Top 5 Web Application Security bugs in custom code
Explore the critical web application security vulnerabilities identified by Microsoft’s ACE Team, detailing the top five issues: Cross-Site Scripting, Clear Text Secrets, Authorization Issues, SQL Injection, and Verbose Error Messages. Each vulnerability is discussed with its impact, examples of common buggy code, and recommended countermeasures to enhance security. This presentation provides essential insights for developers and security engineers focused on safeguarding their applications and ensuring robust protection against potential attacks.

Top 5 Web Application Security bugs in custom code
E N D
Presentation Transcript
Top 5 Web Application Security bugs in custom code Varun Sharma Security Engineer | ACE Team | Microsoft Information Security varun.sharma@microsoft.com
Top 5 Web App Security bugs Relative percentage of the Top 5 Web Application Security vulnerabilities found by Microsoft ACE Team since 1st Jan 08
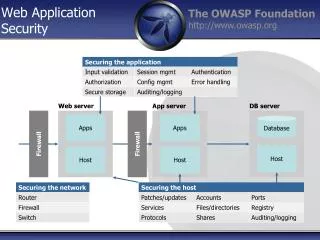
Agenda • Cross-Site Scripting • Clear Text Secrets • Authorization Issues • Disabling Controls in the Web site to enforce authorization • Direct Object Reference • Missing Authorization controls in web services • SQL Injection • Verbose Error messages
Cross-Site Scripting • User controlled input is rendered back to browser without sufficient input validation or output encoding • Leads to execution of script (controlled by the attacker) under the context of the victim
Cross-Site Scripting • Normal execution
Cross-Site Scripting • What attacker does
Cross-Site Scripting • Common Buggy Code • Some ASP.NET Controls encode and some do not
Cross-Site Scripting • Common Buggy Code • Some ASP.NET Controls encode and some do not
Cross-Site Scripting • User input going in attribute context • User input going in JavaScript context
Cross-Site Scripting • Countermeasures • Validate all input and encode all output • Perform context specific encoding • Use the AntiXss Library
Clear Text Secrets • The application may need to store credentials to connect to SQL Server, SMTP Server etc • May need to store symmetric keys to perform encryption of application data • May be storing user passwords or other secret information in the database
Clear Text Secrets • Common bugs
Clear Text Secrets • Common bugs
Clear Text Secrets • Countermeasures • Do not store secrets (passwords/ keys) in code • Use the aspnet_regiis tool to encrypt configuration settings • For application specific data, consider using SQL Server 2005/ 2008 Native Encryption
Authorization Issues • Disabling Controls in the Web site to enforce authorization (Normal execution)
Authorization Issues • Disabling Controls in the Web site to enforce authorization (What attacker does)
Authorization Issues • Disabling HTML text boxes, buttons in only a visual indication, not a security control • Need to perform explicit authorization checks on the server side
Authorization Issues • Common Buggy Code
Authorization Issues • Direct Object Reference (Normal execution)
Authorization Issues • Direct Object Reference (What attacker does)
Authorization Issues • Direct Object Reference • Unique identifier is used to retrieve and update data for an object. This unique identifier is an incrementing integer (or easily available). • No explicit authorization check is performed to ensure current user has access to the object.
Authorization Issues • Missing authorization in web services in multi- tier applications Web Server SQL Server Web Server (Website) (Web service) (Database)
Authorization Issues • Countermeasures:- • Perform server side authorization • Use a platform provided authorization mechanism • URL Authorization • Declarative and Imperative checks • Implement authorization controls in middle tiers
SQL Injection • User input without sufficient validation is used to create and execute a dynamic SQL statement • User can manipulate the SQL statement that gets executed
SQL Injection • Normal execution
SQL Injection • What attacker does
SQL Injection • Common buggy code
SQL Injection • Common buggy code
SQL Injection • Countermeasures:- • Validate all input • Use parameterized SQL statements (in stored procedures as well, using sp_executesql) • Configure SQL server with least privilege for defense in depth
Verbose Error messages • Detailed error messages reveal inner workings of an application and make an attackers job easier
Verbose Error messages • Common Buggy Code:-
Verbose Error messages • Common Buggy Code:- • Missing exception handling in ASMX web services
Verbose Error messages • Leads to…
Verbose Error messages • Common Bad Configuration:-
Verbose Error messages • Leads to…
References • AntiXss Library http://www.microsoft.com/downloads/details.aspx?familyid=efb9c819-53ff-4f82-bfaf-e11625130c25&displaylang=en • ASP.NET IIS Registration Tool (Aspnet_regiis) http://msdn.microsoft.com/en-us/library/k6h9cz8h(VS.80).aspx • ASP.NET Authorization http://msdn.microsoft.com/en-us/library/wce3kxhd(VS.80).aspx • Using sp_executesql http://msdn.microsoft.com/en-us/library/ms175170.aspx
Feedback / QnA • Your Feedback is Important! Please take a few moments to fill out our online feedback form • Use the Question Manager on LiveMeeting to ask your questions now!
Contact • Blog http://blogs.msdn.com/varun_sharma • Email Address varun.sharma@microsoft.com