Expert Toolkit for IP Addressing & Routing
E N D
Presentation Transcript
IP address https://store.theartofservice.com/the-ip-address-toolkit.html
Internet Protocol IP addressing and routing • IP addressing entails the assignment of IP addresses and associated parameters to host interfaces https://store.theartofservice.com/the-ip-address-toolkit.html
Internet Protocol IP addressing and routing • IP routing is also common in local networks. For example, many Ethernet switches support IP multicast operations. These switches use IP addresses and Internet Group Management Protocol to control multicast routing but use MAC addresses for the actual routing. https://store.theartofservice.com/the-ip-address-toolkit.html
IP address spoofing • In computer networking, IP address spoofing or IP spoofing is the creation of Internet Protocol (IP) packets with a forged source IP address, with the purpose of concealing the identity of the sender or impersonating another computing system. https://store.theartofservice.com/the-ip-address-toolkit.html
IP address spoofing Background • The basic protocol for sending data over the Internet network and many other computer networks is the Internet Protocol ("IP") https://store.theartofservice.com/the-ip-address-toolkit.html
IP address spoofing Background • In certain cases, it might be possible for the attacker to see or redirect the response to his own machine. The most usual case is when the attacker is spoofing an address on the same LAN or WAN. https://store.theartofservice.com/the-ip-address-toolkit.html
IP address spoofing Applications • The proliferation of large botnets makes spoofing less important in denial of service attacks, but attackers typically have spoofing available as a tool, if they want to use it, so defenses against denial-of-service attacks that rely on the validity of the source IP address in attack packets might have trouble with spoofed packets https://store.theartofservice.com/the-ip-address-toolkit.html
IP address spoofing Applications • IP spoofing can also be a method of attack used by network intruders to defeat network security measures, such as authentication based on IP addresses https://store.theartofservice.com/the-ip-address-toolkit.html
IP address spoofing Legitimate uses of IP spoofing • Spoofed IP packets are not a priori evidence of malicious intent; however, in performance testing of websites, hundreds or even thousands of "vusers" (virtual users) may be created, each executing a test script against the Web site under test, in order to simulate what will happen when the system goes "live" and a large number of users log on at once. https://store.theartofservice.com/the-ip-address-toolkit.html
IP address spoofing Legitimate uses of IP spoofing • Since each user will normally have their own IP address, commercial testing products (such as HP's Loadrunner software) can use IP spoofing, allowing each vuser its own "return address", as well. https://store.theartofservice.com/the-ip-address-toolkit.html
IP address spoofing Services vulnerable to IP spoofing • Configuration and services that are vulnerable to IP spoofing: https://store.theartofservice.com/the-ip-address-toolkit.html
IP address spoofing Services vulnerable to IP spoofing • RPC (Remote procedure call services) https://store.theartofservice.com/the-ip-address-toolkit.html
IP address spoofing Services vulnerable to IP spoofing • Any service that uses IP address authentication https://store.theartofservice.com/the-ip-address-toolkit.html
IP address spoofing Defense against spoofing attacks • Packet filtering is one defense against IP spoofing attacks https://store.theartofservice.com/the-ip-address-toolkit.html
IP address spoofing Defense against spoofing attacks • It is also recommended to design network protocols and services so that they do not rely on the IP source address for authentication. https://store.theartofservice.com/the-ip-address-toolkit.html
IP address spoofing Upper layers • Some upper layer protocols provide their own defense against IP spoofing attacks https://store.theartofservice.com/the-ip-address-toolkit.html
IP address spoofing Other definitions • The term spoofing is also sometimes used to refer to header forgery, the insertion of false or misleading information in e-mail or netnews headers. Falsified headers are used to mislead the recipient, or network applications, as to the origin of a message. This is a common technique of spammers and sporgers, who wish to conceal the origin of their messages to avoid being tracked down. https://store.theartofservice.com/the-ip-address-toolkit.html
IPv4 address exhaustion - IP addressing • Every node of an Internet Protocol (IP) network, such as a computer, router, or network printer, is assigned an IP address that is used to locate and identify the node in communications with other nodes on the network. Internet Protocol version 4 provides 232 (4,294,967,296) addresses. However, large blocks of IPv4 addresses are reserved for special uses and are unavailable for public allocation. https://store.theartofservice.com/the-ip-address-toolkit.html
IPv4 address exhaustion - IP addressing • The IPv4 addressing structure provides an insufficient number of publicly routable addresses to provide a distinct address to every Internet device or service. This problem has been mitigated for some time by changes in the address allocation and routing infrastructure of the Internet. The transition from classful network addressing to Classless Inter-Domain Routing delayed the exhaustion of addresses substantially. https://store.theartofservice.com/the-ip-address-toolkit.html
IPv4 address exhaustion - IP addressing • In addition, network address translation (NAT) permits Internet service providers and enterprises to masquerade private network address space with only one publicly routable IPv4 address on the Internet interface of a customer premise router, instead of allocating a public address to each network device. Complicating matters, IPv6-unaware NAT devices break native and 6to4 IPv6 connectivity, and a large fraction break 6in4 tunnels. https://store.theartofservice.com/the-ip-address-toolkit.html
IPv4 address exhaustion - Markets in IP addresses • The creation of markets to buy and sell IPv4 addresses has been considered to be a solution to the problem of IPv4 scarcity and a means of redistribution. The primary benefits of an IPv4 address market are that it allows buyers to maintain undisrupted local network functionality. IPv6 adoption, while in progress, is currently still in early stages. It requires a significant investment of resources, and poses incompatibility issues with IPv4, as well as certain security and stability risks. https://store.theartofservice.com/the-ip-address-toolkit.html
IPv4 address exhaustion - Markets in IP addresses • The creation of a market in IPv4 addresses would only delay the practical exhaustion of the IPv4 address space for a relatively short time, since the public Internet is still growing. https://store.theartofservice.com/the-ip-address-toolkit.html
IPv4 address exhaustion - Markets in IP addresses • The concept of legal ownership of IP addresses as property is explicitly denied by ARIN and RIPE NCC policy documents and by the ARIN Registration Services Agreement, although ownership rights have been postulated based on a letter from the National Science Foundation General Counsel https://store.theartofservice.com/the-ip-address-toolkit.html
IPv4 address exhaustion - Markets in IP addresses • Ad-hoc trading in addresses could lead to fragmented patterns of routing that could expand the global routing table. https://store.theartofservice.com/the-ip-address-toolkit.html
IPv4 address exhaustion - Markets in IP addresses • Microsoft bought 666,624 IPv4 addresses from Nortel's liquidation sale for 7.5 million dollars in a deal brokered by Addrex https://store.theartofservice.com/the-ip-address-toolkit.html
Internet Assigned Numbers Authority - IP addresses • IANA delegates allocations of IP address blocks to Regional Internet Registries (RIRs). Each RIR allocates addresses for a different area of the world. Collectively the RIRs have created the Number Resource Organization formed as a body to represent their collective interests and ensure that policy statements are coordinated globally. https://store.theartofservice.com/the-ip-address-toolkit.html
Internet Assigned Numbers Authority - IP addresses • The RIRs divide their allocated address pools into smaller blocks and delegate them in their respective operating regions to Internet service providers and other organizations. Since the introduction of the CIDR system, IANA typically allocates address space in the size of /8 prefix blocks for IPv4 and /23 to /12 prefix blocks from the 2000::/3 IPv6 block to requesting regional registries as needed. https://store.theartofservice.com/the-ip-address-toolkit.html
HTTP cookie - IP address • Some users may be tracked based on the IP address of the computer requesting the page. The server knows the IP address of the computer running the browser or the proxy, if any is used, and could theoretically link a user's session to this IP address. https://store.theartofservice.com/the-ip-address-toolkit.html
HTTP cookie - IP address • IP addresses are, generally, not a reliable way to track a session or identify a user. Many computers designed to be used by a single user, such as office PCs or home PCs, are behind a network address translator (NAT). This means that several PCs will share a public IP address. Furthermore, some systems, such as Tor, are designed to retain Internet anonymity, rendering tracking by IP address impractical, impossible, or a security risk. https://store.theartofservice.com/the-ip-address-toolkit.html
Social VPN - Private IP address space • A social VPN uses dynamic IP address assignment and translation to avoid collision with existing (private) address spaces of end hosts, and to allow the system to scale to the number of users that today's successful online social network services serve (tens of millions). Users are able to connect directly only to a small subset of the total number of users of such a service, where the subset is determined by their established relationships. https://store.theartofservice.com/the-ip-address-toolkit.html
Anonymous blogging - IP Addresses • They hence fully revealing location of the device, making IP addresses are one of the most popular ways to track and reveal identities as well as physical location. https://store.theartofservice.com/the-ip-address-toolkit.html
Anonymous blogging - IP Addresses • Typical of the attitude of internet companies, Google will only reveal an IP address identity on being served a valid court order, as they did in 2007 when the anonymous Skanks in NYC blog attacked Liskula Cohen, a 37-year-old who had modeled for Australian Vogue, Georgio Armani and Versace https://store.theartofservice.com/the-ip-address-toolkit.html
Anonymous blogging - IP Addresses • In China, while legislation and court orders do not directly exist, from 2007 a number of Chinese blog service providers signed the so-called "self-discipline" pact. The pact does not force, but rather "encourages" Internet companies to register and store the real names, addresses and other details of their users. https://store.theartofservice.com/the-ip-address-toolkit.html
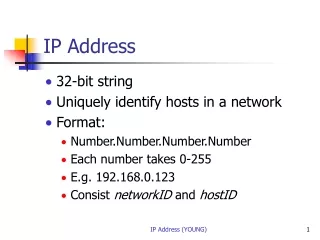
IP address • The designers of the Internet Protocol defined an IP address as a 32-bit number and this system, known as Internet Protocol Version 4 (IPv4), is still in use today. However, due to the enormous growth of the Internet and the predicted depletion of available addresses, a new version of IP (IPv6), using 128 bits for the address, was developed in 1995. IPv6 was standardized as RFC 2460 in 1998, and its deployment has been ongoing since the mid-2000s. https://store.theartofservice.com/the-ip-address-toolkit.html
IP address • Two versions of the Internet Protocol (IP) are in use: IP Version 4 and IP Version 6. Each version defines an IP address differently. Because of its prevalence, the generic term IP address typically still refers to the addresses defined by IPv4. The gap in version sequence between IPv4 and IPv6 resulted from the assignment of number 5 to the experimental Internet Stream Protocol in 1979, which however was never referred to as IPv5. https://store.theartofservice.com/the-ip-address-toolkit.html
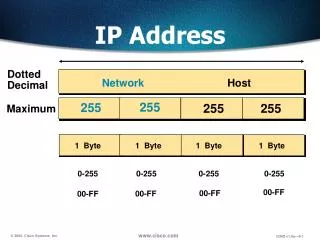
IP address • In IPv4 an address consists of 32 bits which limits the address space to 4294967296 (232) possible unique addresses. IPv4 reserves some addresses for special purposes such as private networks (~18 million addresses) or multicast addresses (~270 million addresses). https://store.theartofservice.com/the-ip-address-toolkit.html
IP address • IPv4 addresses are canonically represented in dot-decimal notation, which consists of four decimal numbers, each ranging from 0 to 255, separated by dots, e.g., 172.16.254.1. Each part represents a group of 8 bits (octet) of the address. In some cases of technical writing, IPv4 addresses may be presented in various hexadecimal, octal, or binary representations. https://store.theartofservice.com/the-ip-address-toolkit.html
IP address • In the early stages of development of the Internet Protocol, network administrators interpreted an IP address in two parts: network number portion and host number portion. The highest order octet (most significant eight bits) in an address was designated as the network number and the remaining bits were called the rest field or host identifier and were used for host numbering within a network. https://store.theartofservice.com/the-ip-address-toolkit.html
IP address • This early method soon proved inadequate as additional networks developed that were independent of the existing networks already designated by a network number. In 1981, the Internet addressing specification was revised with the introduction of classful network architecture. https://store.theartofservice.com/the-ip-address-toolkit.html
IP address • The first three bits of the most significant octet of an IP address were defined as the class of the address https://store.theartofservice.com/the-ip-address-toolkit.html
IP address • Historical classful network architecture https://store.theartofservice.com/the-ip-address-toolkit.html
IP address • Classful network design served its purpose in the startup stage of the Internet, but it lacked scalability in the face of the rapid expansion of the network in the 1990s. The class system of the address space was replaced with Classless Inter-Domain Routing (CIDR) in 1993. CIDR is based on variable-length subnet masking (VLSM) to allow allocation and routing based on arbitrary-length prefixes. https://store.theartofservice.com/the-ip-address-toolkit.html
IP address • Today, remnants of classful network concepts function only in a limited scope as the default configuration parameters of some network software and hardware components (e.g. netmask), and in the technical jargon used in network administrators' discussions. https://store.theartofservice.com/the-ip-address-toolkit.html
IP address • Early network design, when global end-to-end connectivity was envisioned for communications with all Internet hosts, intended that IP addresses be uniquely assigned to a particular computer or device. However, it was found that this was not always necessary as private networks developed and public address space needed to be conserved. https://store.theartofservice.com/the-ip-address-toolkit.html
IP address • Computers not connected to the Internet, such as factory machines that communicate only with each other via TCP/IP, need not have globally unique IP addresses. Three ranges of IPv4 addresses for private networks were reserved in RFC 1918. These addresses are not routed on the Internet and thus their use need not be coordinated with an IP address registry. https://store.theartofservice.com/the-ip-address-toolkit.html
IP address • Today, when needed, such private networks typically connect to the Internet through network address translation (NAT). https://store.theartofservice.com/the-ip-address-toolkit.html
IP address • Any user may use any of the reserved blocks. Typically, a network administrator will divide a block into subnets; for example, many home routers automatically use a default address range of 192.168.0.0 through 192.168.0.255 (192.168.0.0/24). https://store.theartofservice.com/the-ip-address-toolkit.html
IP address • IPv4 address exhaustion is the decreasing supply of unallocated Internet Protocol Version 4 (IPv4) addresses available at the Internet Assigned Numbers Authority (IANA) and the regional Internet registries (RIRs) for assignment to end users and local Internet registries, such as Internet service providers https://store.theartofservice.com/the-ip-address-toolkit.html
IP address • The rapid exhaustion of IPv4 address space, despite conservation techniques, prompted the Internet Engineering Task Force (IETF) to explore new technologies to expand the addressing capability in the Internet https://store.theartofservice.com/the-ip-address-toolkit.html
IP address • The primary intent of the new design is not to provide just a sufficient quantity of addresses, but rather to allow an efficient aggregation of subnetwork routing prefixes at routing nodes https://store.theartofservice.com/the-ip-address-toolkit.html