Multipartite Viruses
Multipartite Viruses. Wendy Bowman ETEC 562. General Information. Activation. Payload. Removal. Transmission. Hidden. General Information. A computer virus is defined as a program or piece of code that is loaded onto your computer without your knowledge and runs against your wishes.

Multipartite Viruses
E N D
Presentation Transcript
Multipartite Viruses Wendy Bowman ETEC 562
General Information Activation Payload Removal Transmission Hidden
General Information • A computer virus is defined as a program or piece of code that is loaded onto your computer without your knowledge and runs against your wishes. • http://www.webopedia.com/TERM/v/virus.html
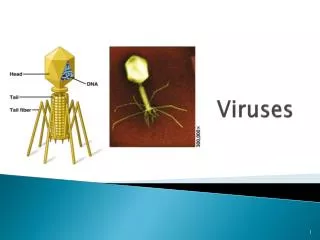
Viruses can replicate. All computer viruses are manmade. Can infect other programs. Viruses do not infect plain text files. Viruses take up memory after replicating. Viruses can not exist without a host. Viral Facts
Trojans and Stealth Boot Sector File Macros Worms Network and Multipartite viruses Types of Viruses
Network Viruses • Infect networks by making extensive use of network protocols. • Network viruses are able to transfer code to a remote server or workstation. Reference http://www.viruslist.com/eng/viruslistbooks.html?id=24
Separated into several segments that each run on a part of the network. Use automated functions such as email to replicate. Use programming built into the macros to spread themselves. Called an octopus when it has one main segment that coordinates with what the other segments are doing. Can steal password info and send it to a malicious source. Network Virus Facts http://www.kaspersky.com/news.asp?tnews=0&nview=1&id=157&page=0
Multipartite Viruses A multipartite virus is defined as a virus that infects your boot sectoras well as files.
Boot Sector The area of the hard drive that is accessed when the computer is first turned on. Back to Show
Can infect floppy disks. Hardest virus to clean. Are memory resident viruses. Harder to spread across networks but isn’t impossible. To spread across a network, the server must be infected and an infected program must be accessed. Multipartite Facts http://www.faqs.org/faqs/computer-virus/alt-faq/part1/
Viral Payload Payload is defined as the action the virus performs on the computer. http://www.antivirus.com/pc-cillin/vinfo/virusencyclo/glossary.asp#payload
Corrupts the hard disk Create files Delete files Modify files Formats the hard drive Hangs the system during rebooting Modifies available memory Modify available resources Possible Payloads http://www.antivirus.com/pc-cillin/vinfo/virusencyclo/
Refers to the condition or date in which the payload of the virus will occur. Computer can be infected for months or years before the payload occurs. Holidays are the most popular trigger date. http://www.antivirus.com/pc-cillin/vinfo/virusencyclo/glossary.asp#trigger_condition_or_date Activation or Trigger
Decrease the size of memory in BIOS, cut the last MCB (memory control block), and replicate in the free space left by the MCB Disguise the virus as part of a downloadable shareware package Interrupting the DOS language just enough to “hook” a viral code onto existing language (hooking) until a floppy disk can be infected. Hooking on to the debugger. Hidden Dangers http://www.virusbtn.com/VirusInformation/natas.html
Floppy disks CD-ROMs Shareware New software Network server Email attachments Hackers Downloading material from the Internet From here to there… http://www.cuyamaca.net/rachael.holloway/ppt/virus.ppt
Run anti-viral software Quarantine the virus (if possible) Replace the MBR (master boot record) Reboot computer from a clean disk then run anti-viral software Reformat the hard drive through DOS Costliest method, purchase a new memory chip Disposal
Payload General Information Activation Click Here! Transmission Hidden Removal
Writes its viral code to the last sector of the hard drive while overwriting data there. Memory resident DOS platform Infects .COM, .EXE, MBR, and floppy boot sectors Multipartite Uses 1024 bytes (files) and 512 bytes (MBR) Anthrax http://www.symantec.com/avcenter/vinfodb.html#
No aliases Memory resident Uses encryption Wild ( Can be transmitted through networks Infects .COM, floppy boot sector, hard disk boot sector Mainly, transmitted through emails Clisti 1025 and Clisti 1025 (b) http://www.symantec.com/avcenter/vinfodb.html#
Infects .COM, .EXE, MBR Memory resident Slowly encrypts the hard drive Uses 3155 bytes (files) and 512 bytes (MBR) Multipartite, stealthing, and polymorphic Transmitted through emails All encrypted data is lost when virus is removed One Half Boot http://www.symantec.com/avcenter/vinfodb.html#