Firewall Survey
80 likes | 738 Views
Firewall Survey CIS600 Internet Security Principles Seongsu, Woo Jongshik, Her Firewall Basics What is a Firewall? A system enforcing an access control policy between two networks.

Firewall Survey
E N D
Presentation Transcript
Firewall Survey CIS600 Internet Security Principles Seongsu, Woo Jongshik, Her
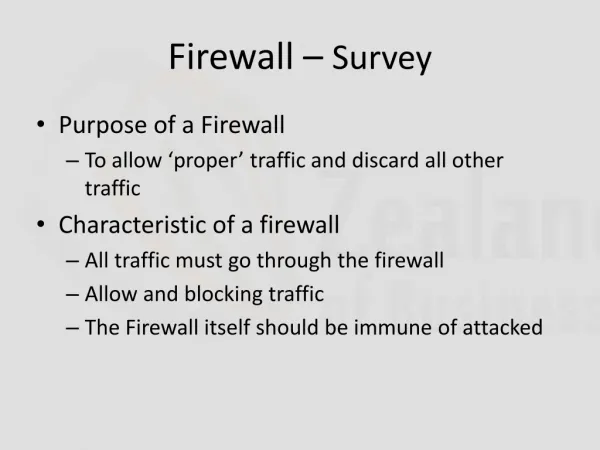
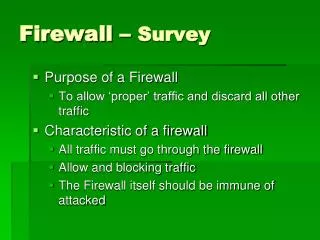
Firewall Basics What is a Firewall? • A system enforcing an access control policy between two networks. • Some emphasize on blocking traffic, while other emphasize on permitting traffic. Why use Firewalls? • Keeps intruders out of your network while still letting you get your job done • Protect sensitive information • Good place to store files, bug-fixes, etc.. What can a firewall protect against? • Unauthenticated logins : Vandals logging into machines on your network • Block traffic from outside to inside, but still permit users on the inside to communicate freely with the outside. • Single “choke point” What can’t a Firewall protect against? • Attacks that don’t go through the firewall:Back-door entrances into your network • Traitors inside your network:Industrial spy • Stupid users: Intruders can completely bypass your firewall, if they can find a “helpful” employee What about viruses? • Firewalls can’t protect very against them Too many ways of encoding binary files • Too many different architectures • Firewalls cannot protect against data-driven attacks • Attack that is in the form of innocuous-seeming data that is copied to an internal host where it is then executed.
Network Level Firewalls • Make their decisions based on the source, destination addresses and ports in individual IP packets. • Originally, they used simple routers that where not able to make sophisticated decisions about what a packet is actually talking to or where it actually came from. • Modern network level firewalls have become more sophisticated, and now maintain internal information about the state of connections passing through them, and the contents of the data stream. • They route traffic directly through them • so to use one you usually need to have an assigned IP address block. • They tend to be very fast and transparent to users Application Level Firewalls • Can be thought of as hosts running proxy servers • Permit no traffic directly between networks • Perform elaborate logging and auditing of traffic passing through them • Can be used as network address translators • Traffic goes in one “side” and out the other • After having passed through an application that effectively masks the origin of the initiating connection. • Having an application in the way may impact performance and may make the firewall less transparent • Provide more detailed audit reports and tend to enforce more conservative security models than network level firewalls
Introduction of personal firewall Most typical user cannot be expected to understand security weakness of their OS or Networks because of its complexity. The important tool for defending Windows was the anti-virus software, but it is no longer enough. The personal firewall may become an essential tool for Windows users connected to vulnerable networks. The personal firewalls allow both beginner and expert users to protect their PCs. Basically, there is a significant risk of information being stolen or destroyed. Your PC can be misused to attack others, or used to access banking software; or simply of PC/network resources wasted.
Benefits for using personal firewall • Protect Windows from network attacks. • If an infected email should install a back door (like BackOrifice), the personal firewall will still prevent network access to the backdoor. • People who connect to the corporate LAN via Internet VPNs may be exposing the corporate intranet. With a personal firewall installed, VPNs on the Internet do not pose as much of a risk. • Ensure that your PC is not used to attack others. • Check points for Choosing a Personal Firewall • Security protection: penetration, Trojans, controlling leaks, denial of service. • Intrusion detection: alerting of dangerous attacks. • Reaction: discovering identity of attacker, blocking attacks. • User interface: ease of use, simplicity, online help, rules setup • Price: how much are you willing to pay?
How and What did we test the firewalls? • Port scanners (Nmap and Nessus) were run against each product to check that incoming ports were effectively blocked. • Trojans(Firehole, Tooleaky) were installed on the test system and run against each product to check that outgoing ports were effectively blocked. • We'll examine the following on each of the firewalls in our test. • Default options : Default installations are typical in many production environments. They also make it easy for an attacker to gain access to the target system. • Basic filter rules : These rules allow traffic out and block frequently attacked ports. We'll analyze the active response and alerting capabilities of each product. • Note on Trojans • We tested these products with Firehole and Tooleaky. • Trojans can leak information by sending it out via standard ports that the firewall probably allows by default (e.g., port 80).
Test environment Direct connection Attack Server OS: Redhat Linux 2.2.16-22 IP Address: 192.168.0.1 Port scanners: Nessus v1.0.9 Nmap v 2.54 beta 30 Test Server OS: Microsoft Windows 2000 Professional Edition IP Address: 192.168.0.2 Firewalls: Zone Alarm v 2.6.362 Sygate Personal Firewall v 4.2 Tiny Personal Firewall v 2.0.14 Trojans: Firehole, Tooleaky