Understanding ID-WSF: Architecture, Benefits, and Interactions in Identity Web Services
This document explores the key components, protocols, and design principles of ID-WSF (Identity Web Services Framework). It outlines the interaction model involving users, identity providers (IdPs), and service providers (SPs). The document emphasizes the importance of user-centric design, secure identity data transactions, and modular system architectures for application development. Additionally, it covers the app-to-app interactions and highlights major benefits such as privacy, flexibility, and dynamic service discovery. The document also provides a real-life example to illustrate the practical application of ID-WSF principles.

Understanding ID-WSF: Architecture, Benefits, and Interactions in Identity Web Services
E N D
Presentation Transcript
Preparation for External Submission of ID-WSF components ID-WSF Basics
The human-to-app story • Single sign-on, single logout, etc. take place among: • The user (with actions mediated by a client of some kind) • An identity provider (IdP) • A service provider (SP) that serves as a relying party (RP) • These actions are communicated primarily with XML over HTTP(S)
Why app-to-app interaction? • Get around browser payload limitations • Allow identity-enabled actions to happen silently (mediated by policy) when you're not around • All the way from pay my bills automatically... • ...to let the emergency-room doctor access my medical records from another country if I'm in a coma • Allow multiple services to cooperate securely • Providing both personalization and access control • To achieve this, ID-WSF uses SOAP-based protocols
Design goals • A standards-based architecture for identity web services • Ecosystems of services that expose interfaces onbehalf of individual users' identities • A flexible foundation layer for application development • Across security domains and computing platforms • Across time, allowing for service location flexibility • The option of maximum privacy and security • Identity information requests access-controlled • Minimal disclosure of identity information • Protection against disclosure of identifiers
High-level ID-WSF protocol architecture • Makes use of existing standards wherever appropriate • All infrastructure components and foundational services can be replaced by your own • At some cost to interoperability, naturally • Extensibility and modularity are built in to let you easily create your own identity-based services
Major benefits of ID-WSF's design • Authentication, authorization, and application of usage policy against consumers of identity data • User privacy through use of pseudonyms • Dynamic service discovery and addressing • Common web services transport mechanisms to apply identity-aware message security • Abstractions and optimizations to allow anything – including client devices – to host identity services • Unified data access/management model for developers • Flexibility to develop arbitrary new services • Support for social identity applications
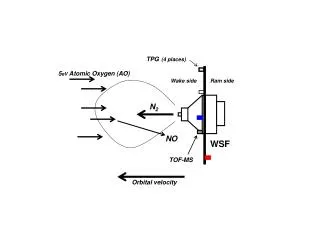
Kicking off an app-to-app interaction • It usually starts with a user (possibly not you!) logging in and asking for some service behavior involving your identity • During SSO, the IdP informs the SP where to find yourDiscovery Service (DS) • A hub for locating, and possibly getting coarse-grained authorization to use, various identity services of yours • In a typical deployment, the IdP and DS form one tightly coupled software component
The locate-and-access dance WSC...of identity data • The SP dons the role of a web service consumer (WSC) • A WSC is the requestor endpoint, and a web service provider (WSP) is the responder endpoint • Tip: Mentally add “of identity data” to remember which is which • The WSC asks the DS where a particular WSP is, and asks for access • WSPs will typically do fine-grained WSC authorization themselves • One example of a WSP is the ID-SIS Personal Profile (PP) service for name, address, etc. WSP...of identity data
Getting information-sharing approval • What if the PP service needs to check with you before responding? • It can ask your DS where to find an Interaction Service (IS) for youso it can bother you real-time • According to your own policypreferences for what's importantenough to bother you with • The PP is acting as a WSC • Doing the locate-and-accessdance itself, just likeBuyPuppyStuff did • The IS uses non-Liberty meansto (e.g.) SMS you for approval Now it's a WSC (...of identity data) in turn
Observations • These logical components were included for maximum privacy and flexibility, but not every deployment needs them all! • And the worst case is still optimized so that devices sensitive to “protocol chattiness” can handle it • Any identity service can “recursively” use the discovery and access system provided by the DS to call another one • At any point a service can (attempt to) contact the user for informed consent, policies, more attributes... • Throughout, the user might be known only by a pseudonym
Real-life example 2: Radio@AOL(credits: Conor Cahill and John Kemp) • The ultimate in user control: your personal device serves up your preferences And oh, by the way –a WSP (...of identity data) A Liberty-enabled User Agent or Device (LUAD)
ID-WSF architecture piece-parts Submission package Legend: Kantara standard External standard Third-party (possibly a standard)
Discovery Service • Registry for services associated with an identity • Identity services are registered at the DS so that Identity requestors can subsequently discover them • Allows for multiple providers of the same service • Allows for data specific discovery • Retrieve the geolocation service that has a particular accuracy • Retrieve the profile service that has an age
Security Mechanisms • Defines combinations of message & transport level security protections for WSF protocol messages • WSC & WSP can 'negotiate' which combinations to use for given transactions
SOAP Binding • Binds abstract WSF protocol messages to SOAP header & payload
Additional features: Service invocation and message construction Security policy Identity mapping mechanisms Identity provider services Major features of ID-WSF • Bootstrapping from SSO • Service discovery • User interaction • Smart clients • Web service identity model • Privacy mechanisms • Person-to-person federation • Design patterns for common development tasks
Web service identity model • A model for carrying the identity of various parties to a transaction within web service messages • Sender (human) • Recipient • Invoker (service on behalf of human) • Target identity owning the resource (human) • In querying for your own mail from an email service, you are the target identity • In looking up your colleague's calendar, your colleague is the target identity • WS-Security SOAP headers and SAML assertions are profiled to carry this info in “identity tokens”
Privacy mechanisms • Ensuring that your data is shared on your terms by: • Capturing your usage directives and consent status in service messages • Allowing for interaction with you at critical junctures to obtain your consent and privacy policies • Interaction Service, Interaction Redirect • Inhibiting correlation of your activities by: • Offering different pseudonyms to different parties • Identity Mapping Service • Protecting your data in transit • WS-Security for confidentiality
Design patterns for development • Many identity services at the ID-SIS layer need: • Provisioning, retrieval, and ongoing updates of identity data (“CRUD” – create, retrieve, update, delete) • Subscription and subsequent notification if something changes • Templates and guidelines are provided for rapid service development offering these common features
Major open-source implementations • Sun's http://OpenSSO.dev.java.net • SAML, ID-FF, ID-WSF in Java; SAML in PHP (“Lightbulb”) • Entrouvert's http://LaSSO.Entrouvert.org • SAML, ID-FF, ID-WSF in C with SWIG bindings for Python, Perl, Java, PHP • Symlabs' http://ZXID.org • SAML, ID-FF, ID-WSF (and WS-Fed) in C with Perl/PHP wrappers • Conor's http://www.cahillfamily.com/OpenSource/ • ID-WSF C client and Java server • Keep an eye on http://www.openLiberty.org!
TEG Progress Update ID-WSF Basics Questions?