Quantum Cryptography with Classical Cryptography Introduction
Quantum Cryptography with Classical Cryptography Introduction. Aaron Holladay and Joshua Pugh. Cryptography Concepts. Plaintext – the original message Ciphertext – the disguised message Encryption – any procedure to convert plaintext into ciphertext

Quantum Cryptography with Classical Cryptography Introduction
E N D
Presentation Transcript
Quantum Cryptographywith Classical Cryptography Introduction Aaron Holladay and Joshua Pugh
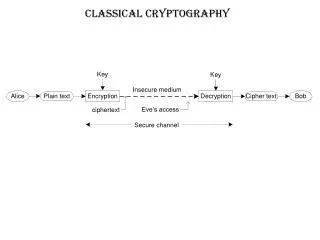
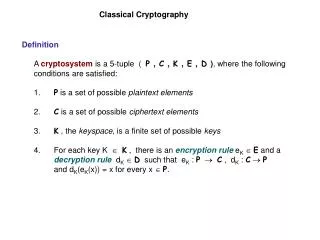
Cryptography Concepts Plaintext – the original message Ciphertext – the disguised message Encryption – any procedure to convert plaintext into ciphertext Decryption – any procedure to convert ciphertext into plaintext Key – label for a specific algorithm in the whole collection of algorithms in a cryptosystem
An Introduction… Cryptography – the art of creating and using cryptosystems Cryptosystem or cipher system – a method of disguising messages so that only certain people can see through the disguise
2 Types of Cryptosystems Symmetric - use the same (secret) key to encrypt and decrypt a message Asymmetric - use one key (the public key) to encrypt a message and a different key (the private key) to decrypt it. Asymmetric cryptosystems are also called public key cryptosystems.
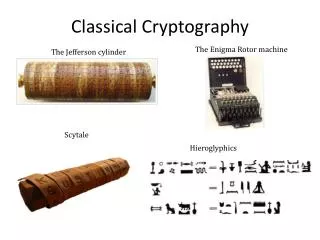
Symmetric Example and “History” Traditionally, the 2 parties would exchange 1 key in private to each other or over a secure connection and then the same key would be used to encrypt and decrypt the message. Supposedly, cryptography began when Julius Caesar sent messages to his trusted acquaintances, he didn't trust the messengers. So he replaced every A by a D, ever B by an E, and so on through the alphabet. Only someone who knew the "shift by 3" rule could decipher his messages.
Caesar-like Example… Text: HELLO WORLD Key: Shift each ASCII character right by 3 Encrypted Text: KHOOR#ZRUOG To Decrypt: Shift each character left by 3
Public-Key Cryptography • introduced by Diffie and Hellman in 1976 • Each person has a public and private key that are mathematical inverses of each other • So, if the public key does something like Caesar did, then each character would be shifted right by 3. The private key then shifts the characters left by 3. • want your function to be something that someone else could not find the inverse of
Problems?? • An absolute security of information cannot be guaranteed. It has to be possible to figure out the mathematical inverse, but this could be quite timely. • Can’t verify the author of a message • Won’t know if the message has been read by an eavesdropper or not
Digital Signatures…Second Problem Solved! Example: Bob and Alice create their public/private key pairs and exchange public keys. Then, Bob can use his private key to digitally sign his messages and Alice can use Bob's public key to verify the message is from Bob. Bob encrypts messages with Alice's public key and sends them to her and she decrypts them with her private key.
Current Uses The main public-key algorithm is RSA and was developed by Ron Rivest, Adi Shamir, and Leonard Adleman in 1977. This algorithm is included as part of web browsers from Netscape and Microsoft.
Quantum Concepts Quantum entanglement – a phenomenon in which the superposition of states (all possible states) of two or more systems allows the system to influence one another regardless of their spatial separation
Quantum Concepts cont… EPR (Einstein, Poldolsky and Rosen) paradox - As long as both photons remain unobserved, their properties remain indefinite, in a superposition of all states. But because of their common origin, the properties of the photons are correlated, or entangled. Ex. Through simple conservation of momentum, one knows that if one photon heads north, the other headed south. Consequently, measuring the momentum of one photon instantaneously determines the momentum of the other photon – even if it has traveled to the opposite end of the universe. While the two measurements remain probabilistic, they nevertheless are correlated.
Polarization of Photons There are four different polarizations of photons: Rectilinear polarizations: -0 degrees -90 degrees Diagonal polarizations: -45 degrees -135 degrees
2 Encryption Techniques • Parity Bits • Keys
Parity Bits One technique is to use parity bits throughout the transmission and if the polarization of the parity bits are not correct, then you know there was an eavesdropper.
Keys The sender sends photons with one of the four polarizations which are chosen at random. For each incoming photon, the receiver chooses at random the type of measurement: either rectilinear or diagonal. The receiver records the results and keeps them secret. The receiver then publicly announces the type of measurement, but not results and the sender tells the receiver which measurements were correct. The parties keep all cases in which the receiver’s measurements were correct, converts the measurements to binary, and this becomes the key.
Eavesdropping Quantum no-cloning – theorem states that it is impossible to make an exact copy of an unknown quantum state Thus it is virtually impossible to eavesdrop by reading photons from an entangled pair and then continue sending that photon in the stream without being detected.
The Reason The fundamental problem with classic private channel message/key transfers is that it can be monitored passively without the sender/receiver knowing. The act of measurement is an integral part of quantum mechanics, not just passive. The way that the quantum channel is designed it uses the theories of quantum mechanics so that any attempt to monitor the channel will disrupt the data in a detectable way.
Problems • Single photons on demand…a beam of light produced by a laser contains approximately 100 million billion photons per second…SOLVED…an individual photon can be released from a quantum dot embedded in a microdisk. • Distinguishing between line noise and eavesdropping • Sending photons over a large distance, but this problem has recently become less of an issue with the use of Quantum Repeaters
Future Use Future applications are in the most secure communication lines for bank-to-ATM transactions, financial information protection over the internet, and military and government communications including the use for ship-to-ship, ground-to-satellite, and satellite-to-satellite communication.
References Cryptography FAQ – http://www.faqs.org/faqs/cryptography-faq/ Cryptography: The Study of Encryption – http://world.std.com/~franl/crypto.html Public Key Cryptography – http://www.trustedweb.com/intro/public-key-cryptography.html What is Quantum Cryptography? – http://www.qubit.org/intros/crypt.html Quantum Cryptography, Scientific American, July 1992, http://dhushara.tripod.com/book/quantcos/aq/qcrypt.htm Quantum Cryptography and Communications – http://photon.bu.edu/sergienko/crypto.html Quantum Entanglement – http://www.wikipedia.com/wiki/quantum+entanglement Unconditional Security of Quantum Key Distribution over Arbitrarily Long Distances – http://www.sciencemag.org, March 26, 1999, Vol. 283. First Device That Produces Light – One Photon At a Time – http://ptg.djnr.com/ccroot/asp/publib/story.asp Did A Mouse Give Birth To The Universe? – http://www.uoregon.edu/~rlz/QM.html Single Photons on Demand – http://www.sciencemag.org/cgi/content/full/290/55002273?ijkey=sgvWC1gAd.O4M&keytype=ref&siteid=sci