyed dynamically • Then how can we identify a process on a remote machine as our destination?
Introduction • Each machine has a set of abstract destination points called protocol ports, identified by a positive integer • Most operating systems provide synchronous access to ports • the process is blocked until data arrives for it • ports are buffered so that data that arrives before a process is ready for it will not be lost • To communicate with a process, a sender needs to know the IP @ and the protocol port number
Introduction • Each message carries the number of the destination port on the destination machine, and the source port on the source machine
User Datagram Protocol • UDP provides the primary mechanism that application programs use to send datagrams to other application programs • UDP uses the underlying IP to transport a message from one machine to another • UDP is unreliable • UDP does not use acknowledgements, does not order incoming messages, does not provide flow control • UDP messages can be lost, duplicated, arrive out of order, or arrive to fast for the receiver to handle
User Datagram Protocol • UDP provides the ability to distinguish among multiple destinations in a host computer • Application programs that use UDP accept responsibility for reliability • Unfortunately, many applications that rely on UDP have not been thoroughly tested in a large TCP/IP environment and may fail
UDP Message Format • A UDP message is called a user datagram • It consists of two parts: • UDP header • source port (16 bits) - could be zero if not used • destination port (16 bits) • UDP message length (16 bits) - header and data • UDP checksum (16 bits) - optional for low overhead, guarantees that data arrives correctly • UDP data
UDP Pseudo-Header • Verifies that UDP datagram reaches its correct destination • specific machine and specific protocol port • UDP on the sending machine computes a checksum that covers the destination IP address and the UDP datagram • Since the IP is a layer “below” this, we must copy the IP addresses into a pseudo-header • This header is prepended to the UDP datagram
UDP Pseudo-Header • The information in the pseudo-header is used in calculating the checksum at the sender • But the pseudo-header is not transmitted with the UDP datagram • At the receiver, the checksum is calculated again, this time using the source and destination IP addresses that were in the IP header that carried the UDP message
UDP Pseudo-Header • To verify the checksum, the receiver extracts the fields (those shown in Figure 12.2) from the IP header, assemble them in the correct format and recompute the checksum • If the checksums agree, the message has reached the correct port on the correct destination machine
Encapsulation • UDP prepends a header to the data that a user sends and passes it to IP • IP prepends a header to what it receives from UDP • The network interface layer embeds the datagram in a frame before sending it from one machine to another - see Figure 12.4 • The format of the frame depends on the underlying network technology • On arrival, each layer removes a header...
Division of Duties • IP transfers data between a pair of hosts on an internet • only the IP header identifies source and destination hosts • UDP differentiates between multiple sources (or destinations) within one host • only the UDP header identifies the source or destination ports
Another Approach to UDP Checksum • Let UDP encapsulate the UDP datagram in an IP datagram, get addresses from IP, compute the UDP checksum and pass it on to IP to fill in the rest
Multiplexing, Demultiplexing and Ports • Think of a UDP port as a queue • UDP checks to see that the destination port number matches a port that is currently in use • If not found, an ICMP port unreachable message is sent and the datagram is discarded • If found, the new datagram is enqueued at the port of the appropriate application program
UDP Port Numbers • Computers need to agree on port numbers and their meaning • Well-known ports are permanently assigned for specific applications • see those assigned in Figure 12.6 • Dynamic binding • assigned by the network software when a program needs a port
Summary • Multiple application programs, often called processes, may run simultaneously • UDP distinguishes among them by their 16-bit protocol port identifier • Application programs using UDP must handle the reliability problem • Conceptually, the transport layer is independent of the Internet layer. But they interact strongly • the UDP checksum includes IP @ which must be gotten from IP
For Next Time • Read Chapter 13