Role Based Access Control
Role Based Access Control. Venkata Marella. Access Control System. Access control is the ability to permit or deny the use of a particular resource by a particular entity. Access control mechanisms can be used in managing physical resources, logical resources, or digital resources.

Role Based Access Control
E N D
Presentation Transcript
Role Based Access Control VenkataMarella
Access Control System • Access control is the ability to permit or deny the use of a particular resource by a particular entity. Access control mechanisms can be used in managing physical resources, logical resources, or digital resources.
Different Access Control Systems • Discretionary Access Control: Restricts access to objects based solely on the identity of users who are trying to access them. • Mandatory Access Control: Assign a security clearance to each user, and ensure that all users only have access to that data for which they have a clearance. • Role-Based Access Control
What is RBAC? • Role-Based Access Control Model is a nondiscretionary access control mechanism which allows & prompts the central administration of an organization specific security policy • Permission to perform an operation on an object is assigned to roles, not to users • Users are assigned to roles • Users acquire their permissions based on the roles they are assigned
The process of defining roles should be based on a thorough analysis of how an organization operates and should include input from a wide spectrum of users in an organization. • Permissions are defined based on job authority and responsibilities within a job function. • Operations on an object are invocated based on the permissions. • The object is concerned with the user’s role and not the user.
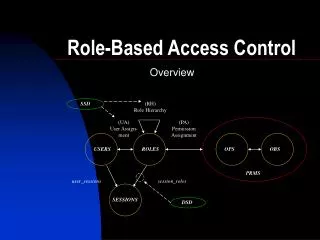
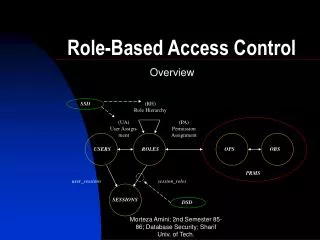
RBAC (UA)User Assignment OPERA TIONS OBJECTS ROLES USERS privileges user_sessions session_roles Sess- ions
Core Components • Defines: • USERS • ROLES • OPERATIONS (ops) • OBJECTS (obs) • User Assignments (ua) • Permissions (prms) • Sessions
Role-Based Access Control • RBAC supports three well-known security principles: • Least Privilege • Separation of duties • Data Abstraction • Least Privilege says that only minimum necessary rights should be assigned to a subject that requests access to a resource. • Separation of duties is achieved by ensuring that mutually exclusive roles must be invoked to complete a sensitive task. • Data abstraction is supported by means of abstract permissions such as credit and debit for an account. • The degree to which data abstraction is supported will be determined by the implementation details
Challenges in RBAC • Policy must be clearly defined or RBAC breaks down completely • Roles must be created that reflect business needs • Permissions for roles to access objects must be determined • Membership is each role must be determined
Advantage of RBAC • Once implemented RBAC simplifies system administration • Strong support for separation of duties • Good auditing support • Considered best practice by many
RBAC Simplifies System Administration • When a user changes positions • Her roles are changed to reflect her new position • Her replacement is assigned her old roles • No need to remove user’s old access on each object • If roles are well defined, the system administrator only needs to add a user to their assigned roles and the user has access to all the resources they require to complete their job
Separation of Duties • Manages conflict of interest policy • Reduces chances of fraud • Spreads critical duties across roles and in turn users • RBAC has built-in support for: • Static Separation of duties (SSD) • Dynamic Separation of duties (DSD)
RBAC Improves Auditing • User, role, and permission reviews are built into RBAC • Much easier to determine if an object should be accessed from a role instead of a person • Should Jane access the payroll object? ???
Disadvantages • This is good model for a static, closed, centralized organization where you can form a Role Hierarchy. But, this model is not efficient for distributed or dynamic system.
References • Ravi S. Sandhu“Role-Based Access Control “ • Gail - JoonAhn and Ravi Sandhu “Role-Based Authorization Constraints Specification” • Sandhu R. et. al. “Role-based Access Control Models”. IEEE Computer, 29(2):38-47 February 1996