IP QoS
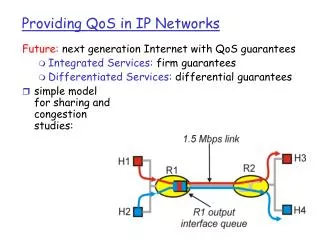
IP QoS. Authors names. Mohammad Joud Boris Dushkov Rashid Mijumbi. Definition , QoS Parameters and Need for QoS. Definition : Quality of Service (QoS) refers to the capability of a network to provide better service to selected network traffic over various technologies

IP QoS
E N D
Presentation Transcript
IP QoS Authorsnames • Mohammad Joud • Boris Dushkov • Rashid Mijumbi
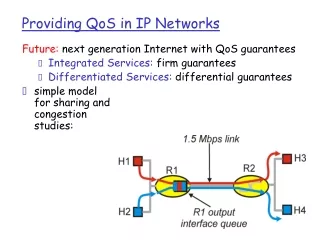
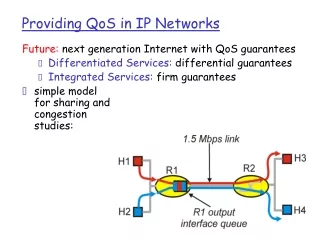
Definition, QoS Parameters and Needfor QoS • Definition:Quality of Service (QoS) refers to the capability of a network to provide better service to selected network traffic over various technologies • Parameters: Bandwidth (BW), Delay, Jitter, Packet Loss, Throughput - Data Rate • Need for Qos: • Network flexibility is becoming central to enterprise strategy • Traffic is bursty • Interactive voice, video applications have stringent bandwidth and latency demands IP QoS
Problem Statement • We have a limited pool of network resources that should be shared by different Applications or Users • How the different Applications or Users can be provided with different Quality of Service levels. • Which kind of tools can be useful for providing and Managing the different service levels.
IntServ Model (RFC 1633) Gives QoS guarantees at individual Applications flow level Resource Reservation Resources must be explicitly managed. Source Specifies Service Requirements Admission Control Service Commitments Individual Flows (Application Level Perfomance) Operates on an end-to-end level - Flow Specific state needs to be maintained in the router IP QoS
IntServ Model – Router Components Are there enough Resources ? Identification of Admitted Streams Source Data Stream Admission Control Packet Classifier Packet Scheduler Which queue is admitted first? ROUTER Specification of Service Requirements IP QoS
ResourceReservationProtocol (RSVP) PATH MESSAGE RESV MESSAGE IP QoS
RSVP ReservationProcess IP QoS
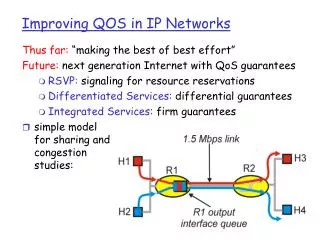
Differentiated Services • Agreements/service provided within a domain: • Service Level Agreement (SLA) with ISP; • Edge routers do traffic conditioning: • Perform “per-class” control (buffering, scheduling); • Mark packets with a small number of bits, each bit encoding represents a class or subclass – by using IPv4 header Type of Service or IPv6 Traffic Class field (called DS field); • Core routers: • Process packets based on packet marking and defined per hop behavior (PHB); • More scalable than IntServ: • No per flow state or signaling;
DiffServ Code Point Field • Packets are first divided into classes by marking the type of service (ToS) byte in the IP header; • A 6-bit bit-pattern (called the Differentiated Services Code Point (DSCP) in the IPv4 ToS Octet or the IPv6 Traffic Class Octet is used as shown below:
Per hop Behavior (PHB) • PHBs are typically implemented by means of buffer management and packet scheduling • All packets with the same DSCP are treated the same, Four types of classes available: • Default: traditional best effort treatment, for unsupported DSCP; • Class-Selector: • Backward compatibility, • 8 possible combinations (including default) ; • Expedited Forwarding (EF):providing low loss, low latency, low jitter, assured bandwidth, end-to-end service through DS domains; • Non-conformant traffic is dropped or shaped; • Assured Forwarding (AF): method by which Behavior Aggregates can be given different forwarding assurances • AF defines 4 classes with some bandwidth and buffers allocated to them; • Within each class, there are three drop priorities, which affect which packets will get dropped first if there is congestion;
Traffic condition block (TCB) • Classifier: Selects a packet in a traffic stream based on the content of some portion of the packet header; • Meter: Checks compliance to traffic parameters (ie: token bucket) and passes results to the marker and shaper/dropper to trigger action for in/out-of-profile packets; • Marker: Writes/rewrites the DSCP value; • Shaper: Delays some packets to be compliant with the profile;
DiffServ drawbacks • Traffic aggregation problems: • Class guarantees do not mean flow (user) guarantees -> Flows inside a class can “collide/interfere”; • Poor performance for real-time flows; • Good for small data transfers (web browsing); • Limited flexibility • Designed for relatively “static” networksNetwork topology, user traffic demands unchanging; • Difficult to change class resource allocations, Increase/decrease bandwidth per usage levels;
Qos management Supporting IP QoS requires some specific infrastructure, that have to use such basic concepts and algorithms: • Traffic description; • QoS specification and contract(Service Level Agreement, SLA); • QoS signalling(negotiation of theparameters in order to receive the required QoS); • Packet classification; • Resource Reservation; • Admission Control; • Traffic Policing(to detect any violation of the negotiated contracts); • Traffic Shaping(smoothing out any traffic burst); • Queuing and scheduling(allow multiple traffic sources to share bandwidth in the networks); • Congestion control and buffer management;
Traffic description • Sources need to provide an accurate description of their traffic to thenetwork, so that the network can properly allocate its resources to support required Qos; • Basic types of traffic: • CBR (Constant Bit Rate). Applications send traffic at a constant rate; • VBR (Variable Bit Rate). Applications send traffic at a variable rate; E.g.MPEG-VBR coded video where there are high scene changes (high bit rate) • Basic traffic parameters: • Peak rate -maximum data rate in any time interval; • Average rate - mean of the traffic rate (VBR); • Burst size - number of packets that can be delivered in the peak rate. VBR is bursty (generates traffic in bursts);
Qos specification and contract • A QoS contract (Service Level Agreement, SLA) is established betweencustomer and service provider; • QoS contract must include at least this information: • QoSguarantees (customers will precisely know what QoS are they going to get from the service); • QoSmonitoring (service providers will monitor the actual QoS parameters and compare them with the set of QoS parameters specified in the contract); • Charging (different charging schemes could be implemented, based on the values of the QoS parameters specified in the QoS contract);
Traffic Policing • To detect any violationof the negotiated contracts, we have to police all entering traffic; • Policing must be implemented at the edgeof the network-at therouters with direct connection to the users; • Traffic violating the contract must be dropped or taggedwith lower priority at the network entry; • Two basic algorithms of the policing: • Leaky Bucket; • Token Bucket;
Leaky Bucket • Only peak rate is policed; • Two parameters: • token leaking rate; • burst tolerance; • The token leaking rate is often called Committed Information Rate (CIR);
Token Bucket • Average rate and burst size are policed; • Two parameters: • token accumulation rate ; • burst tolerance; • With the single token bucket, the token accumulation rate is often called Committed Information Rate (CIR);
Traffic Shaping • Traffic shaping controls the shape of the traffic before sending it tothe network; • Traffic shaping limits the rate of transmission of data: • As a specific configured rate; • A derived rate based on the level of congestion; • If sources send traffic without shaping, packets may be detected asnonconforming and be discarded; • Shaping of traffic means: • Smoothing out any traffic burst; • Donot discard violating traffic, but to store them in actual buffers tosmooth it out; • Average-rate and burst-size shaping (The server sends packets from the incoming packet buffer as long as there are tokens in the token bucket)
Queuing and Scheduling • This two mechanisms allow multiple traffic sources to share bandwidth in the networks. • Queuing: • the process of buffering incoming packets at the entrance of a node; • one packet is transmitted at a time from one of the queues; • if a buffer gets full, packets are thrown according to the queuing algorithm: (FIFO, Priority Queuing (PQ), Round Robin (RR), Weighted Fair Queuing, etc.); • Scheduling: • scheduling algorithm defines the transmission schedule of packets from the queues over the link while multiple types of packets are waiting in different queues; • the choice of the queuing and schedulingalgorithms will define the Qos parameters of a traffic flow (packet loss rate, packet delay, etc.)
Traffic-engineering and QoS Improvements • Traffic-engineering Capabilities and QoS Improvements at Layer 3 – Router. • Using Protocols and some types of tools. • Changing Links coasts – Updating Routing tables. • What do we need from this tools? • Providing high-quality delivery with guaranteed minimum latency. • improving the quality of service is being immediately just for some of services. • The possibility of applying this tool when is needed and remove it at the end of this need. • Easy to use this tool and that is away from the complexities of programming. • Using it doesn't require a huge amount of information. IP QoS
Access Control Lists - ACLs are lists of instructions you apply to a router's interface. These lists tell the router what kinds of packets to accept and what kinds of packets to deny. Acceptance and denial can be based on certain specifications, such as source address, destination address, protocol, and port number. - An ACL is a group of statements that define how packets: • Enter inbound interfaces . • Relay through the router . • Exit outbound interfaces of the router . - ACLs can be used to: - Limit network traffic and increase network performance. - Provide traffic flow control. For example. - Provide a basic level of security for network access. - Decide which types of traffic are forwarded or blocked at the router interfaces. IP QoS
ACLsProcedure Let's suggest this network architecture: With applying some ACLs on Routers Interfaces we can reserve the least cost Link for the service that we need to improve its QoS. IP QoS
Testing packets with ACLs The order in which you place ACL statements is important. When the router is deciding whether to forward or block a packet, the Cisco Internetwork Operating System (IOS) software tests the packet against each condition statement, in the order in which the statements were created. IP QoS
How ACLs work IP QoS
ACL Test Matching Process IP QoS
ACLs Types 1- Standard ACLs • block all traffic from a network, allow all traffic from a specific network, or deny protocol suites. they will have a number between 1-99 2- Extended ACLs - Extended ACLs are used most often to test conditions because they provide a greater range of control than standard ACLs. You would use an extended ACL when you want to allow Web traffic but deny File Transfer Protocol (FTP) or telnet from non-company networks. Extended ACLs check for both source and destination packet addresses. They also can check for specific protocols, port numbers, and other parameters. This gives you more flexibility to describe what checking the ACL will do. Packets can be permitted or denied output based on where the packet originated and based on its destination. They will have a number between 100-199. for that we will use it to improve QoS. IP QoS
ACL Configuration Tasks • IP Address • Subnet mask • Subnetting • Protocols • Port Number • Router Interface • Wildcard Mask • A wildcard mask is a 32-bit quantity that is divided into four octets, with each octet containing 8 bits. A wildcard mask bit 0 means "check the corresponding bit value" and a wildcard mask bit 1 means "do not check (ignore) that corresponding bit value". IP QoS
Wildcard Mask IP QoS
ACL Commands For Extended ACLs Router(config)# access-list access-list-number {permit | deny} protocol source [source-mask destination destination-mask operator operand] [established] Router(config-if)#interface interface-name Router(config-if)#ip access-group access-list-number {in | out} Router(config)# no access-list access-list-number - Instead of typing 0.0.0.0 255.255.255.255 you can use the word any by itself as the keyword. - Instead of typing 172.30.16.29 0.0.0.0 you can use the word host in front of the address. IP QoS
Placing ACLs • The rule is to put the extended ACLs as close as possible to the source of the traffic denied. Standard ACLs do not specify destination addresses, so you have to put the standard ACL as near the destination as possible. IP QoS
Extended ACL Example • Extended ACL that blocks Talent traffic ( its port number is 23 ) from 172.16.4.0 being sent out interface E0 access-list 101 deny tcp 172.16.4.0 0.0.0.255 any eq 23access-list 101 permit ip any any interface Ethernet oip access-group 101 out IP QoS