The Ultimate Guide to Finding and Exploiting Admin Systems in SecurityCenter
Learn how to identify and exploit vulnerable admin systems using SecurityCenter. Discover plugins and dynamic assets to identify exploitable systems and vulnerabilities easily. Combine assets to get comprehensive insights for remediation.

The Ultimate Guide to Finding and Exploiting Admin Systems in SecurityCenter
E N D
Presentation Transcript
Finding Exploitable Admin Systems A “How To” Guide for SecurityCenter
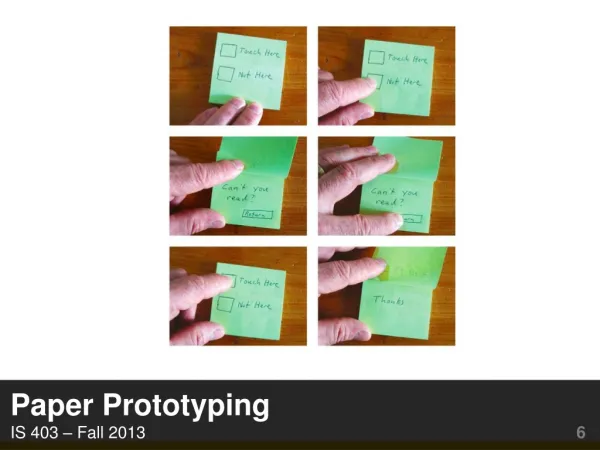
Exploitable Admin Systems • If the hosts used to administer the network are vulnerable, then a malicious entity can exploit them to compromise the entire network! • How can SecurityCenter be used to find hosts that are used to administer other systems ANDthat also have exploitable vulnerabilities?
Find Administrative Systems • Plugin 800041, User Source Summary • Plugin output gives list of user accounts that have logged into remote systems from this host • If output contains 'root', 'Administrator', or another Windows management account name, then it is likely that this host was used to administer other systems on the network
Find Administrative Systems • Use dynamic asset: Admin Systems • Available in feed by selecting category Collected Data, and then selecting tags admin or root
Find Administrative Systems • If the Windows management account has been renamed from ‘Administrator’ to something else, text search clauses can be added in the asset.
Find Exploitable Systems • Hosts that for at least one vulnerability detected, plugin text indicates that an exploit is available for the vulnerability, or that an exploit framework (such as Metasploit) can exploit the vulnerability.
Find Exploitable Systems • Use dynamic asset: Exploitable (Generic) • Available in feed by selecting category Vulnerabilities, and then selecting tag exploitable
Find Exploitable Admin Systems • Now use a combination asset to find systems that are both administrative AND exploitable
Find Exploitable Admin Systems • This new combination asset can be used in dashboards and reports, to display for example: • Top vulnerabilities on admin systems (Vulnerability Summary) • Top exploitable admin systems (IP Summary) • Top remediationsfor admin systems (Remediation Summary) • And more!
Combination Assets • Combination assets(assets of assets) can be used to locate systems that belong to both one group AND another group, or that belong to one group OR another group • For example, the Exploitable (Generic) asset could be combined with other dynamic assets to find the systems in those groups that are exploitable • Combination assets are dynamically updated, so any network changes are immediately reflected
For Questions Contact Tenable Customer Support Portal