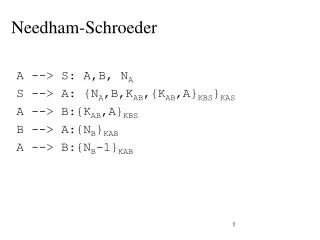
Needham-Schroeder
Needham-Schroeder. A --> S: A,B, N A S --> A: {N A ,B,K AB ,{K AB ,A} KBS } KAS A --> B: {K AB ,A} KBS B --> A: {N B } KAB A --> B: {N B -1} KAB.

Needham-Schroeder
E N D
Presentation Transcript
Needham-Schroeder A --> S: A,B, NA S --> A: {NA,B,KAB,{KAB,A}KBS}KAS A --> B:{KAB,A}KBS B --> A:{NB}KAB A --> B:{NB-1}KAB
Consider the following protocol for user authentication. Alice and the host share a secret key KA which is initially communicated out of band. After that, every time Alice wants to log on she uses the following protocol: • Alice sends to the host her ID and a nonce R1 (a nonce is a non repeatable random number). • The host returns a nonce R2 and also the encrypted nonce R1 using the secret key that the host shares with Alice, that is EKA(R1). • Alice returns EKA(R2). • Is the above protocol susceptible to a replay attack? Explain your answer. • Show how the above protocol is susceptible to a reflection attack.
A user community uses a trusted third party Trent, who keeps a database of all the participants’ public keys. Also, all participants have a trusted copy of Trent’s public key. When Alice needs to communicate with Bob: • Alice sends a message to Trent with her identity and Bob’s identity: A,B. • Trent sends Alice Bob’s public key KB, signed with Trent’s private key. Trent also send Alice her own public key, KA signed with his private key: ST(B,KB), ST (A,KA). • Alice sends Bob a random session key and a time-stamp, signed with her private key and encrypted with Bob’s public key, along with signed public keys: EB(SA(K, TA)), ST (B,KB), ST (A,KA). • Bob decrypts Alice’s message with his private key and then verifies Alice’s signature with her public key. He checks to make sure that the time stamp is still valid. • At this point both Alice and Bob have the session key K and can communicate securely. The problem with the above protocol is that Bob, after completing the protocol with Alice can immediately turn around and pretend to be Alice. Explain how this can be done and what can be done to prevent it.