Secure Ad-Hoc On-Demand Vector Routing and Distributed Key Management Overview
This document provides an in-depth overview of Secure Ad-Hoc On-Demand Distance Vector (SAODV) routing and distributed key management techniques. It explores the authentication and integrity challenges within AODV, highlighting the need for secure source node verification and data integrity checks. The advantages and disadvantages of SAODV are discussed in relation to digital signatures and potential tampering. It further delves into an efficient key management approach for dynamic collaborative groups, emphasizing Group Diffie-Hellman and key agreement protocols, addressing security requirements, group membership dynamics, and the balance between efficiency and security.

Secure Ad-Hoc On-Demand Vector Routing and Distributed Key Management Overview
E N D
Presentation Transcript
SAODV and Distributed Key Management Mark Guzman, Jeff Walter, Dan Bress, Pradhyumna Wani
Agenda • SAODV • AODV • Authentication and Integrity • Distributed Key Management • Overview • Advantages • Disadvantages
AODV • Ad-Hoc On-Demand Distance Vector Routing • Reactive route discovery • Contains no security (no authentication of source nodes, no data integrity checking)
AODV • RREQ, RREP, RERR • Each node maintains a routing table of destination nodes • Each node uses sequence numbers to check ‘freshness’ of routes
SAODV • Secure Ad-Hoc On-Demand Distance Vector Routing • Authentication- must verify source node’s identity • Data integrity- information passed through routing packets must not be tampered with
Authentication • Digital signatures (asymmetric, one public and private key per node) • No specific key distribution system • Possibility of certificates
Integrity • Mutable (hop count) vs. immutable (source and destination IP addresses) information • Use Hash Chains to help secure the hop count • Digital Signatures prevent tampering of immutable data
Issues • High cost of using digital signatures • Nothing to prevent some kinds of tampering of the hop count • No exact key distribution system • Man in the middle and tunneling attacks not prevented • No mention of how to secure the process of joining group
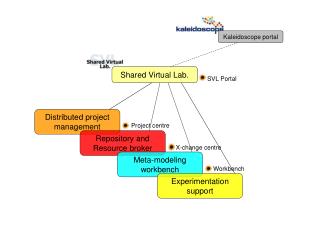
Distributed Key Mangement • Simple and Fault-Tolerant Key Agreement for Dynamic Collaborative Groups
Overview • Efficient Key Management required to provide secure and reliable group communication • Problem domain • Dynamic Membership • Distributed and Collaborative System
Key Management Solution • Group Diffie-Hellman • Secured Key exchanged between nodes • Key Tree • Efficient Key calculation
Key Trees • Efficiency • Tree Balancing • Private and Public (blinded) Keys
Communication • Group Key Agreement • View Synchrony • Guarantees group members receive same set of messages • Sender’s requested message order preserved
Group Membership Events • JOIN • LEAVE • MERGE • PARTITION
JOIN • Role of sponsor
Cascaded Events • Event A occurs, and during its processing event B occurs. • This is handled using re-entrance. • Partially mitigated by VS usage
Security • Cryptographic Requirements • Group Key Secrecy • Forward Secrecy • Backward Secrecy • Key Independence
Security cont. • Security features of the protocol • Each node contributes to group key • Node’s shares are secret • Group membership fluctuation handled • All messages are signed by senders
Complexity • Broadcast • Tree Calculation