What is Data Security Posture Management
Learn how Data Security Posture Management (DSPM) helps organizations assess, protect, and strengthen data security across various environments.

What is Data Security Posture Management
E N D
Presentation Transcript
Protect Your Enterprise Data with DSPM PEnsuring Data Security in a Complex Digital World
Introduction: The Growing Threat of Data Breaches Every second a data breach occurs globally. Data breaches can damage reputation, and finances, and lead to legal consequences. Challenge: Managing data security in today’s complex, distributed environments (cloud, devices, SaaS).
What is Data Security Posture Management (DSPM)? DSPM = A continuous process to assess, identify, and improve data security. Proactive Approach: Focuses on preventing breaches, not just reacting. Key Goal: Know where sensitive data is, who accesses it, and how it's protected.
Why DSPM is Essential for Your Business? Data Sprawl: Sensitive data is spread across cloud, on- prem, and personal devices. Hidden Data Risks: “Shadow data” exists without visibility or protection. Compliance: Failing to meet privacy regulations (e.g., GDPR) leads to fines. Security Gaps: Misconfigurations make data vulnerable to attacks.
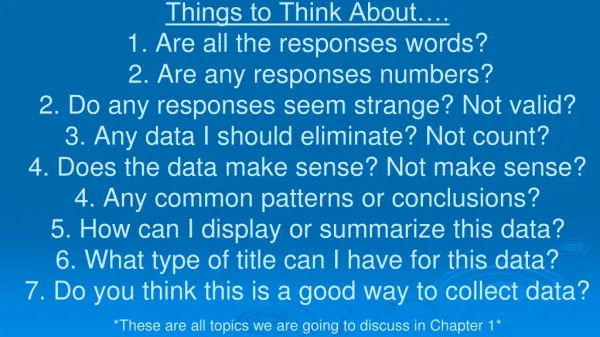
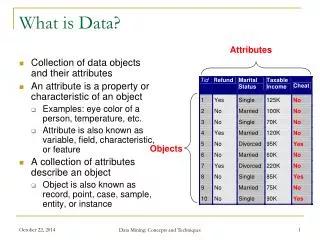
Key Capabilities of DSPM Data Discovery & Classification: Automatically scans and sorts sensitive data. Vulnerability Assessment: Identifies security weaknesses like misconfigurations. Remediation & Prioritization: Helps fix issues and prioritize risks. Continuous Monitoring: Ongoing surveillance to maintain data security. Compliance Reporting: Automates audits and shows regulatory compliance.
HawkShield’s DSPM Solution? AI-Powered Protection: Discover, classify, and secure your data effortlessly. Zero-Trust Access: Ensures only authorized personnel access sensitive data. Real-Time Data Flow Tracking: Map data movement to prevent unauthorized access. Compliance & Risk Minimization: Automate compliance and breach preparedness. Secure Your Data Now with HawkShield
ContactUs: HawkShield HawkShield. Singapore. Visit Us: https://www.hawkshield.ai/