Funkwerk UTM
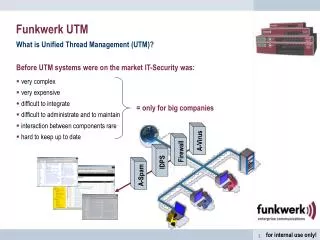
Funkwerk UTM. What is Unified Thread Management (UTM)?. Before UTM systems were on the market IT-Security was: very complex very expensive difficult to integrate difficult to administrate and to maintain interaction between components rare hard to keep up to date.

Funkwerk UTM
E N D
Presentation Transcript
Funkwerk UTM What is Unified Thread Management (UTM)? Before UTM systems were on the market IT-Security was: • very complex • very expensive • difficult to integrate • difficult to administrate and to maintain • interaction between components rare • hard to keep up to date = only for big companies A-Virus Firewall IDPS A-Spam
Firewall VPN Authentication Application Level Gateway Anti-Virus Intrusion Prevention Anti-Spam Auto Prevention Funkwerk UTM Unified Threat Management – Integrated “one size fits all” Protection Funkwerk PacketAlarm UTM
Funkwerk UTM Idea of Funkwerk UTM UTM Definition Unified Threat Management (UTM) is a term first used by IDC in 2004 to describe a category of security appliances which integrates a range of security features into a single appliance. By definition UTM appliances combine … firewall, gateway anti-virus, intrusion detection and prevention capabilities into a single platform! Funkwerk Unified Thread Management (UTM) means: • one solution for all major security threads • based on corporate security standards • out-of-the-box • easy implementation and easy administration • security components interact by default • good pricing • one update mechanism = for all companies sizes
Funkwerk UTM Unified Threat Management Components Firewall, Application Level Gateway • Multi Inspection Firewall with easy to use rule editor • Application Level Gateway (HTTP, FTP, SMTP, POP3, DNS) • Network- and Port-Address-Translation (Redirect Services) • DHCP server • Ethernet and DSL-capable (PPPoE) VPN Gateway • PPTP,L2TP und IPSec • Encryption: DES, 3DES, AES, Blowfish, Twofish, Serpent, Cast • Authentication: SHA-1, MD5, IKE certificate • IPSec NAT Traversal • Certificate Server
Funkwerk UTM Unified Threat Management Components Intrusion Prevention Engine • Blocks attacks in real-time before they reach the network • Protects from Worms, Trojans, network based attacks • Active inside the data stream • Flexible and easy implementation Auto Prevention • Easy adjustment through pre-defined policy levels • Definitions through Funkwerk expert team and automatic reaction to attacks • Reduces administration effort extremely • Online Update of policy levels • Feature only available with Funkwerk PacketAlarm UTM
Funkwerk UTM Unified Threat Management Components Auto/Prevention (Background) • Basic IPS Engines just offer a pure pattern base but without any deployment policy: what to do when which event shows up. There is no help to the administrator or the integrator (reseller) what to do and there is no value to such an “Marketing-IPS” (no reaction is more an IDS than an IPS). • Funkwerk’s Auto Prevention offers a complete pre-defined IPS-policy or IPS-logic with a single click. • Two policy-levels are available: normal and strong • Levels can be applied for all attack groups or user selected groups • Each new IPS signature update already has the policy classification => automatic prevention of new attacks (!) • Single groups or patterns can still be adjusted Source www.commtouch.com
Funkwerk UTM Unified Threat Management Components Anti-Spam • Anti-Spam for SMTP and POP3 • Real-time replication with multiple Blackhole-Lists (RBL + ORDB) • Heuristic Analyse of the content • White- und Black-Lists can be added • MIME header Check • Reactions defined based on spam rating • Transmission of the spam parameter inside the header for individual use • Optional: Advanced Detection Engine
Problem: • method causes false positives (Examples: moral, s-e-x, send text as picture, customer is on blacklists by accident) • fine-tuning is necessary but: If filter is to liberal then to much spam (false negative), if filter is to strict then false positives • languages • causes almost no false positives • no fine-tuning • very good detection ratio Funkwerk UTM Unified Threat Management Components Anti-Spam (Background) • Basic Engines look from “outside” on certain parameters of the email, e.g. words and content (text, html, pictures), subject, sender and server on blacklists or whitelists • Commtouch Engine looks with sensors worldwide on appearance of mass mails and gives each mail an individual fingerprint. Source www.commtouch.com
Funkwerk UTM Unified Threat Management Components Anti-Virus, Anti-Spyware, Anti-Phishing • Gateway virus protection for HTTP, FTP, SMTP, POP3 • Can handle multi-ziped files • Reactions: delete or quarantine • Definition of unwanted file formats • ClamAV included for free • Optional Update to Kaspersky Scan Engine User Authentication • Internal User Database • External LDAP Database • External RADIUS Database • Out-of-Band Authentication ->
Example 2: user access restrictions https http, ssh http, ftp, pop3 Funkwerk UTM Unified Threat Management Components Out-of-band Authentication protocol independent user authentication from both, internal to external and external to internal Example 1: Access from external e.g. OutlookWebAccess or SSH Intranet …. With OOBA insecure and sensitive services can be secured • very flexible: no client is needed (https) • sensitive services still can be accessed With OOBA users can be authenticated • very flexible: no client is needed (https) • independent of the workstation’s IP
Definition of Log Filter based on: Subsystem (FW, IPS, …) and Level (high, med., low, info) Log Layer Funkwerk UTM Unified Threat Management Components Flexible Event Logging (Sub-) System Events Firewall Virus Update IPS Mail ......... Internal Log SMTP (Email) Syslog SNMP V2 (Tivoli, OpenView) 100.000 entries max. Auto delete of oldest 1000
Funkwerk UTM Sales arguments • All-in-one security through PacketAlarm UTM’s Multi Layer Security Architecture • Very simple Installation through Setup-Wizard • Very easy config backup and roll-out with same configurations possible • Plug-and-secure functionality through Auto-Prevention (predefined prevention policies) • Security inside VPN connections (VPN-traffic still has to pass all security layers) • Centralized online signature and software update for all security components • Basic Spam and Virus Protection already included in base product • Virus scanning also for big files possible • Additional Kaspersky and Commtouch engine • User Authentication (OOBA, internal, LDAP, Radius, Certificates) • Centralized remote management solution • Easy configuration and administration (new FCI) • External logging via Syslog, SNMP and SMTP • flexible use – as stand alone system or in combination with existing security • Very good TCO
63,0 Virus’s /Worms/ Trojans Spam 55,8 Misuse of E-Mail addresses 27,2 23,8 Human miss-configuration 16,2 Phishing 10,6 External DoS attacks Misuse of user accounts 9,1 6,8 Guessed passwords Information in percent, base: 265 / 190 answers (multiple answers possible) Source: CRN 11/2006, IT-Security 2006 Funkwerk UTM Major security threads
Funkwerk UTM Unified Threat Management Components Multi Layer Security • Funkwerk UTM’s multi layer security architecture gives comprehensive security that is needed today on one single system. • All security layers inside Funkwerk UTM can be easily switched on or off. • If there is e.g. already a Firewall or an Anti-Virus-System installed these modules can be easily deactivated to fully integrate into existing security architectures. Auto Prevention Anti-Spam Intrusion Detection & Prevention Anti-Virus VPN Firewall
Funkwerk UTM Product line Funkwerk UTM - Matrix UTM 3500 (Gigabit) UTM 2500 +50 User + 499 € +50 User + 499 € +Unlim. User + 2000 € UTM 2100 UTM 1500 +25 User + 300 € +25 User + 300 € UTM 1100 Retail prices in € already including first year of Software & Pattern Update Software & Pattern Update for platform per following year (user independent)
new threat, (attack, vulnerability, virus) discovered Funkwerk UTM The security process – Update is a must! Software updates and patterns for: IPS Auto Prevention A-Virus A-SPAM Install and activate pattern New pattern developed Download of new patterns We’re not only selling a product once – we’re selling a long term service !!
Funkwerk UTM Stand-alone Solution small big medium
Funkwerk UTM Stand-alone Solution LAN to LAN Routing & Security LAN to WAN Routing & Security LAN, WAN, DMZ Routing & Security WAN WAN server
Centralized remote management Funkwerk UTM Branch office solution server Security within VPN!
Funkwerk UTM Mixed Product Solution Router / UTM Special requirements on WAN ISDN or S2M Backup DSL Modem X.21, ATM, FrameRelay, etc Security VPN
Funkwerk UTM Mixed Product Solution UTM / WLAN Telecommuters, customers, public etc. e.g. hotel, hospital, office …
Funkwerk UTM Mixed Product Solution
Funkwerk UTM Cross selling Basic ideas of FEC cross selling: • in every router project there must be security as you connect two or more networks • in every VoIP project there must be security as connection to the internet or VoIP providers is necessary • in every WLAN project there must be security as people access networks
Funkwerk UTM Roadmap 2007 Step 1 – Jan. 2007 • Product launch Funkwerk PacketAlarm UTM 1500 and UTM 2100 Step 2 – April 2007 • Product launch Funkwerk PacketAlarm UTM 1100 and UTM 2500 Step 3 – Q3 / 2007 • IMAP Proxy, Traffic shaping, Policy Based Routing, Content Check/Filter, DOS protection, RIP Step 4 – Q4 / 2007 • Integration into FEC network management system (NMS)
Funkwerk Enterprise Communication Vertriebsunterstützung und Partnerprogramm
Funkwerk Enterprise Communication Funkwerk PacketAlarm IDS und IPS
SQL Slammer MS Blaster Code Red Nimda TCP/IP Payload depth of inspection S D P Introduction – The Security Problem Depth of inspection Hybrid Threats like e.g. MS Blaster, Nimda, Code Red and SQL Slammer have proven, that Routers, Firewalls and Anti-Virus Systems are not enough to protect today’s company networks. Firewall Anti/Virus
TCP/IP Payload S D P depth of inspection PacketAlarm – First Class Security Scalable High-Level Security for every usage scenario. IDS IPS UTM
PacketAlarm IDS Features The solution: The PacketAlarm product family Intrusion Detection System (IDS) • High-Speed Intrusion Detection Engine • Monitors the complete data traffic in the whole network segment • Stores detailed attack data and can send out alerts • Powerful Vulnerability Scanner • Invisible inside the network • No influence on the performance and the traffic (passive sniffing) • Anomaly Detection • Event-Correlation • Traffic-trace • Automatic Software- and Pattern Update • Easy and simple configuration and administration • Central management and forensic over multiple systems
PacketAlarm IPS Features The solution: The PacketAlarm product family Intrusion Prevention System (IPS) • High-Speed Intrusion Prevention Engine • Active inside the data stream • Prevents actively from Worms, Trojans, network attacks etc. by blocking • Stores detailed attack data and can send out alerts • Automatic Software- and Pattern Update • Easy configuration and administration • Anomaly Detection • Traffic-Trace • Uses multiple correlation techniques to solve „false positive“ topic • Easy and flexible integration through implementation layer 2 or 3 • High Availability option • Central management and forensic over multiple systems
Target Markets PacketAlarm IDS/IPS Target customer segments Target markets for IDS: • medium to large size companies and enterprises IDS Examples: • Backbones of ISPs, Telcos • Network areas with a high demand on security and availability (IDS = passive sniffing) like production networks, power-plants, military, confidential and top secret development data, etc. Target markets for IPS: • medium to large size companies and enterprises IPS Examples: • Networks where Layer 3 integration is too costly (IPS in Layer 2 does not affect layer 3 infrastructure like routing, gateways etc. = easy implementation) • When only IPS functionality is needed (Firewall and IPS) e.g. securing internal server farms
IDS/IPS Product Line The solution: The PacketAlarm product family Product line IDS: PacketAlarm IDS 100 Unlimited user, for 100 Mbit/s networks PacketAlarm IDS 250 Unlimited user, for 1000 Mbit/s networks Product line IPS: PacketAlarm IPS 100 Unlimited user, for 100 Mbit/s networks PacketAlarm IPS 250 Unlimited user, for 1000 Mbit/s networks