Integer Factorization Problem
Integer Factorization Problem. Salman Cheema 9 th April 2009. Outline. Cryptography & Number Theory RSA Integer Factorization Problem Complexity Q&A. Private Key Cryptography. Been in use for the last few thousand years.

Integer Factorization Problem
E N D
Presentation Transcript
Integer Factorization Problem Salman Cheema 9th April 2009
Outline • Cryptography & Number Theory • RSA • Integer Factorization Problem • Complexity • Q&A
Private Key Cryptography • Been in use for the last few thousand years. • Everyone uses the same secret key for encryption and decryption. • Issues • Key leaked => broken security. • Impersonation is possible. • How to distribute the key securely? • Knowledge of the algorithm usually allows an attacker to guess the key.
Public Key Cryptography • Introduced by Diffie & Hellman in 1976. • Most significant paradigm shift in a few thousand years. • Features • Each user has two keys (a public key and a private key) • The algorithm is public knowledge. • Knowledge of the algorithm does not help an attacker.
Requirements for PKC • Anyone can quickly encrypt messages for A using his public key. • Only A can quickly decrypt messages. • It must be hard for anyone else to decrypt messages intended for A in a reasonable amount of time. • (3) guarantees security. • Also implies the need for computationally hard problems.
Number Theory Stuff • Prime Numbers • Integers that have no positive factors except themselves and 1. • Composite Numbers • Integers that have at least one non-trivial factor except themselves and 1. • Co-prime or Relatively Prime • Two integers a and b are co-prime iff GCD(a, b)=1. • GCD(a, b) = Largest integer that completely divides both a and b. • Euclid’s algorithm can be used to compute GCD.
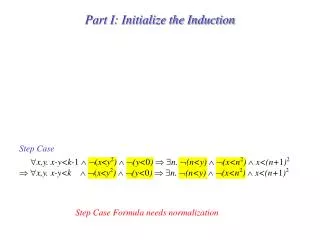
More Number Theory • Euler’s Totient function • ɸ(n) = Count of numbers < n that are co-prime to n • If n is prime • ɸ(n) = n-1 • If n is composite (e.g. n=p . q) • ɸ(n) = ɸ(p . q) = ɸ(p).ɸ(q) = (p-1).(q-1) • p and q must be co-prime. • Euler’s Theorem • Given a number n, ∀a ∈ {1, 2, 3,…., n-1} • GCD(a, n)=1 => aɸ(n) mod n = 1
RSA • Invented by Rivest, Shamir & Adleman in 1978. • Public key cryptosystem based on the Integer Factorization problem. • Very Popular • One of the first to support Digital Signatures.
RSA – Key Generation • Every user • Picks two large random prime numbers (p, q) • Computes n = p . q • Computes ɸ(n) = (p-1).(q-1) • Picks a random integer e • 1 < e < ɸ(n) • GCD(ɸ(n),e) = 1 • Computes d = e-1mod ɸ(n) • Public Key = (n, e) • Secret Key = (ɸ(n),d)
Encryption/Decryption • Encryption (raise M to the eth power in mod n) • C = Memod n • Decryption (raise C to the dth power in mod n) • M = Cdmod n • Works because e & d are inverses • e.d = 1 mod ɸ(n) => e.d = 1 + k.ɸ(n) • (Me)dmod n • = (M)1+ k.ɸ(n) mod n • = M(Mk)ɸ(n) mod n = M mod n
Breaking RSA • Public knowledge = (n, e) • Secret knowledge = (ɸ(n), d) • d cannot be computed without knowing ɸ(n). • Recall that d=e-1 mod ɸ(n) • An attacker must compute ɸ(n) given only n. • Need to factorize n into its prime factors.
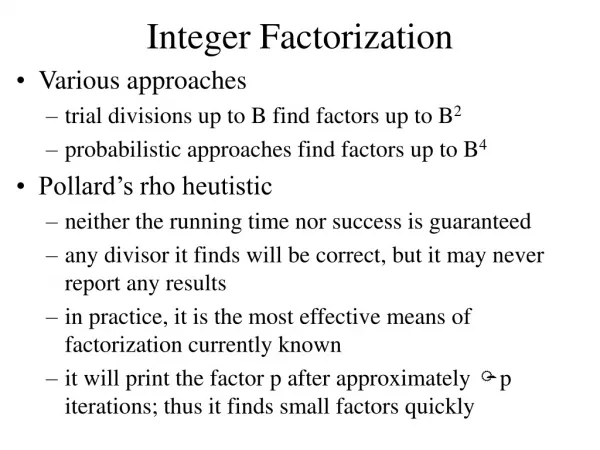
Integer Factorization • Stated as a search problem • Given an integer n, find its prime factors. • Brute-force approach • For ∀ 2 ≤ si ≤ √n, Verify if si divides n. • Need to consider at most √n numbers for division. • Using k-bits => 2k/2 possibilities. • Given a 150-bit number and a PFLOPS capable supercomputer, time needed ≈ 1 year • RSA typically uses ~ 1000 bits for its numbers.
Congruence of Squares • To factorize N, choose numbers a, b that satisfy • a2 ≡ b2 mod N • a ≢ ±b mod N • N divides (a-b)(a+b) but neither (a-b) nor (a+b) • either (a+b) or (a-b) should have a factor in common with N. • Compute GCD(a±b, N) to find factor. • The trick is how to quickly come up with suitable a,b. • Most efficient known algorithm is General Number Field Sieve. • For a b-bit integer, runtime is O(e(c(∛b)(∛(log b)²)) • Current Record: in November 2005, a 640-bit integer was factored in 5 months. (www.rsalabs.com)
Integer Factorization • Integer Factorization as a Decision Problem, • Given two integers A, k • Does there exist a prime number p such that • 2 ≤ p ≤ k • p completely divides A. • “YES” instance => we can find a prime number p that satisfies the above requirements • “NO” instance => we cannot find any prime number that satisfies above requirements.
Complexity • Clearly Integer Factorization is in NP. • Witness: An Oracle provides the factor p. • Verify that p is prime AND 2 ≤ p ≤ k • Verify that p is a factor of n. • Also in Co-NP • Witness: An Oracle provides all prime numbers < k • Verify that each is indeed prime. • Verify that none of them completely divide n. • Integers can be tested for primality in polynomial time. [Agarwal et al 2002]
Is it NP-Complete? • Unknown • What if it is NP-Complete? • Its complement will be Co-NP Complete. • ∀p ∈ NP, p ⇨ Integer Factorization • Therefore NP ⊆ Co-NP • ∀pc ∈ Co-NP, pc ⇨ (Integer Factorization)c • Therefore Co-NP ⊆ NP • ergo Co-NP = NP
What if it’s not polynomial • Suppose the best possible algorithm for Integer Factorization is exponential. • It follows that P != NP • A problem exists in NP that does not have a polynomial algorithm. • But if it is polynomial, tough luck • Cannot say anything about “P=NP?” • Will break RSA in its current form though.
Conclusion • Integer Factorization lies in NP, but we don’t know exactly how hard it is. • The best known algorithm (given classical computers) runs in exponential time. • In 1994, Peter Shor invented a Quantum Computing Algorithm for factorization. • Runs in O(b3) time and needs O(b) storage for a b-bit integer. • Tested in 2001 using Quantum Computer with 7 q-bits. Factorized 15 into 3 and 5. (Wikipedia)
References • Arjen K Lenstra, Integer Factoring, Designs, Codes and Cryptography, 19, 101–128 (2000) • Jorg Rothe, Some Facets of Complexity Theory and Cryptography: A Five Lecture Tutorial, ACM Computing Surveys, Vol. 34, No. 4, December 2002, pp. 504–549 • Manindra Agrawal, Neeraj Kayal, Nitin Saxena, "PRIMES is in P", Annals of Mathematics 160 (2004), no. 2 • RIVEST, R., SHAMIR, A., AND ADLEMAN, L. 1978. A method for obtaining digital signature and public-key cryptosystems. Commun. ACM, 21, 2 (Feb.), 120–126, pp. 781–793 • Neal Koblitz, A Course in Number Theory and Cryptography, 2nd Edition, Springer-Verlag 1994