Exploring Authentication Methods & Protocols in Cryptology: A Comprehensive Overview
DESCRIPTION
Dive into the world of authentication methods and protocols in cryptology with insights from Jens Bo Friis M.Sc. from the Technical University of Denmark and the University of Aarhus. Discover the latest advancements and best practices in secure authentication for IT systems. Stay informed and ensure robust cybersecurity measures are in place.
1 / 39
Download Presentation 

Exploring Authentication Methods & Protocols in Cryptology: A Comprehensive Overview
An Image/Link below is provided (as is) to download presentation
Download Policy: Content on the Website is provided to you AS IS for your information and personal use and may not be sold / licensed / shared on other websites without getting consent from its author.
Content is provided to you AS IS for your information and personal use only.
Download presentation by click this link.
While downloading, if for some reason you are not able to download a presentation, the publisher may have deleted the file from their server.
During download, if you can't get a presentation, the file might be deleted by the publisher.
E N D
Presentation Transcript
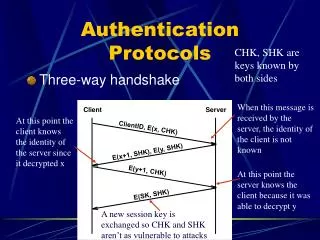
1. Authentication � methods and protocols - an overview Jens Bo Friis M.Sc. from Technical University of Denmark M. Cryptology from University of Aarhus Partner in IT Practice A/S Email: jbf@it-practice.dk
More Related