Computer Crimes
Computer Crimes . Wikipedia. World-wide data base of information that can be edited by anyone Uses programs to monitor malicious behavior Effective? Ex: 2008 Presidential Election. What Is Crime?. It is define: instance of negligence injurious to the public welfare or morals

Computer Crimes
E N D
Presentation Transcript
Wikipedia • World-wide data base of information that can be edited by anyone • Uses programs to monitor malicious behavior • Effective? • Ex: 2008 Presidential Election
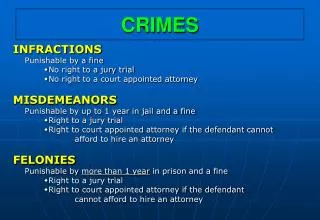
What Is Crime? • It is define: • instance of negligence • injurious to the public welfare or morals • Ex: Murder, Stealing, Breaking and Entering
What Would You Do? • Example: You are sitting in your classroom when… • You see a man outside mugging an old lady AND • You see a random person in the corner smugly typing on his computer Who would you go to first and why?
How Does Crime Interact with Technology? • Also called “Cyber Crimes” • Defined as: • the use of information technology for illegal purposes • unauthorized access of a computer system • damage, delete or alter the data present in the computer.
Genres of Computer Crimes 1.) New Versions of old crimes ex: Theft, Fraud, Stalking, Libel, and Defamation 2.)Crimes that couldn’t exist without computers or are directed at computers ex: Virus, Denial-of-Service Attack, and Inappropriate Pinging
Which Is Worse? • Example: Child Pornography v. Rape • Pornography is one of the most frequent computer crime to date • Every second - 28,258 Internet users are viewing pornography • 3% of college women nationally have experienced rape or attempted rape during the academic year. • Ex: A campus with 6,000 coeds will have an average of one rape per day during the school year.
Hacking • In olden days, considered to be computer enthusiasts who found new things to do with technology • Now, refers to those who use computers for illegal actions such as unauthorized access to computer systems and stealing proprietary software.
Examples of Hacking Robert T. Morris Jr.- Created the most invasive computer worm that spread across the internet. Attempted to show security flaws, but had its own flaw which enabled people from stopping it. Charged with violating Federal Computer Fraud and Abuse Act and suspended from Cornell.
Is Hacking Ever Good? • Ex: Wikileaks • “The founder of whistleblowing website Wikileaks has defended the release of almost 400,000 classified US documents about the war in Iraq.” (BBC News) • Video: http://www.bbc.co.uk/news/world-middle-east-11612731
Hacker Defense Discussion Topics: 1.) All Information Should be Free Give me an example of information should not be available 2.) Benificial because it illustrates security problems that can be fixed Does hacking for the purpose of government security violate either act or rule utilitarianism?
Hacker Defense cont. 3.)Gaining unauthorized access does no harm as long as hackers don’t change anything Do you believe this is true? Why? 4.)Help keep Big Brother at bay
Sextortion Example • Ex: Isanybodydown.com • People send naked pictures in • Posted to site with personal information • $250 fee to get the info and picture down • What would you do if you found your picture on this website?
Sextortion and Pornography • Sexortion is: • Sexual exploitation • Non-physical forms of coercion sexual favors • Pornography is: • Explicit portrayal of sexual encounters • Although some is legal, most frequented porn is not
Facebook and Pornography • Facebook had almost 1 billion users • 435 children were trafficked last year in Indonesia alone • 40,000-70,000 children were involved in Trafficking. Pornography, and/or Prostitution • Is Facebook a computer crime?
What About the Children? • How do we protect children from something they don’t know about? • New research suggest that the young and the old are the most vulnerable and used targets for computer criminals • http://www.wishtv.com/dpp/news/local/marion_county/cyber-crime-snapped-teens-photo-while-online
China and Technology • Limited use of internet • Google and Facebook are banned • Considered a crime if used without authorization • Are computer crimes a moral or objective and why?
How is This Ethical? • Who is hurt by computer crimes? • Fraud, viruses, extortions, identity theft, even Facebook? • Ethical Relativism- Does this change dependent on where you are?
Current Events • Ours: • Hackers in China and the Times • Financial Cyber Attacks • SnapChat • Yours:
Punishing Computer Crimes • Should someone who steal someone’s identity have the same penalty as someone who goes in and steals from a bank? • Is one worse than the other? Why?
Solution to Problem Is There A solution? • New Laws- what type? • Website coverage and instigation- how would we do this? • Actually downloading songs from Itunes • Buying the movie or renting it- How would that affect your recreational life?