System Penetration with Metasploit Framework
System Penetration with Metasploit Framework. Presentation by Rob Bobek. Content. Part I: System Penetration Many Attack Vectors Understanding Software Exploitation Attacks Understanding Exploits Understanding Payloads Metasploit Framework Understanding MSF Part II:

System Penetration with Metasploit Framework
E N D
Presentation Transcript
System Penetration with Metasploit Framework Presentation by Rob Bobek
Content • Part I: • System Penetration • Many Attack Vectors • Understanding Software Exploitation Attacks • Understanding Exploits • Understanding Payloads • Metasploit Framework • Understanding MSF • Part II: • Snort Introduction • Understanding Snort • Snort Installation/Configuration • IDScenter Configuration • The Attack Experiment • Network Topology and Hardware Configuration/Details • Software Details • Vulnerability Details • Conducting the Attack • Snort Observations • References • Questions
Part I – System Penetration • What do I mean by System Penetration? The act of successfully breaching security on a remote computer system in order to gain some form of control access. • So, what is Metasploit Framework? • First we need to learn some basic concepts before understanding what the Metasploit Framework is and what it is capable of providing.
Many Attack Vectors! • Gaining access to a secured system can be a difficult task that requires skill and maybe luck. However, we have also have plenty of simple techniques, commonly used today, to achieve the same result. Such include; • Authentication Attacks • Password guessing using common strings or using default passwords • Ex: Wireless Routers have default passwords Majority don’t change this!!! • Ex: Windows Administrator Account are often blank • Password Brute Force Attack • These method has become extremely fast with the of Rainbow Tables! • Rainbow tables pre-computed tables of password hashes. • Social Engineering Attacks • To influence someone into divulging confidential information using techniques. • Ex: Phishing Attacks • A malicious user who impersonates him or herself as trustworthy a entity • SQL Injection Attacks • To inject unexpected malformed SQL into a query in order to manipulate the database in unintended ways. • Ex: Injection of SQL to spit out information from certain tables • Ex: Inject an administrator account for yourself
Many Attack Vectors! • However, one of the most dangerous and yet a very effective attack used by malicious users today areSoftware Exploitation Attacks! Software Exploitation Attacks can be used to gain access to unauthorized systems, leverage user account privileges, crash systems or provide installation of malicious software (such as Spyware, Virus’s, Trojans, Adware, etc.) without the awareness of the other party.
Understanding S.E. Attacks. • First, let’s understand basics. • According to Wikipedia; “The word vulnerability, in computer security, refers to a weakness in a system allowing an attacker to violate the confidentiality, integrity, availability, access control, consistency or audit mechanisms of the system or the data and applications it hosts” • To Software Developers, a bug is synonymous to a vulnerability. • Ex: Errors in program’s source code or flawed program design • Buffer overflows • Memory leaks • Dead locks • Arithmetic overflow • Accessing protected memory (Access Violation)
Understanding S.E. Attacks • Regardless though which type of software bug we are speaking of, they are used as the foundation to form an exploit. • Therefore, an exploit is a security attack on a vulnerability. • In other words (again), an exploit attacking a vulnerability is generating an event that the application/program/OS is not programmed/designed to recover successfully and therefore the result is a system that discontinues to function correctly • How will this give us access to a secured System? Ans: It won’t. • Each exploit can be designed to meet the methodology of your attack. • Ex: An attacker exploits an IDS to reboot it or crash it before he/she launches a further attack to avoid detection.
Understanding Payloads • However, Exploits have more potential! • They are commonly used to install system malware or gain system access or recruit client machines into an existing ‘botnet’. • This is accomplished with the help of a payload • The payload is a sequence of code that is executed when the vulnerability is triggered • To make things clear, an Exploit is really broken up into two parts, like so; EXPLOIT = Vulnerability + Payload;
Understanding Payloads • The payload is usually written in Assembly Language • Platform and OS dependant. • A Win32 payload will not work in Linux (even if we are exploiting the same bug) • Big Endian, Small Endian Architectures • Different payload types exist and they accomplish different tasks • exec Execute a command or program on the remote system • download_exec Download a file from a URL and execute • upload_exec Upload a local file and execute • adduser Add user to system accounts
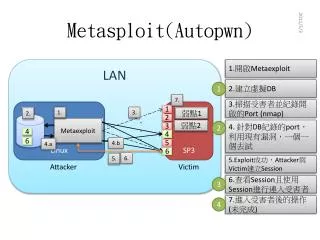
Understanding Payloads • However, the most common payload type used with exploits are shellcodes or aka shell payloads. • These payloads are very useful because they provide the attacker an interactive shell that can be used to completely control the system remotely • The term is inherited from Unix /bin/sh • For Win OS’s, shells actually refer to command prompt cmd.exe • There are two different types of shell payloads; • Bind Shells A socket is created, a port is bound to it and when an a connection is established to it, it will spawn a shell. • Reverse Shells Instead of creating a listening socket, a connection is created to a predefined IP and Port and a shell is then shoveled to the Attacker.
Metasploit Framework What is the Metasploit Framework? • According to the Metasploit Team; “The Metasploit Framework is a platform for writing, testing, and using exploit code. The primary users of the Framework are professionals performing penetration testing, shellcode development, and vulnerability research.”
Understanding MSF • The MSF is not only an environment for exploit development but also a platform for launching exploits on real-world applications. It is packaged with real exploits that can provide real damage if not used professionally. • The fact that MSF is an open-source tool and provides such a simplified method for launching dangerous attacks, it has and still is attracting wannabe hackers and script kiddies that do no more than create additional problems on networks and system.
Part II – Snort Introduction • A problem exists will large networks • Without proper equipment, it becomes more difficult for Administrators and Analyst's to continuously keep track of the security and integrity of their network. This is true because larger network have more potential areas to be targeted and therefore detection of attacks become a challenging task. • What are Network Intrusion Detection System’s? • This is proper equipment • It is technology that has been designed to automatically detect malicious content on a network and provide the administrator with a response in the event of a problem.
Understanding Snort • Simply, Snort is an open-source Intrusion Detection System (IDS) and an Intrusion Prevention System (IPS) technology. • Meaning it will monitor our networks traffic for malicious content to determine if there is a problem and it will also take immediate action if it detects a problem • Snort can perform real-time analysis on packet streams to detect many variations of attacks and probes. Such attacks and probes include, as listed on snorg.org, are buffer overflows, stealth port scans, CGI attacks, SMB probes, OS fingerprinting attempts, and much more. • Snort is also a real-time alerting agent. • Example: Snort can be configured to send Bob an e-mail when a low-priority attack is detected but send Joe a pager notification when a high-priority attack is detected.
Snort Installation/Configuration • Installation easy! • Requires WinPcap libraries • However, configuration is not so easy • Required manual modifications to snort.conf • Difficult to debug • IDScenter makes snort configuration much easier! • http://www.engagesecurity.com/products/idscenter/ • In a nutshell, IDScenter is a front-end GUI for the snort.conf configuration file • IDScenter also includes; • snort.conf testers • No worries about syntax • Alert file viewer
IDScenter Configurations Figure: IDScenter Main Panel
IDScenter Configurations Figure: Initialize Environment Variables
IDScenter Configurations Figure: Added Bleeding Edge Threats Rulesets
The Attack Experiment Goal: • To conduct a Software Exploitation Attack using Metasploit Framework against a Victim machine in order to gain system access • To make things interesting, the Victim’s machine will also have Snort running locally as an IDS in order to see how it reacts to the attack.
Software Details • Victim(*No anti-virus or similar scanner is running on this machine) • Operating System: Windows XP Professional 5.1.2600, Service Pack 2 (not fully updated) • Snort 2.7.0 • Attacker • Operating System: Slackware Linux via BackTrack 2 Bootable Live CD • Metasploit Framework 3.0 – Beta Development Release
Vulnerability Details • Microsoft Security Bulletin - MS06-001 Vulnerability in Graphics Rendering Engine Could Allow Remote Code Execution (912919) • Originally posted on January 5, 2006 • However, it was running wild as a 0-Day vulnerability for a couple weeks • The heart of the vulnerability was within ‘Graphics Rendering Engine’ of the OS; where a problem would occur whenever it handled corrupted Windows Metafile images. This is was not typical buffer overflow problem but merely a flaw in the design. • At the time, it was an extremely critical vulnerability!
Conducting the Attack Figure: Booting up Backtrack
Conducting the Attack Figure: Metasploit Command Line Interface
Conducting the Attack Figure: Exploit Selection Figure: Exploit Initialization
Conducting the Attack Figure: Payload Selection
Conducting the Attack Figure: Module and Payload Configuration
Conducting the Attack Figure: Attack launched using ‘exploit’ command
Conducting the Attack Figure: Victim Exploited
Conducting the Attack Figure: Successful attack opens remote control session Figure: Active sessions
Conducting the Attack Figure: System Access ! Figure: ‘ipconfig’ executed on Victim’s machine
References [1] “Software Bug” URL: http://en.wikipedia.org/wiki/Computer_bug [2] “Computer Security” URL: http://en.wikipedia.org/wiki/Computer_security [3] “Exploit (computer security)” URL: http://en.wikipedia.org/wiki/Exploit_(computer_security) [4] “BackTrack Security Live CD” URL: http://www.remote-exploit.org/ [5] “Metasploit Framework” URL: http://www.metasploit.com/ [6] “Snort” URL: http://www.snort.org/ [7] “WinPcap” URL: http://www.winpcap.org/ [8] “IDScenter” URL: http://www.engagesecurity.com/products/idscenter/ [9] ” Bleeding Edge Threats” URL: http://www.bleedingthreats.net/ [10] “Microsoft Security Bulletin MS06-001” URL: http://www.microsoft.com/technet/security/bulletin/MS06-001.mspx